Resolve Technology
Led by Brian Wheeler who has more than 10 years of technology consulting expertise, including brand-name companies such as Siebel, Putnam Investments, Farmers Insurance, Telecom Italia and Visa International.
From configuring desktop computers, to building database servers, to designing phone systems and more, Resolve Technology has the knowledge small businesses need at prices they can afford.
Let Resolve Technology deal with your technology so you can spend more time running your business.

CMMC v2: 17 Domains with 43 capabilities
CMMC domain Capability Access Control (AC) Establish system access requirementsControl internal system accessControl remote system accessLimit data access to authorized users and processes Asset management (AM) Identify and document assets Audit and Accountability (AU) Define audit requirementsPerform auditingIdentify and protect audit informationReview and manage audit logs Awareness and Training (AT)
CMMC domain Capability Access Control (AC) Establish system access requirementsControl internal system accessControl remote system accessLimit data access to authorized users and processes Asset management (AM) Identify and document assets Audit and Accountability (AU) Define audit requirementsPerform auditingIdentify and protect audit informationReview and manage audit logs Awareness and Training (AT)
Read full post on resolvetech.biz
CMMC v2: 17 Domains with 43 capabilities
CMMC domain Capability Access Control (AC) Establish system access requirementsControl internal system accessControl remote system accessLimit data access to authorized users and processes Asset management (AM) Identify and document assets Audit and Accountability (AU) Define audit requirementsPerform auditingIdentify and protect audit informationReview and manage audit logs Awareness and Training (AT)
CMMC domain Capability Access Control (AC) Establish system access requirementsControl internal system accessControl remote system accessLimit data access to authorized users and processes Asset management (AM) Identify and document assets Audit and Accountability (AU) Define audit requirementsPerform auditingIdentify and protect audit informationReview and manage audit logs Awareness and Training (AT)
Read full post on resolvetech.biz
Yes, IT Security Is a Cost Center
IT security is a cost center but so is: Malware, ransomware, and virusesDowntime created by malware, ransomware and viruses. I know of situations where internal IT teams had to wipe all of the computers because the network had ransomware on every Windows device on the network. Lack of email hygieneSpam and phishing emails can be filtered
IT security is a cost center but so is: Malware, ransomware, and virusesDowntime created by malware, ransomware and viruses. I know of situations where internal IT teams had to wipe all of the computers because the network had ransomware on every Windows device on the network. Lack of email hygieneSpam and phishing emails can be filtered
Read full post on resolvetech.biz
Yes, IT Security Is a Cost Center
IT security is a cost center but so is: Malware, ransomware, and virusesDowntime created by malware, ransomware and viruses. I know of situations where internal IT teams had to wipe all of the computers because the network had ransomware on every Windows device on the network. Lack of email hygieneSpam and
IT security is a cost center but so is: Malware, ransomware, and virusesDowntime created by malware, ransomware and viruses. I know of situations where internal IT teams had to wipe all of the computers because the network had ransomware on every Windows device on the network. Lack of email hygieneSpam and
Read full post on resolvetech.biz
5 Functions of the NIST Cybersecurity Framework
Identify: What and who are your key people, assets, data? Protect: How will you limit key cybersecurity incidents? Detect: Can you identify breaches or incidents in a timely fashion? Respond: How will you react to incidents? Do you have plans in place? Recover: Can you recover from a cyber-incident? If you need help implementing NIST,
Identify: What and who are your key people, assets, data? Protect: How will you limit key cybersecurity incidents? Detect: Can you identify breaches or incidents in a timely fashion? Respond: How will you react to incidents? Do you have plans in place? Recover: Can you recover from a cyber-incident? If you need help implementing NIST,
Read full post on resolvetech.biz
5 Functions of the NIST Cybersecurity Framework
Identify: What and who are your key people, assets, data? Protect: How will you limit key cybersecurity incidents? Detect: Can you identify breaches or incidents in a timely fashion? Respond: How will you react to incidents? Do you have plans in place? Recover: Can you recover from a cyber-incident? If
Identify: What and who are your key people, assets, data? Protect: How will you limit key cybersecurity incidents? Detect: Can you identify breaches or incidents in a timely fashion? Respond: How will you react to incidents? Do you have plans in place? Recover: Can you recover from a cyber-incident? If
Read full post on resolvetech.biz
Who Are The Best IT Companies in New Hampshire?
Each year at Resolve Technology we speak with over 100 prospects in New Hampshire about their information technology (IT). They often ask us who are some of the other IT companies and competitors we have in the area. Not being afraid of healthy competition, we want our customers to be as informed as possible. Here
Each year at Resolve Technology we speak with over 100 prospects in New Hampshire about their information technology (IT). They often ask us who are some of the other IT companies and competitors we have in the area. Not being afraid of healthy competition, we want our customers to be as informed as possible. Here
Read full post on resolvetech.biz
Who Are The Best IT Companies in New Hampshire?
