Technical Support International (TSI)
Our main purpose is to serve our clients’ technology needs and add value to our customer's information infrastructure.
We have designed our company around the needs of our clients and you will find that in service, expertise and cost, we have no equal.
TSI provides computer solutions to customers ranging from small businesses to large corporations. Our services and the products we sell range from basic computer maintenance to sophisticated computer networking.
We also provide IT Managed Services, VPNs, and Internet Security. TSI strives to provide our customers with the best services and the right information. We deliver our services by using a combination of local onsite experts, network management tools, and services performed remotely. Our goals are to assist you in staying focused on your business while we handle the support, maintenance, and security of your network and computers.
TSI consists of a team of professionals offering their individual and collective capabilities to assist our clients with a complex technology. We conduct business in a manner, which our customers entrust to us. We share our company's commitment to growth and aim to be viewed as a leader in information technology.
The courteous, professional manner in which we deliver our Services is the benchmark of our commitment to our clients. We are fully aware of our responsibilities to our clients, our employees, and our company.
Our years of experience in system integration and support gives you full confidence that we can plan, install, support Systems and Applications that will meet your business needs for today and tomorrow.

Still on Windows 10? Why Not Upgrading is a Serious Security Risk for Businesses
Christopher Souza | CEO As of October 2025, Microsoft stopped supporting Windows 10, ending any new security updates, patches, or protection against newly discovered vulnerabilities. Despite this, millions of systems are still running on outdated software, presenting a considerable direct and indirect risk to organizations like yours. With extended support available ending on October 13,…
Christopher Souza | CEO As of October 2025, Microsoft stopped supporting Windows 10, ending any new security updates, patches, or protection against newly discovered vulnerabilities. Despite this, millions of systems are still running on outdated software, presenting a considerable direct and indirect risk to organizations like yours. With extended support available ending on October 13,…
Read full post on tsisupport.com
TSI Employee Spotlight: Joseph Gutto
Joe Gutto is TSI’s Network and Cloud Services Manager/Azure Architect and is our newest addition to the team! With over 26 years of experience in the IT sector and a career of system administration to leading quality assurance and cloud infrastructure projects, Joe is already making waves through the cybersecurity field, and we’re thrilled to…
Joe Gutto is TSI’s Network and Cloud Services Manager/Azure Architect and is our newest addition to the team! With over 26 years of experience in the IT sector and a career of system administration to leading quality assurance and cloud infrastructure projects, Joe is already making waves through the cybersecurity field, and we’re thrilled to…
Read full post on tsisupport.com
