tkc.io
Founded in 2011, tkc.io is based in Portland, Maine. We provide onsite IT support in the United States and Europe. Our custom web development group offers worldwide web development and support.
We are a member of the MSPAlliance, an industry trade group for managed service providers (MSP companies provide as-needed computer support as well as long-term, pro-active assistance).
Our support is driven solely by technicians. We don’t have a sales staff. Our personalised approach is scaled to suit your needs. Three computers, three offices or three continents.
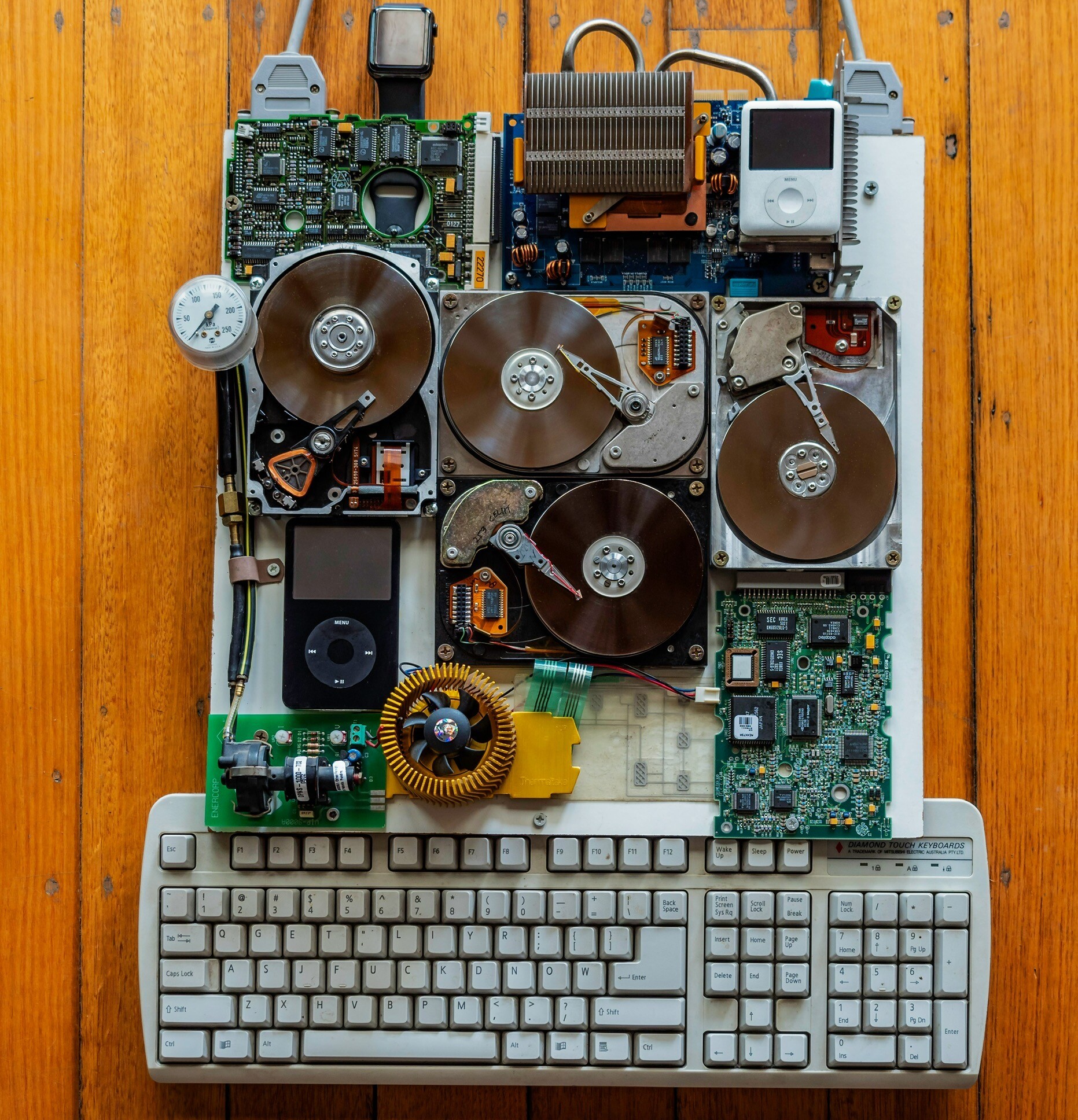
What’s Going on with US Pricing and Availability?
