Blue Light IT
Our firm has over 20 years of experience in designing and implementing managed technology solutions for companies ranging from home offices to multi-national corporations. Regardless of your project size we strive to give each customer the personal service they deserve.

Three Years on CRN’s Security 100: What It Actually Means for Your Business
CRN just named Blue Light IT to their Security MSP 100 list for 2026, our third year running. That’s not the news. Here’s the news: we’re protecting businesses from South Florida to South Africa and beyond with the same enterprise-grade security Fortune 500 companies use. Law firms. Car dealerships. Financial services companies. They all get ... Read more
CRN just named Blue Light IT to their Security MSP 100 list for 2026, our third year running. That’s not the news. Here’s the news: we’re protecting businesses from South Florida to South Africa and beyond with the same enterprise-grade security Fortune 500 companies use. Law firms. Car dealerships. Financial services companies. They all get ... Read more
Read full post on bluelightit.com
Why Choose Us as Your Managed Security Service Provider in Boca Raton
Blue Light IT specializes in offering managed security services (MSSP) for businesses of all types and sizes in Boca Raton and across South Florida. Our IT experts can help your organization’s network maintain peak operation, no matter how big or small your business may be. For an affordable flat rate, we’ll take care of all ... Read more
Blue Light IT specializes in offering managed security services (MSSP) for businesses of all types and sizes in Boca Raton and across South Florida. Our IT experts can help your organization’s network maintain peak operation, no matter how big or small your business may be. For an affordable flat rate, we’ll take care of all ... Read more
Read full post on bluelightit.com
Why Smart Businesses Never Risk Their Data: The 2025 Guide to Bulletproof Data Backup
Every 39 seconds, a cyberattack strikes another business. When an attack occurs, we track the source, eliminate malware and restore your data. But here’s what most Boca Raton business owners don’t realize: the attack itself isn’t what destroys companies—it’s the data loss that follows. Think about this for a moment. What would happen to your ... Read more
Every 39 seconds, a cyberattack strikes another business. When an attack occurs, we track the source, eliminate malware and restore your data. But here’s what most Boca Raton business owners don’t realize: the attack itself isn’t what destroys companies—it’s the data loss that follows. Think about this for a moment. What would happen to your ... Read more
Read full post on bluelightit.com
Law Firms Beware: The Silent Ransom Group is Calling
Essential Cybersecurity Guide for Legal Practices Based on Latest FBI Warning The FBI’s Private Industry Notification 20250523-001 warns that law firms are being systematically targeted by the Silent Ransom Group. This cybersecurity threat requires immediate attention from legal professionals to protect sensitive client information and maintain practice integrity. There’s a cybercriminal group called the Silent ... Read more
