Fortis
The company's flagship VoIP telephony solution, ProLinePBX™, offers flexible, turnkey business telephone services, hosted entirely in the cloud.
Founded by telecom industry veterans, Fortis' engineering team has contributed to the development large carrier networks for AT&T, Sprint, Comcast, Microsoft, Time Warner and the United States Department of Defense.
Fortis differentiates itself from traditional VoIP and IT service providers with its "concierge service". The company provides all customers with a named account manager to deliver on its promise of personalized service.
Do You and Your Employees Have an Encryption Mindset?
Data is one of your organization’s most valuable assets and is in perpetual peril. Proprietary business information, sensitive customer data, financial reports, and intellectual property all need protection from unauthorized access. This is true whether the data is in transit or at rest. While deploying firewalls, antivirus software, and other security measures is essential, encryption
Data is one of your organization’s most valuable assets and is in perpetual peril. Proprietary business information, sensitive customer data, financial reports, and intellectual property all need protection from unauthorized access. This is true whether the data is in transit or at rest. While deploying firewalls, antivirus software, and other security measures is essential, encryption
Read full post on fortistelecom.net
Fundamental Cybersecurity Controls All SMBs Should Have
The Center for Internet Security (CIS) is a nonprofit organization that publishes a set of cybersecurity Controls and Safeguards for businesses. If you run a small or mid-sized business, a subset of these Controls—those in Implementation Group 1 (IG1)—is foundational and should be strongly considered for your organization’s solid cybersecurity posture. A strong security posture
The Center for Internet Security (CIS) is a nonprofit organization that publishes a set of cybersecurity Controls and Safeguards for businesses. If you run a small or mid-sized business, a subset of these Controls—those in Implementation Group 1 (IG1)—is foundational and should be strongly considered for your organization’s solid cybersecurity posture. A strong security posture
Read full post on fortistelecom.net
A Guide to SOC 2 Compliance for SMBs
As a small or mid-sized business owner or manager, you have a lot on your plate—keeping your customers happy, staffing your organization, managing finances, and ensuring the growth of your business. If your company handles sensitive customer data or plans to provide services to larger enterprises, consider SOC (System and Organization Controls) compliance to acquire
As a small or mid-sized business owner or manager, you have a lot on your plate—keeping your customers happy, staffing your organization, managing finances, and ensuring the growth of your business. If your company handles sensitive customer data or plans to provide services to larger enterprises, consider SOC (System and Organization Controls) compliance to acquire