If you’ve bought a new computer in 2025, you likely noticed that the price was higher than expected. Worse, it may not have been available at all. Fluctuating equipment pricing has led to shortages and hoarding. It’s affecting parts and components in ways you might not have expected. This week we placed a large order
If you’ve bought a new computer in 2025, you likely noticed that the price was higher than expected. Worse, it may not have been available at all. Fluctuating equipment pricing has led to shortages and hoarding. It’s affecting parts and components in ways you might not have expected. This week we placed a large order
Read full post on tkc.io
The Microsoft / Crowdstrike Outage
Microsoft systems were CrowdStricken this week.
Microsoft systems were CrowdStricken this week.
Read full post on tkc.io
“Our” AI Generated Holiday Card
We didn’t use it but here is what the image generation AI by Playground came up with.
We didn’t use it but here is what the image generation AI by Playground came up with.
Read full post on tkc.io
What is a BEC Attack and Why Should You Care?
BEC stands for Business Email Compromise. And we promise that it’s the last acronym that we’ll us in this blog post. Everyday, spam filters deal with an onslaught of emails that are either: a) Definitely fake b) Possibly legitimate That’s it. There is no “100% bonafide” option here. Email is always suspect, when it comes
BEC stands for Business Email Compromise. And we promise that it’s the last acronym that we’ll us in this blog post. Everyday, spam filters deal with an onslaught of emails that are either: a) Definitely fake b) Possibly legitimate That’s it. There is no “100% bonafide” option here. Email is always suspect, when it comes
Read full post on tkc.io
Beware of Fake Support
CEO scams, phishing emails, fake texts…the companies that we work with are always on the lookout. But managed service providers can be part of the problem. We’ve been diligent about letting users know but it pays to reinforce a couple of our rules. These are the things that we’ll never do. We’ll never email, message
CEO scams, phishing emails, fake texts…the companies that we work with are always on the lookout. But managed service providers can be part of the problem. We’ve been diligent about letting users know but it pays to reinforce a couple of our rules. These are the things that we’ll never do. We’ll never email, message
Read full post on tkc.io
Cybersecurity: 5 Weaknesses That Hackers Exploit
NOT AS EASY AS “SET IT AND FORGET IT” Keeping your business safe isn’t a one-time thing and it’s not just a matter of adding firewalls and antivirus software. Cybercriminals take advantage of all sorts of vulnerabilities in your company. Some are digital. Some are human. Ransomware meltdowns have grabbed headlines but a lot of businesses suffer less catastrophic invasions. Fraudulent money transfers, stolen business information, and days of lost productivity. Even the smallest business can be targeted by automated attacks and hacker farms. It’s always more affordable to prevent thes
NOT AS EASY AS “SET IT AND FORGET IT” Keeping your business safe isn’t a one-time thing and it’s not just a matter of adding firewalls and antivirus software. Cybercriminals take advantage of all sorts of vulnerabilities in your company. Some are digital. Some are human. Ransomware meltdowns have grabbed headlines but a lot of businesses suffer less catastrophic invasions. Fraudulent money transfers, stolen business information, and days of lost productivity. Even the smallest business can be targeted by automated attacks and hacker farms. It’s always more affordable to prevent these exposures than it is to recover from them. A good percentage of businesses are so affected that they resultantly fold. Checking for weaknesses is an ongoing task. Here are five things you
Read full post on tkc.io
Remote Users and Security Updates
With everyone settling into work from their home digs, it’s important to make sure that the attitudes surrounding good computer security aren't falling by the wayside.
With everyone settling into work from their home digs, it’s important to make sure that the attitudes surrounding good computer security aren't falling by the wayside.
Read full post on tkc.io
Top 5 Five Tips for Coronavirus IT

We’ve Got Some Fancy Masks
Our confinement hasn’t changed our approach to technical support. We try to do it with a little flair.
Our confinement hasn’t changed our approach to technical support. We try to do it with a little flair.
Read full post on tkc.io
Coronavirus IT Update – Remote Workers and Covid-19
Coronavirus: what have learned these first few weeks.
Coronavirus: what have learned these first few weeks.
Read full post on tkc.io