Essential Cybersecurity Guide for Legal Practices Based on Latest FBI Warning The FBI’s Private Industry Notification 20250523-001 warns that law firms are being systematically targeted by the Silent Ransom Group. This cybersecurity threat requires immediate attention from legal professionals to protect sensitive client information and maintain practice integrity. There’s a cybercriminal group called the Silent ... Read more
Read full post on bluelightit.com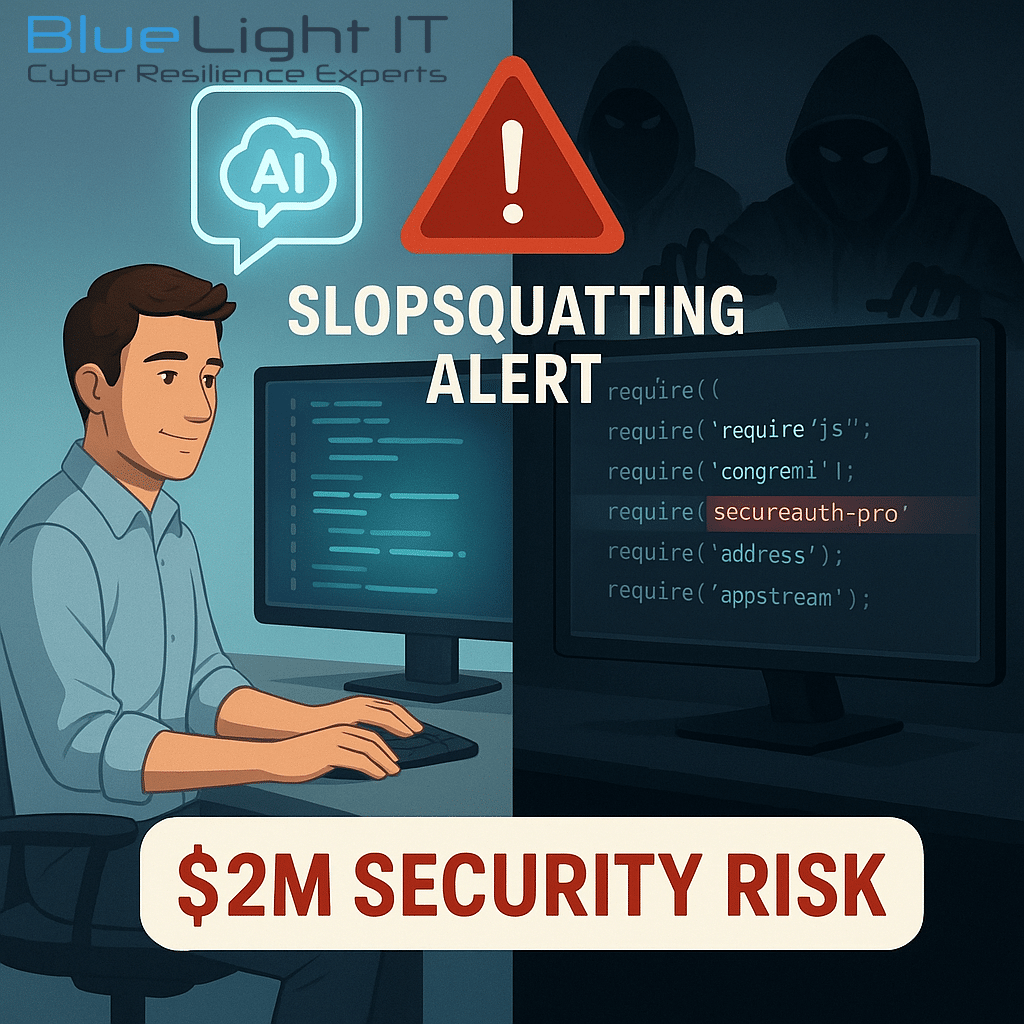
Slopsquatting: The AI Security Threat Every Development Team Must Address
How Slopsquatting Exploits AI Hallucinations to Compromise Your Code In my 20+ years leading cybersecurity initiatives, I’ve witnessed numerous attack vectors emerge, but slopsquatting represents a uniquely dangerous evolution targeting AI-assisted development workflows. Even if you’re not writing code yourself, your internal or outsourced developers might be exposing your business to serious risk, without even ... Read more
How Slopsquatting Exploits AI Hallucinations to Compromise Your Code In my 20+ years leading cybersecurity initiatives, I’ve witnessed numerous attack vectors emerge, but slopsquatting represents a uniquely dangerous evolution targeting AI-assisted development workflows. Even if you’re not writing code yourself, your internal or outsourced developers might be exposing your business to serious risk, without even ... Read more
Read full post on bluelightit.com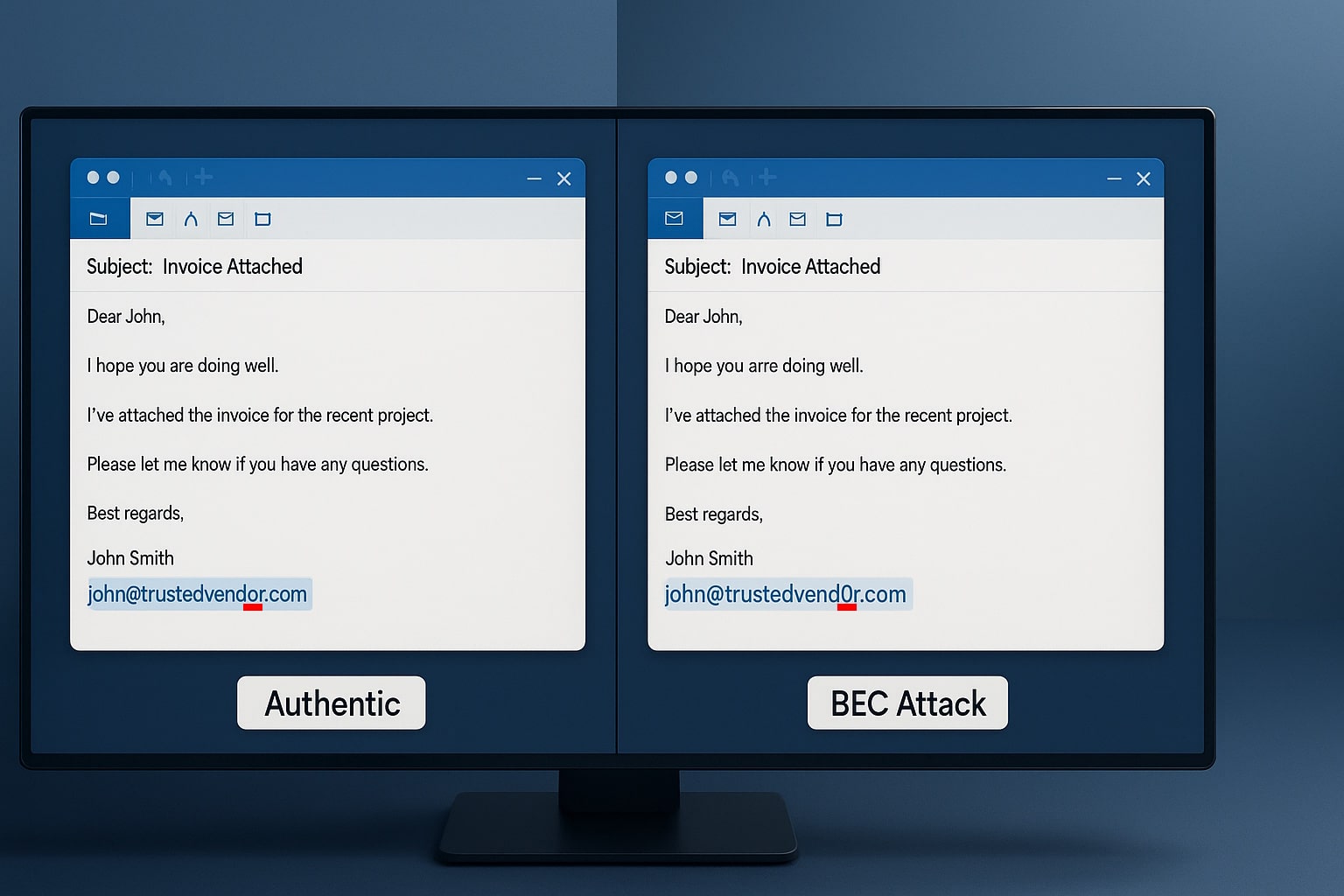
The $287,000 Email Mistake
Why Business Email Compromise Is Your Company’s Biggest Blind Spot I’m about to tell you something that might save your company from financial ruin. And no, this isn’t some hyped-up sales pitch about the latest software gizmo. This is about a sophisticated threat that’s draining business bank accounts while everyone’s distracted by ransomware headlines. It’s ... Read more
Why Business Email Compromise Is Your Company’s Biggest Blind Spot I’m about to tell you something that might save your company from financial ruin. And no, this isn’t some hyped-up sales pitch about the latest software gizmo. This is about a sophisticated threat that’s draining business bank accounts while everyone’s distracted by ransomware headlines. It’s ... Read more
Read full post on bluelightit.com
Did You Know There Are Multiple Types of Phishing? (2025 Edition)
Cybercriminals are getting smarter, and phishing attacks are evolving. What used to be simple email scams have now expanded into highly targeted, multi-channel attacks designed to steal credentials, install malware, and even take over entire business operations. Phishing isn’t just one thing, it comes in different forms, each with its own tactics. Here’s what you ... Read more