CMMC’s 2026 “Deadline” Explained: Why It’s Not a True Deadline and What Actually Drives Compliance
Christopher Souza | CEO There’s a growing misconception across the Defense Industrial Base (DIB): that November 2026 is a universal deadline for CMMC certification. It’s not. CMMC does not operate on a single, universal deadline. Instead, requirements are enforced through contract awards as the program rolls out in phases. For many organizations, this means the…
Christopher Souza | CEO There’s a growing misconception across the Defense Industrial Base (DIB): that November 2026 is a universal deadline for CMMC certification. It’s not. CMMC does not operate on a single, universal deadline. Instead, requirements are enforced through contract awards as the program rolls out in phases. For many organizations, this means the…
Read full post on tsisupport.com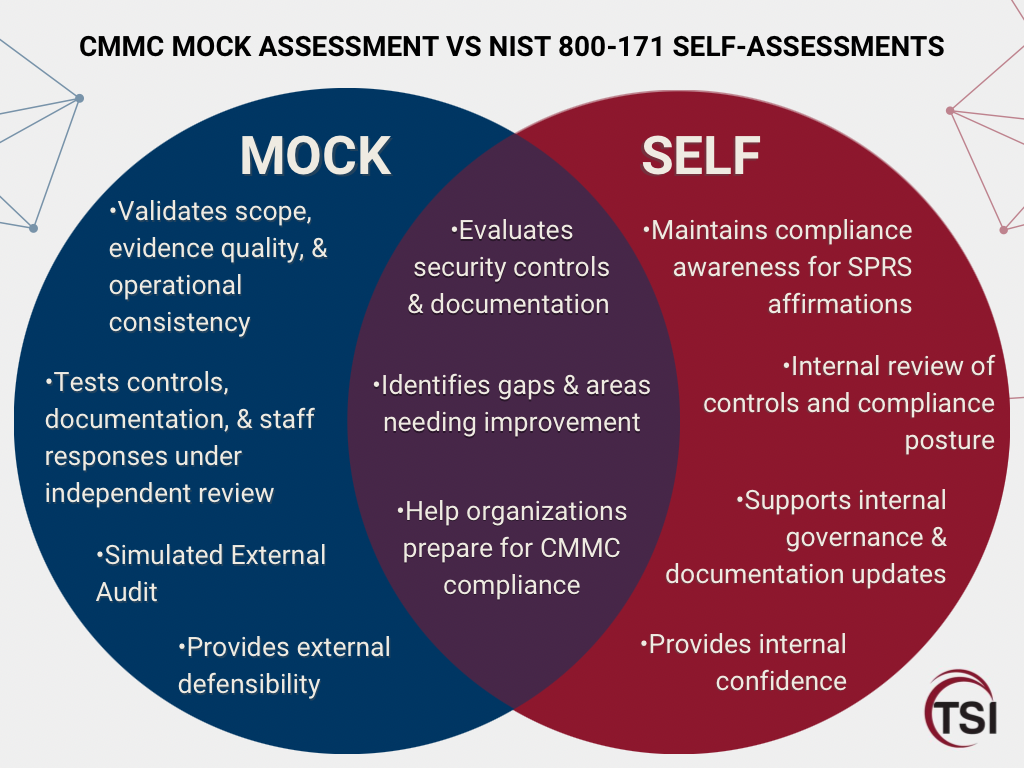
CMMC Mock Assessments vs. NIST SP 800-171 Self-Assessments
Christopher Souza | CEO For many defense contractors, one of the biggest CMMC mistakes is assuming that an internal NIST SP 800-171 self-assessment is enough to prove readiness for a C3PAO certification audit. It is not. A self-assessment is an important internal management exercise, but it is not the same as demonstrating readiness under the…
Christopher Souza | CEO For many defense contractors, one of the biggest CMMC mistakes is assuming that an internal NIST SP 800-171 self-assessment is enough to prove readiness for a C3PAO certification audit. It is not. A self-assessment is an important internal management exercise, but it is not the same as demonstrating readiness under the…
Read full post on tsisupport.com
Elevated Cybersecurity Risk Amid U.S. and Iran Conflict
Christopher Souza | CEO A cyber advisory issued by our partners at Sophos highlights an increased global cyber risk environment due to escalating geopolitical tensions involving the United States, Israel, and Iran. Sophos assesses the current threat level as elevated, with the greatest risk occurring in the immediate to short term, ranging from days to…
Christopher Souza | CEO A cyber advisory issued by our partners at Sophos highlights an increased global cyber risk environment due to escalating geopolitical tensions involving the United States, Israel, and Iran. Sophos assesses the current threat level as elevated, with the greatest risk occurring in the immediate to short term, ranging from days to…
Read full post on tsisupport.com
The Self-Assessment Era Is Over! CMMC Is Now Mandatory
Christopher Souza | CEO As of February 1, 2026, the DoD implemented significant updates to DFARS and FAR cybersecurity clauses as part of its FAR Overhaul initiative. While certain DFARS “Basic” self-assessment requirements have been removed at the federal clause level, this does not reduce your cybersecurity obligations. It marks a clear transition away from…
Christopher Souza | CEO As of February 1, 2026, the DoD implemented significant updates to DFARS and FAR cybersecurity clauses as part of its FAR Overhaul initiative. While certain DFARS “Basic” self-assessment requirements have been removed at the federal clause level, this does not reduce your cybersecurity obligations. It marks a clear transition away from…
Read full post on tsisupport.com