Managed Services Group
With 24/7/365 monitoring & remediation, our Proactive Preventative Maintenace programs, coupled with Vendor Management (manage clients copier, phone, ISP, etc... vendors) allow us to predict and manage IT issues before they affect client downtime and productivity.

Mark Fugett on Liquidity as a Strategic Weapon for CEOs
Cash is no longer just a financial metric, it is a strategic advantage. In Chief Executive, Founder & CEO Mark Fugett explains why companies should maintain 9 to 12 months of liquidity and embed cash discipline across leadership to strengthen resilience, improve decision making and create flexibility to invest in growth without sacrificing margin. As
Cash is no longer just a financial metric, it is a strategic advantage. In Chief Executive, Founder & CEO Mark Fugett explains why companies should maintain 9 to 12 months of liquidity and embed cash discipline across leadership to strengthen resilience, improve decision making and create flexibility to invest in growth without sacrificing margin. As
Read full post on msgrouponline.com
The Dangerous Gap Between Cyber Insurance and Cyber Reality
Cyber insurance was never designed for the reality of modern cyberattacks. Not when a single compromised account can halt operations, expose sensitive data, trigger regulatory scrutiny, damage customer trust, and create millions in downstream financial impact within hours. And that is exactly why today’s cyber losses have become so difficult to underwrite, litigate, and recover from. The
Cyber insurance was never designed for the reality of modern cyberattacks. Not when a single compromised account can halt operations, expose sensitive data, trigger regulatory scrutiny, damage customer trust, and create millions in downstream financial impact within hours. And that is exactly why today’s cyber losses have become so difficult to underwrite, litigate, and recover from. The
Read full post on msgrouponline.com
Aaron Puckett on Cybersecurity and IT as the Hidden Variable in Deal Valuation
Cybersecurity and IT are no longer back-office considerations in a transaction. In a recent Orlando Business Journal, Executive Vice President Aaron Puckett shares insight into how these areas now play a direct role in valuation, deal structure and timelines. Buyers are evaluating them earlier as gaps in access, systems and control increasingly surface during due
Cybersecurity and IT are no longer back-office considerations in a transaction. In a recent Orlando Business Journal, Executive Vice President Aaron Puckett shares insight into how these areas now play a direct role in valuation, deal structure and timelines. Buyers are evaluating them earlier as gaps in access, systems and control increasingly surface during due
Read full post on msgrouponline.com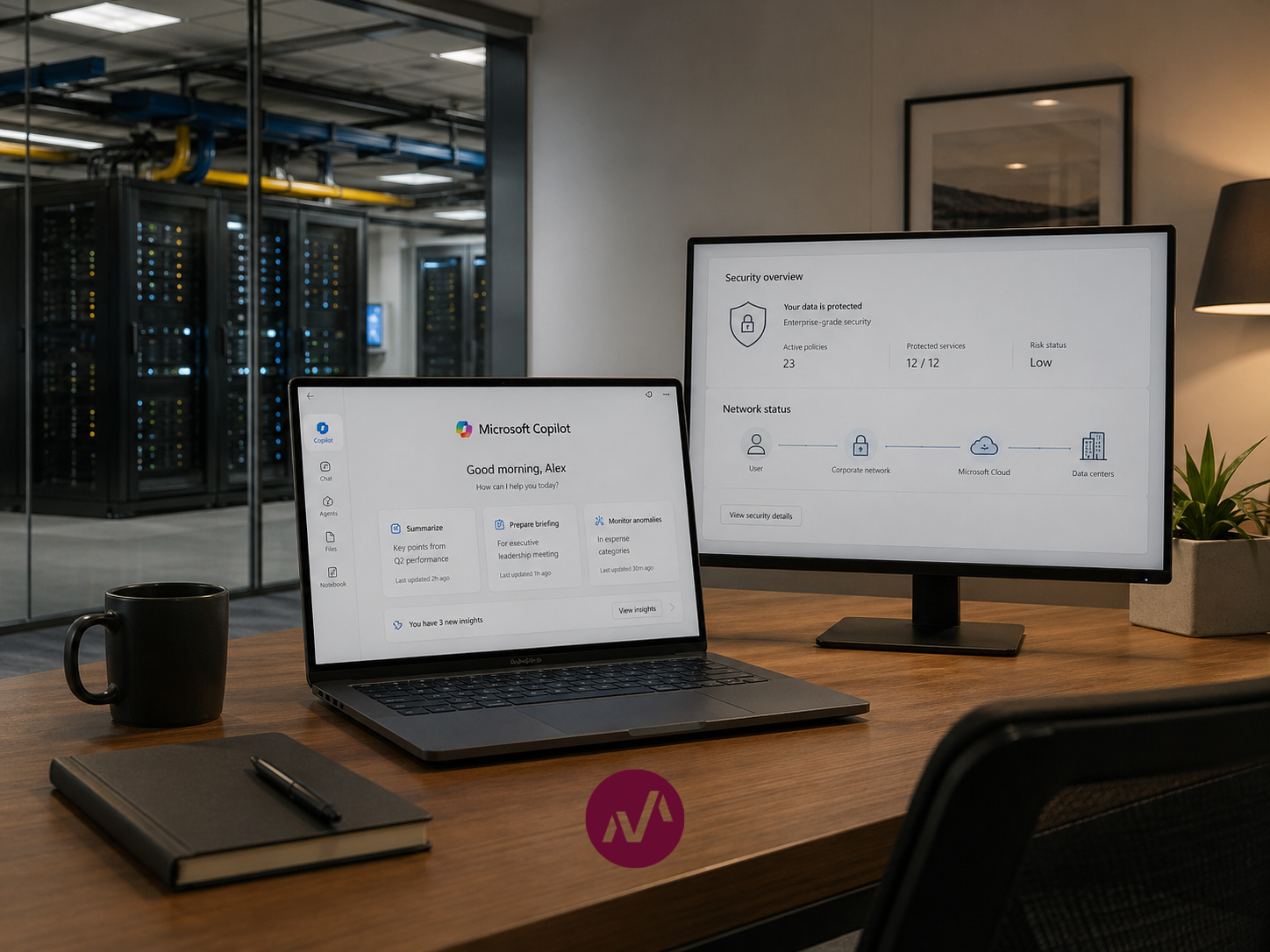
Agentic AI Security and Microsoft Copilot: What Business Leaders Need to Understand Before Expanding AI Access
Published: April, 2026 Author: Jeramy Martin, Solutions Engineer Category: Cybersecurity, AI Governance, IT Leadership Managed Services Group (MSG) is a managed IT service provider and MSSP based in Orlando, Florida, serving businesses across healthcare, legal, financial services, and professional services. Our team works daily inside Microsoft 365 environments, security toolchains, and compliance frameworks on behalf of our
Published: April, 2026 Author: Jeramy Martin, Solutions Engineer Category: Cybersecurity, AI Governance, IT Leadership Managed Services Group (MSG) is a managed IT service provider and MSSP based in Orlando, Florida, serving businesses across healthcare, legal, financial services, and professional services. Our team works daily inside Microsoft 365 environments, security toolchains, and compliance frameworks on behalf of our