Cybercriminals are getting smarter, and phishing attacks are evolving. What used to be simple email scams have now expanded into highly targeted, multi-channel attacks designed to steal credentials, install malware, and even take over entire business operations. Phishing isn’t just one thing, it comes in different forms, each with its own tactics. Here’s what you ... Read more
Read full post on bluelightit.com
Why Business Owners Need Managed IT Services
Managed IT Services play a key role in maintaining security, improving efficiency, and boosting productivity for businesses. The importance of a robust IT infrastructure should not be underestimated, especially in the face of increasing security threats, outdated systems, limited IT staff, and potential downtime costs that businesses may face. As technology continues to shape the ... Read more
Managed IT Services play a key role in maintaining security, improving efficiency, and boosting productivity for businesses. The importance of a robust IT infrastructure should not be underestimated, especially in the face of increasing security threats, outdated systems, limited IT staff, and potential downtime costs that businesses may face. As technology continues to shape the ... Read more
Read full post on bluelightit.com
Disaster Recovery and Business Continuity Planning
Your organization must be prepared to navigate unforeseen disruptions that have the potential to severely impact their operations. While disasters of various scales are inevitable, it’s imperative for your business to proactively strategize and establish robust disaster recovery and business continuity plans. Such meticulously designed frameworks ensure resilience in times of crisis, enabling your company ... Read more
Your organization must be prepared to navigate unforeseen disruptions that have the potential to severely impact their operations. While disasters of various scales are inevitable, it’s imperative for your business to proactively strategize and establish robust disaster recovery and business continuity plans. Such meticulously designed frameworks ensure resilience in times of crisis, enabling your company ... Read more
Read full post on bluelightit.com
What are Managed IT Services?
Technology has brought many benefits and advancements throughout history, but one downside is that it continues to become more complicated. “IT services” refers to any service or product provided by a company, including technical support, cybersecurity issues, website development, and more. In this article, we’ll discuss what managed IT services are and how they can ... Read more
Technology has brought many benefits and advancements throughout history, but one downside is that it continues to become more complicated. “IT services” refers to any service or product provided by a company, including technical support, cybersecurity issues, website development, and more. In this article, we’ll discuss what managed IT services are and how they can ... Read more
Read full post on bluelightit.com