StratusComm - Managed IT Services
Over the past 15 years, our clients have been able to maximize the value of their technology investments, drive down costs and greatly improve outcomes. Here are a few ways your business can benefit as well:
✔ Benefit from 24/7 responsiveness that assures your technology is working when you need it the most!
✔ Achieve significant IT cost reductions and get optimal value from the software, licenses & solutions that you use.
✔ Make decisions that inspire innovative solutions that support your organizational vision & goals!
We have worked with businesses of all types and sizes, and we understand the IT struggles that business endure. Developing an effective technology plan is not a journey you need to take alone. Contact us now to get started!

How Hackers Steal Your Passwords
Hackers are trying to devise more ways to steal your passwords and invade your privacy. Here are some of the most utilized methods they employ.
Hackers are trying to devise more ways to steal your passwords and invade your privacy. Here are some of the most utilized methods they employ.
Read full post on stratuscomm.com
Selecting the Right MSP for Your Business It’s About Much More Than Cybersecurity
Yes, cyber-security is important! If you own a small or medium-sized business, you probably field a lot of calls from Managed IT Services Providers, or MSPs. And it’s almost a sure bet that the one thing each one emphasizes is the need for cybersecurity...
Yes, cyber-security is important! If you own a small or medium-sized business, you probably field a lot of calls from Managed IT Services Providers, or MSPs. And it’s almost a sure bet that the one thing each one emphasizes is the need for cybersecurity...
Read full post on stratuscomm.com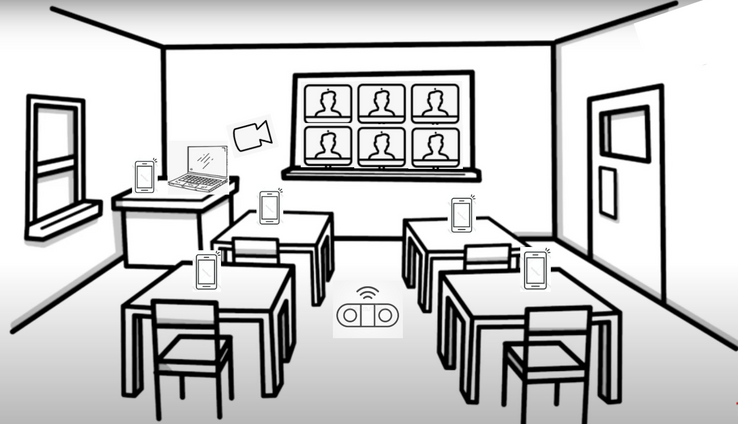
How to Set Up for a Hybrid Meeting
Due to the technical aspects involving the setup, it can be challenging to get hybrid meetings done right. Most of the regular setups only consider transmitting a general overview of the in-person meeting to the virtual attendees and vice-versa, which leads to a great disconnection between participants, low engagement, and unsatisfactory interaction...
Due to the technical aspects involving the setup, it can be challenging to get hybrid meetings done right. Most of the regular setups only consider transmitting a general overview of the in-person meeting to the virtual attendees and vice-versa, which leads to a great disconnection between participants, low engagement, and unsatisfactory interaction...
Read full post on stratuscomm.com
Is Cloud the New Normal?
Cloud-based IT systems have become an attractive solution to businesses. Instead of demanding a high up-front investment for technology, Cloud solutions are flexible and customizable, giving the agility to both scale up as well as scale down according to the business growth...
Cloud-based IT systems have become an attractive solution to businesses. Instead of demanding a high up-front investment for technology, Cloud solutions are flexible and customizable, giving the agility to both scale up as well as scale down according to the business growth...
Read full post on stratuscomm.com
The Internet is down, now what?!
You are in the middle of a video conference with that prospect you’ve been trying to reach for weeks… or about to send a crucial email with a report that must be submitted asap. Suddenly, the Internet connection is down. Now what?! We’ve all been there, let’s face it...
You are in the middle of a video conference with that prospect you’ve been trying to reach for weeks… or about to send a crucial email with a report that must be submitted asap. Suddenly, the Internet connection is down. Now what?! We’ve all been there, let’s face it...
Read full post on stratuscomm.com
How to protect against ransomware?
Ransomware is malicious and dangerous software that will infect a computer, making users unable to use it or access encrypted files until a ransom is paid. Victims are extorted to pay the ransom demands when they see an alert and are unable to access their data due to the encryption...
Ransomware is malicious and dangerous software that will infect a computer, making users unable to use it or access encrypted files until a ransom is paid. Victims are extorted to pay the ransom demands when they see an alert and are unable to access their data due to the encryption...
Read full post on stratuscomm.com
6 Tech Tips to Help Your Video Conferencing!
Although working from home can increase your productivity, having to do all your own IT work can be a downside. After all, the last thing you want is to have a technical problem right when it’s time to dial in! With that in mind, we came up with a few tech tips to help you minimize these unwanted issues and thrive in video conferencing.
Although working from home can increase your productivity, having to do all your own IT work can be a downside. After all, the last thing you want is to have a technical problem right when it’s time to dial in! With that in mind, we came up with a few tech tips to help you minimize these unwanted issues and thrive in video conferencing.
Read full post on stratuscomm.com
Best Video Conferencing Tools for your Business
As businesses find their ways in the current environment – either remote or back in the office, it is evident that video conferencing apps became an essential tool to engage in meetings, calls, and appointments. But in the midst of so many alternatives available on the web, both free and paid, it can be challenging to evaluate and decide which solution is the most appropriate to your type of business...
As businesses find their ways in the current environment – either remote or back in the office, it is evident that video conferencing apps became an essential tool to engage in meetings, calls, and appointments. But in the midst of so many alternatives available on the web, both free and paid, it can be challenging to evaluate and decide which solution is the most appropriate to your type of business...
Read full post on stratuscomm.com
Phishing emails, how to appropriately combat them?
As the technology becomes more sophisticated and more widely used so do the cybercriminals and cyber-attacks. More than ever, cyber-attacks and cyber breaches focus on a monetary gain over just doing damage...
As the technology becomes more sophisticated and more widely used so do the cybercriminals and cyber-attacks. More than ever, cyber-attacks and cyber breaches focus on a monetary gain over just doing damage...
Read full post on stratuscomm.com
Working from home? Check out these technology tips!
Thanks to technology, many types of work can be done remotely. If you’re new to the work-from-home lifestyle, whether due to coronavirus or because you have a position that allows for a remote-based work, here are a few tips to help make working remotely a success.
Thanks to technology, many types of work can be done remotely. If you’re new to the work-from-home lifestyle, whether due to coronavirus or because you have a position that allows for a remote-based work, here are a few tips to help make working remotely a success.
Read full post on stratuscomm.com