Read full post on msgrouponline.com
Recovery Is the Real Test of Cyber Maturity; Why Resilience Determines Business Impact
Most organizations spend a lot of time thinking about how to prevent cyber incidents. The more honest question is what happens when one happens. Because at some point, it will. CISA’s Zero Trust model focuses heavily on controlling identity, devices, data, applications, and networks. Those are the fundamentals. But what CISA consistently reinforces across its
Most organizations spend a lot of time thinking about how to prevent cyber incidents. The more honest question is what happens when one happens. Because at some point, it will. CISA’s Zero Trust model focuses heavily on controlling identity, devices, data, applications, and networks. Those are the fundamentals. But what CISA consistently reinforces across its
Read full post on msgrouponline.com
Why Detection Speed in Cybersecurity Is Now a Business Issue
Most organizations still think business cybersecurity is about stopping attacks. The reality is most incidents aren’t prevented. They’re detected. And how fast detection speed happens is what determines impact. That’s why CISA emphasizes Threat Detection as a core pillar of Zero Trust. Not just keeping threats out, but identifying and responding to them quickly once
Most organizations still think business cybersecurity is about stopping attacks. The reality is most incidents aren’t prevented. They’re detected. And how fast detection speed happens is what determines impact. That’s why CISA emphasizes Threat Detection as a core pillar of Zero Trust. Not just keeping threats out, but identifying and responding to them quickly once
Read full post on msgrouponline.com
Why Healthcare Cybersecurity Is Really About Data Discipline
If Identity is where most breaches start and Devices are where they spread, Data is usually the reason healthcare organizations become targets in the first place. That’s why CISA emphasizes Data Protection as a core pillar of Zero Trust. Once identity and devices are reasonably controlled, the next focus becomes simple: protecting what actually matters.
If Identity is where most breaches start and Devices are where they spread, Data is usually the reason healthcare organizations become targets in the first place. That’s why CISA emphasizes Data Protection as a core pillar of Zero Trust. Once identity and devices are reasonably controlled, the next focus becomes simple: protecting what actually matters.
Read full post on msgrouponline.com
MSG CEO Mark Fugett Details How His Career Journey Has Shaped How He Leads Today in Authority Magazine
CEO Mark Fugett was recently featured in an in-depth interview with Authority Magazine, exploring how his career journey has shaped his leadership philosophy. In the conversation, Mark reflects on the early experiences that led him to found Managed Services Group, including his frustration with unreliable IT execution and his commitment to building a company grounded
CEO Mark Fugett was recently featured in an in-depth interview with Authority Magazine, exploring how his career journey has shaped his leadership philosophy. In the conversation, Mark reflects on the early experiences that led him to found Managed Services Group, including his frustration with unreliable IT execution and his commitment to building a company grounded
Read full post on msgrouponline.com