Read full post on fortistelecom.net
California Accounting Firms: Compliance and Best Practices for Safeguarding Client Data
The accounting industry continues to be transformed by changing technology, where staff members work from, and an increasing number of outsider threats. With an eye-watering number of challenges and changes and with increasingly sophisticated threat actors, the industry needs to be more vigilant than ever about ensuring the security of sensitive client data. California CPA
The accounting industry continues to be transformed by changing technology, where staff members work from, and an increasing number of outsider threats. With an eye-watering number of challenges and changes and with increasingly sophisticated threat actors, the industry needs to be more vigilant than ever about ensuring the security of sensitive client data. California CPA
Read full post on fortistelecom.net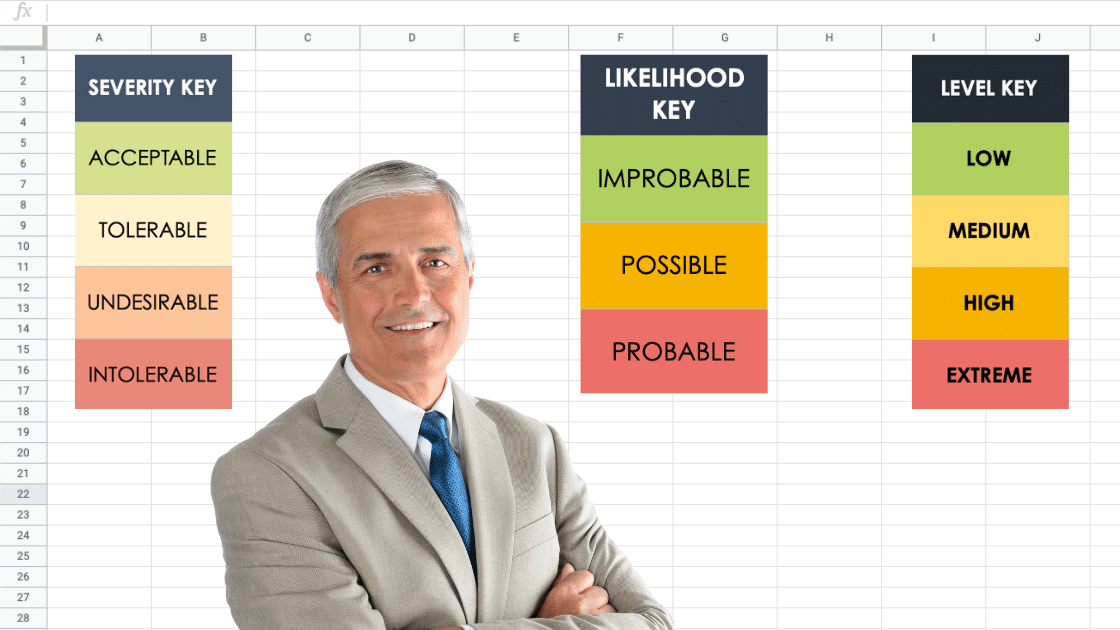
Business Continuity Risk Assessment: A Critical Exercise
How can you assess the risks of a disaster interrupting business operations? How can you manage and reduce risk? Here in California, the word ‘disaster’ is mainly associated with large-scale, destructive events such as fires, earthquakes, and floods. However, according to the Oxford Dictionary, one of the definitions of ‘disaster’ is “an event or fact
How can you assess the risks of a disaster interrupting business operations? How can you manage and reduce risk? Here in California, the word ‘disaster’ is mainly associated with large-scale, destructive events such as fires, earthquakes, and floods. However, according to the Oxford Dictionary, one of the definitions of ‘disaster’ is “an event or fact
Read full post on fortistelecom.net
Why Businesses Migrate Legacy Applications to a Private Cloud
Your business may still depend on one or more robust legacy applications. From a cost and user access perspective, would it be beneficial to migrate some or all of them to the cloud? Software Environments Let’s start by looking at four general environments in which business software runs. For a given organization, these are not
Your business may still depend on one or more robust legacy applications. From a cost and user access perspective, would it be beneficial to migrate some or all of them to the cloud? Software Environments Let’s start by looking at four general environments in which business software runs. For a given organization, these are not
Read full post on fortistelecom.net
How to Prevent Orphaned Online Marketing Accounts
An orphan or orphaned online account is one that nobody in your business has access to. Orphan accounts can cause frustration, waste time, and reduce lead flow & brand exposure. How does this occur? Sometimes, an employee leaves a company without sharing usernames and passwords for the cloud marketing accounts they set up using their
