KeyNet Technologies
KeyNet’s Intentional by Design, mindful, and caring approach to every client engagement sets them apart from traditional managed IT services.
KeyNet enhances end-user and client experiences while forecasting trends and making informed recommendations for their continued protection.
KeyNet’s success is measured by improving day-to-day functions and achieving their client’s operational outcomes through technology.
KeyNet is headquartered in Lancaster, PA.

KeyNet Technologies Ramps Fight Against Cyber Threats
KeyNet Technologies in Lancaster PA announces the CISSP certification of Security Analyst, Ryan Brommer. KeyNet. KeyNet continues to invest in securing our clients from cyber threats. The addition of an in-demand CISSP accreditation differentiates KeyNet's security practice from competing regional MSPs and MSSP.
KeyNet Technologies in Lancaster PA announces the CISSP certification of Security Analyst, Ryan Brommer. KeyNet. KeyNet continues to invest in securing our clients from cyber threats. The addition of an in-demand CISSP accreditation differentiates KeyNet's security practice from competing regional MSPs and MSSP.
Read full post on keynettech.com
Third Party Should Be a First Priority
Getting Started with Third-Party Vendor Cybersecurity Risk Management Doing business today takes a village. No matter the size of your organization, you can’t do it alone—nor should you. Working with other companies, from parts suppliers or outsourced legal teams to software providers, often adds great value for your organization. These important third-party relationships also come
Getting Started with Third-Party Vendor Cybersecurity Risk Management Doing business today takes a village. No matter the size of your organization, you can’t do it alone—nor should you. Working with other companies, from parts suppliers or outsourced legal teams to software providers, often adds great value for your organization. These important third-party relationships also come
Read full post on keynettech.com
Third Party Should Be a First Priority
Third Party Vendor Cybersecurity Risk Management Working with third party vendors should be a first priority. We understand that doing business today takes a village. No matter the size of your organization, you can’t do it alone—nor should you. Working with third party vendors, from parts suppliers or outsourced legal teams to software providers, often
Third Party Vendor Cybersecurity Risk Management Working with third party vendors should be a first priority. We understand that doing business today takes a village. No matter the size of your organization, you can’t do it alone—nor should you. Working with third party vendors, from parts suppliers or outsourced legal teams to software providers, often
Read full post on keynettech.com
How Does Co-Managed SIEM Elevate Your Cybersecurity Strategy?
Five Reasons Why Tapping Outside Cybersecurity Expertise is the Practical Way Forward for Small and Midsize Companies Every second matters in cyberspace. It only takes one second for a potential threat to become an active one. That’s why real-time detection is essential in mitigating your risk against cyberattacks. Implementing advanced threat detection requires cybersecurity experts
Five Reasons Why Tapping Outside Cybersecurity Expertise is the Practical Way Forward for Small and Midsize Companies Every second matters in cyberspace. It only takes one second for a potential threat to become an active one. That’s why real-time detection is essential in mitigating your risk against cyberattacks. Implementing advanced threat detection requires cybersecurity experts
Read full post on keynettech.com
How Does Co-Managed SIEM Elevate Your Cybersecurity Strategy?
Five Reasons Why Tapping Outside Cybersecurity Expertise is the Practical Way Forward for Small and Midsize Companies Every second matters in cyberspace. It only takes one second for a potential threat to become an active one. That’s why real-time detection is essential in mitigating your risk against cyberattacks. Implementing advanced threat detection requires cybersecurity experts
Five Reasons Why Tapping Outside Cybersecurity Expertise is the Practical Way Forward for Small and Midsize Companies Every second matters in cyberspace. It only takes one second for a potential threat to become an active one. That’s why real-time detection is essential in mitigating your risk against cyberattacks. Implementing advanced threat detection requires cybersecurity experts
Read full post on keynettech.com
COVID-19 Altered the Threat Landscape. Are You Properly Prepared for Today’s Cyberattacks?
Four Critical Steps to Reset Your Long-Term Cybersecurity and Compliance Strategy “When COVID-19 hit, I hate to admit it as an IT leader…I was caught off-guard. With years of experience, I followed my instincts, and we did what was needed to respond to the new normal. I was amazed, but not surprised, how resilient everyone
Four Critical Steps to Reset Your Long-Term Cybersecurity and Compliance Strategy “When COVID-19 hit, I hate to admit it as an IT leader…I was caught off-guard. With years of experience, I followed my instincts, and we did what was needed to respond to the new normal. I was amazed, but not surprised, how resilient everyone
Read full post on keynettech.com
COVID-19 Altered the Threat Landscape. Are You Properly Prepared for Today’s Cyberattacks?