Each year at Resolve Technology we speak with over 100 prospects in New Hampshire about their information technology (IT). They often ask us who are some of the other IT companies and competitors we have in the area. Not being afraid of healthy competition, we want our customers to be
Each year at Resolve Technology we speak with over 100 prospects in New Hampshire about their information technology (IT). They often ask us who are some of the other IT companies and competitors we have in the area. Not being afraid of healthy competition, we want our customers to be
Read full post on resolvetech.biz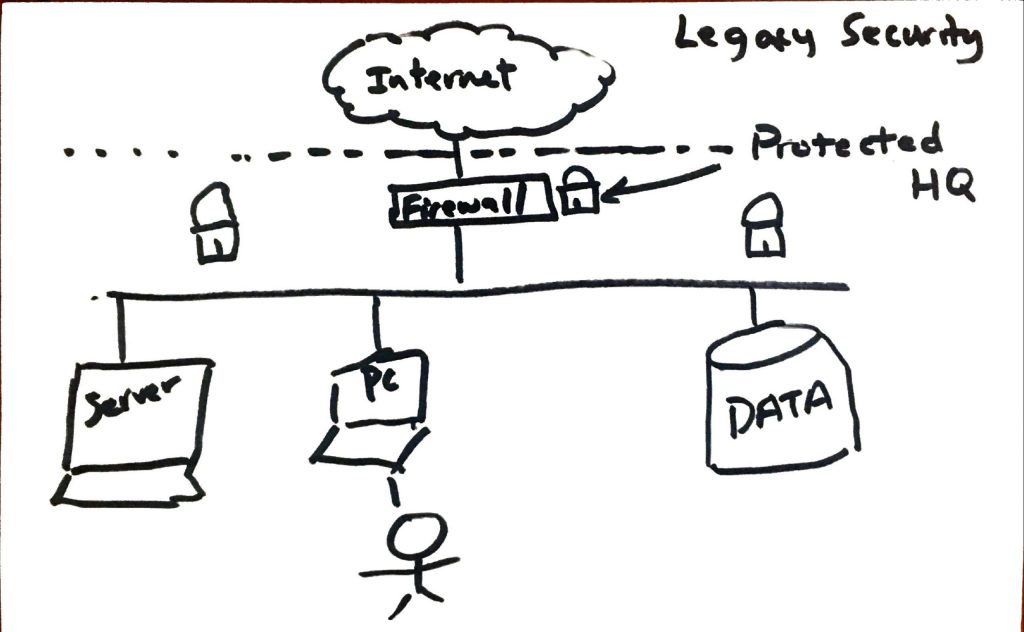
Why a Firewall Isn’t Enough?
The technology landscape has changed dramatically in the last few years. Cloud adoption and the Covid19 pandemic have moved the network perimeter from company HQ to remote locations. So how are you protecting these remote locations and endpoints? Here’s a few ways we’re doing this for clients: MFA using tools such as Google Authenticator, LastPass,
The technology landscape has changed dramatically in the last few years. Cloud adoption and the Covid19 pandemic have moved the network perimeter from company HQ to remote locations. So how are you protecting these remote locations and endpoints? Here’s a few ways we’re doing this for clients: MFA using tools such as Google Authenticator, LastPass,
Read full post on resolvetech.biz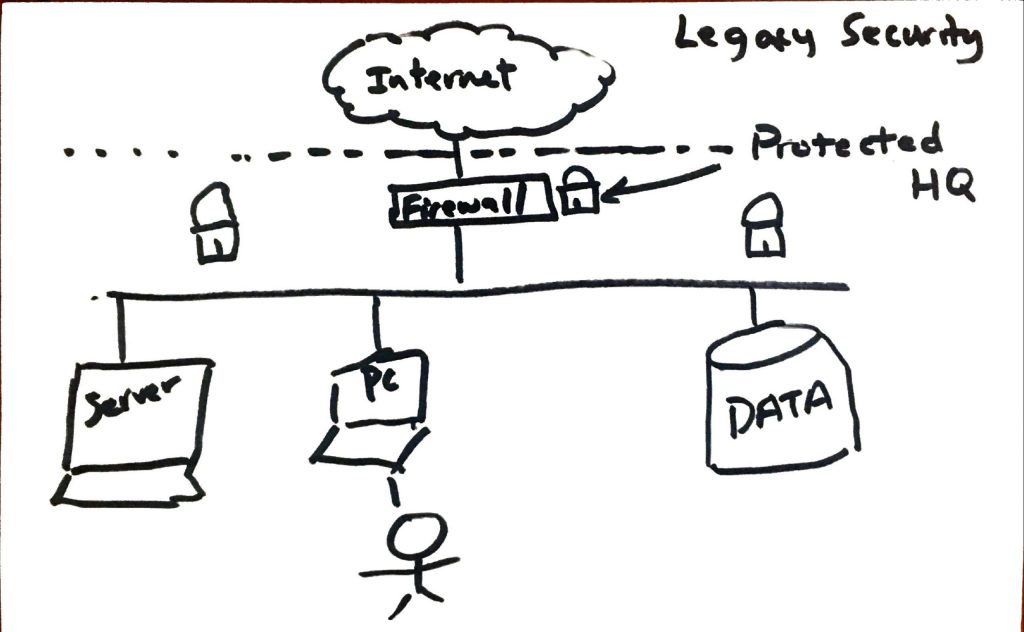
Why a Firewall Isn’t Enough?
The technology landscape has changed dramatically in the last few years. Cloud adoption and the Covid19 pandemic have moved the network perimeter from company HQ to remote locations. So how are you protecting these remote locations and endpoints? Here’s a few ways we’re doing this for clients: MFA using tools
The technology landscape has changed dramatically in the last few years. Cloud adoption and the Covid19 pandemic have moved the network perimeter from company HQ to remote locations. So how are you protecting these remote locations and endpoints? Here’s a few ways we’re doing this for clients: MFA using tools
Read full post on resolvetech.biz