An orphan or orphaned online account is one that nobody in your business has access to. Orphan accounts can cause frustration, waste time, and reduce lead flow & brand exposure. How does this occur? Sometimes, an employee leaves a company without sharing usernames and passwords for the cloud marketing accounts they set up using their
Read full post on fortistelecom.net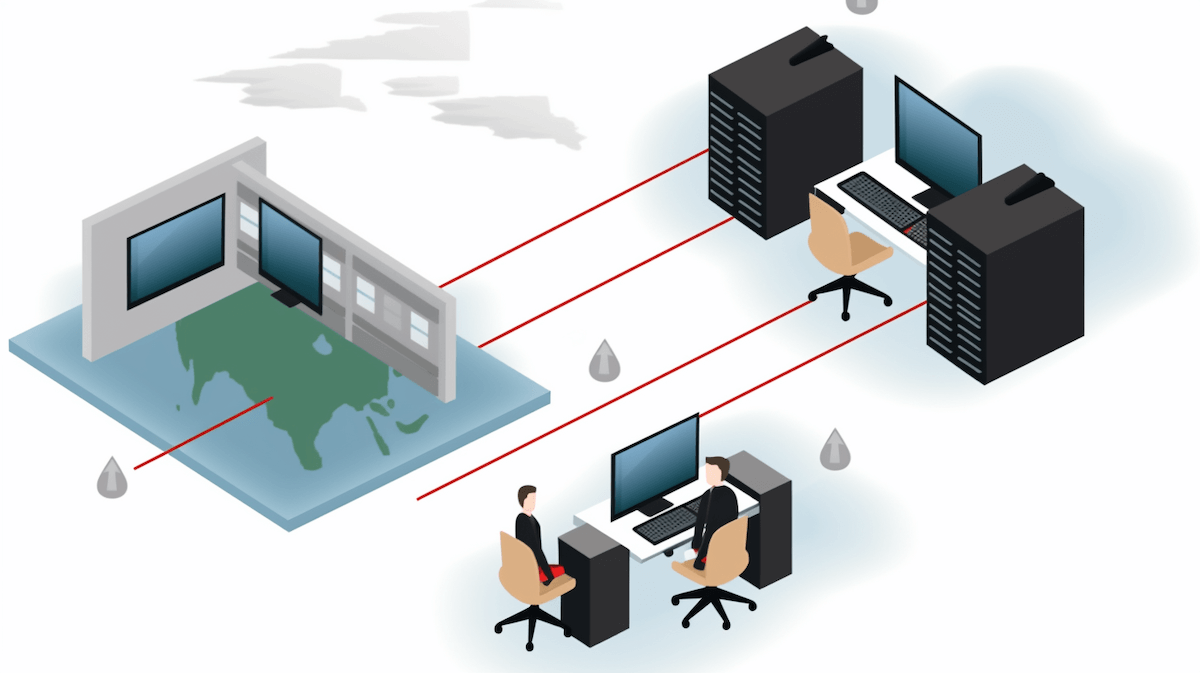
Microsoft 365 MFA-Bypass Schemes: Protecting Your Business
Multi-factor authentication (MFA) is a critical layer of protection for online business accounts. MFA is a system that uses various methods to confirm a user’s identity — typically involving something the user knows, like a password, and something the user has, like a physical device. However, none of the levels of MFA, even FIDO security
Multi-factor authentication (MFA) is a critical layer of protection for online business accounts. MFA is a system that uses various methods to confirm a user’s identity — typically involving something the user knows, like a password, and something the user has, like a physical device. However, none of the levels of MFA, even FIDO security
Read full post on fortistelecom.net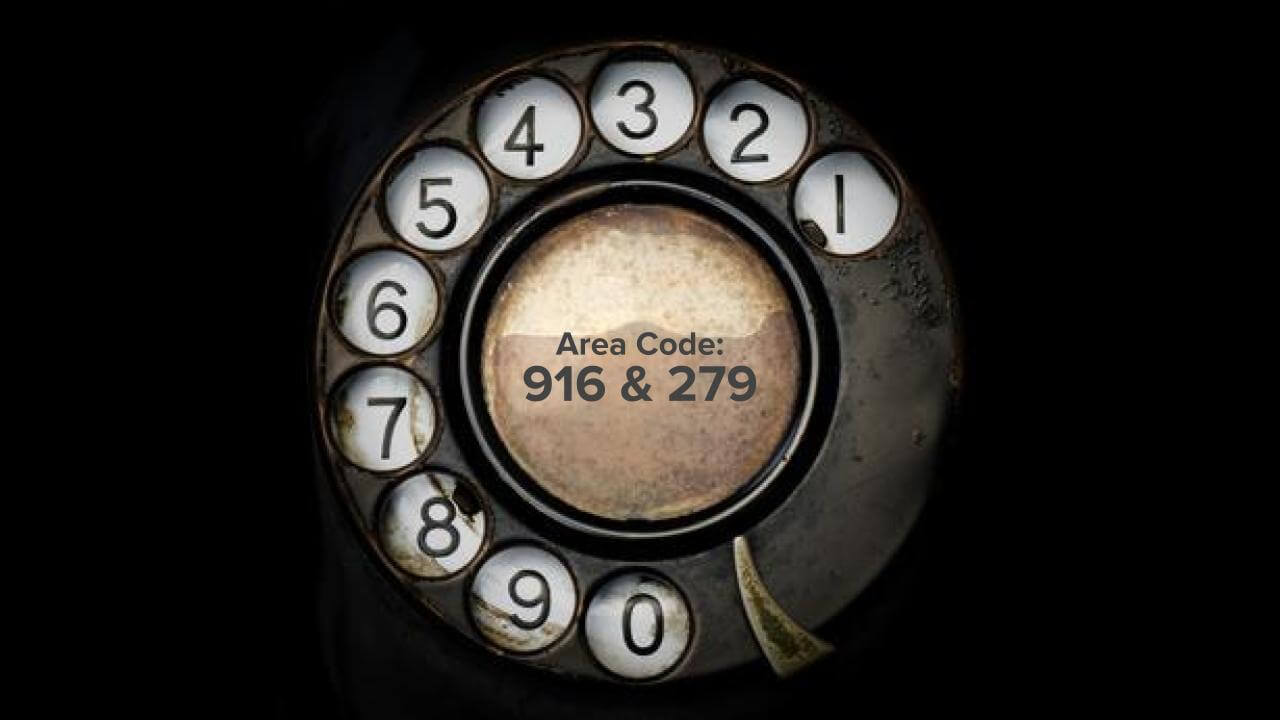
916 Area Code Insights: Key Facts About This Number
The 916 area code was one of California’s original three area codes when area codes were introduced to the United States and Canada in 1947 as part of the North American Numbering Plan (NANP). The other two California area codes introduced that year were 415 and 213. The 916 area code in northern California initially
The 916 area code was one of California’s original three area codes when area codes were introduced to the United States and Canada in 1947 as part of the North American Numbering Plan (NANP). The other two California area codes introduced that year were 415 and 213. The 916 area code in northern California initially
Read full post on fortistelecom.net
Six Levels Of Two-Factor Authentication For Protecting Your Online Accounts
Strong passwords are essential to protecting your business and personal online account. However, in some cases, a strong password may not be enough to deter cybercriminals from assuming your online identity and accessing your business or personal data. Dive into this guide on two-factor authentication because it offers practical advice on securing your online accounts
Strong passwords are essential to protecting your business and personal online account. However, in some cases, a strong password may not be enough to deter cybercriminals from assuming your online identity and accessing your business or personal data. Dive into this guide on two-factor authentication because it offers practical advice on securing your online accounts
Read full post on fortistelecom.net