Cybersecurity and Compliance Strategy needs to be reset. “When COVID-19 hit, I hate to admit it as an IT leader…I was caught off-guard. With years of experience, I followed my instincts, and we did what was needed to respond to the new normal. I was amazed, but not surprised, how resilient everyone around me became,
Cybersecurity and Compliance Strategy needs to be reset. “When COVID-19 hit, I hate to admit it as an IT leader…I was caught off-guard. With years of experience, I followed my instincts, and we did what was needed to respond to the new normal. I was amazed, but not surprised, how resilient everyone around me became,
Read full post on keynettech.com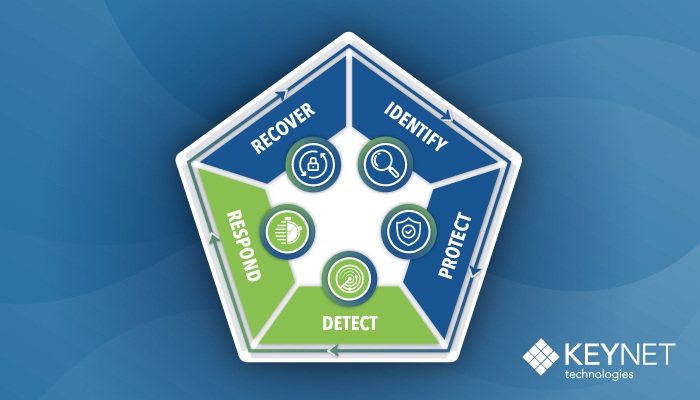
Strategic IT Services Provider KeyNet Technologies Launches Advanced Cybersecurity Solution Backed by 24×7 Security Operations Center
Real-Time Threat Detection and Response Now Attainable for Small and Medium-Size Business (SMB) (Lancaster, PA) January 26, 2021 – KeyNet Technologies, the trusted advisor and strategic IT and Cybersecurity solutions provider for SMBs, today launches KeyNet Advanced Cybersecurity, a comprehensive, defense-in-depth approach to securing systems and data by extending beyond traditional protections to swiftly detect
Real-Time Threat Detection and Response Now Attainable for Small and Medium-Size Business (SMB) (Lancaster, PA) January 26, 2021 – KeyNet Technologies, the trusted advisor and strategic IT and Cybersecurity solutions provider for SMBs, today launches KeyNet Advanced Cybersecurity, a comprehensive, defense-in-depth approach to securing systems and data by extending beyond traditional protections to swiftly detect
Read full post on keynettech.com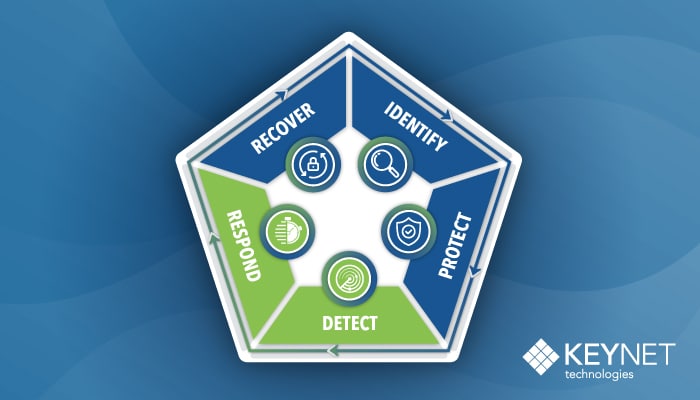
Strategic IT Services Provider KeyNet Technologies Launches Advanced Cybersecurity Solutions Backed by 24×7 Security Operations Center
Real-Time Threat Detection and Response Now Attainable for Small and Medium-Size Business (SMB) (Lancaster, PA) January 26, 2021 – KeyNet Technologies, the trusted advisor and strategic IT and Cybersecurity solutions provider for SMBs, today launches KeyNet Advanced Cybersecurity, a comprehensive, defense-in-depth approach to securing systems and data by extending beyond traditional protections to swiftly detect
Real-Time Threat Detection and Response Now Attainable for Small and Medium-Size Business (SMB) (Lancaster, PA) January 26, 2021 – KeyNet Technologies, the trusted advisor and strategic IT and Cybersecurity solutions provider for SMBs, today launches KeyNet Advanced Cybersecurity, a comprehensive, defense-in-depth approach to securing systems and data by extending beyond traditional protections to swiftly detect
Read full post on keynettech.com