Phantom Technology Solutions
Choose the best IT support option below.
Everything from consulting and support to complex business software systems, we find the right solutions for businesses both big and small.

How You Can Protect Your Business If a Mobile Device Disappears
The mobile device is deeply ingrained in modern life, society, and culture, so it will be present in the workplace. This can be a very useful thing… with the right preparations, your employees can become a lot more mobile in terms of their potential productivity.However, mobile work isn’t without its dangers. Perhaps the most obvious risk is that a device will be lost, whether it's left behind in a rideshare or pilfered as a latte is retrieved from the barista. Either way, your business will have suffered a data breach.Let’s talk about how this outcome can be avoided with some proactive planni
The mobile device is deeply ingrained in modern life, society, and culture, so it will be present in the workplace. This can be a very useful thing… with the right preparations, your employees can become a lot more mobile in terms of their potential productivity.However, mobile work isn’t without its dangers. Perhaps the most obvious risk is that a device will be lost, whether it's left behind in a rideshare or pilfered as a latte is retrieved from the barista. Either way, your business will have suffered a data breach.Let’s talk about how this outcome can be avoided with some proactive planning, thanks to mobile device management.
Read full post on phantomts.com
Why Information Overload Is Stalling Your Small Business
We’ve been told since we were young that knowledge is power. For entrepreneurs, information is like oxygen. There is a tipping point to having too much data, however, where helpful insight turns into analytical paralysis. If you feel like you’re working harder than ever but your business isn't moving, you might be suffering from information overload. Here is how too much knowledge is actually hurting your bottom line.
We’ve been told since we were young that knowledge is power. For entrepreneurs, information is like oxygen. There is a tipping point to having too much data, however, where helpful insight turns into analytical paralysis. If you feel like you’re working harder than ever but your business isn't moving, you might be suffering from information overload. Here is how too much knowledge is actually hurting your bottom line.
Read full post on phantomts.com
Is That Email Legit? How to Check for These 3 Phishing Red Flags
Most contemporary cyberthreats originate from social engineering. Typically, this involves deceptive phishing messages designed to lure users into compromising their own safety. While these attacks can occur across various platforms, email remains the primary weapon of choice for attackers.To stay protected, let’s examine the key red flags that suggest an email is actually a phishing attempt.
Most contemporary cyberthreats originate from social engineering. Typically, this involves deceptive phishing messages designed to lure users into compromising their own safety. While these attacks can occur across various platforms, email remains the primary weapon of choice for attackers.To stay protected, let’s examine the key red flags that suggest an email is actually a phishing attempt.
Read full post on phantomts.com
How a Custom Email Domain Builds Instant Trust and Authority
Many entrepreneurs start their journey using a free personal email address. While this works for a startup of one, continuing to use generic addresses as you grow creates a significant branding gap. More importantly, it introduces massive security and ownership risks that can jeopardize your company’s future and long-term scalability.
Many entrepreneurs start their journey using a free personal email address. While this works for a startup of one, continuing to use generic addresses as you grow creates a significant branding gap. More importantly, it introduces massive security and ownership risks that can jeopardize your company’s future and long-term scalability.
Read full post on phantomts.com
It Pays to Have a Backup that Hackers Can’t Mess With
Let’s say that today was the day a cyberattack successfully infiltrated your business network. Not good, but if you have a proper data backup, you should be safe… unless the party responsible prioritizes deleting your backup files.While we would never recommend a business skip the data backup process, it is important to recognize that traditional backups have this critical vulnerability. To remedy this, we do recommend implementing immutable backups.
Let’s say that today was the day a cyberattack successfully infiltrated your business network. Not good, but if you have a proper data backup, you should be safe… unless the party responsible prioritizes deleting your backup files.While we would never recommend a business skip the data backup process, it is important to recognize that traditional backups have this critical vulnerability. To remedy this, we do recommend implementing immutable backups.
Read full post on phantomts.com
5 Ways to Use AI as a Business Growth Enhancer
Generative AI is no longer just the cool new thing; it’s a powerful tool for business growth that organizations like yours should be leveraging. If you don’t use AI, you’ll be at a disadvantage compared to your competitors who do, and that’s no good. That said, there’s a massive difference between those who dabble in AI and those who use it masterfully, and that difference is going to grow more significant over time.Today, we’ve got five tips to help you use AI in a proficient way so you can beat out the competition.
Generative AI is no longer just the cool new thing; it’s a powerful tool for business growth that organizations like yours should be leveraging. If you don’t use AI, you’ll be at a disadvantage compared to your competitors who do, and that’s no good. That said, there’s a massive difference between those who dabble in AI and those who use it masterfully, and that difference is going to grow more significant over time.Today, we’ve got five tips to help you use AI in a proficient way so you can beat out the competition.
Read full post on phantomts.com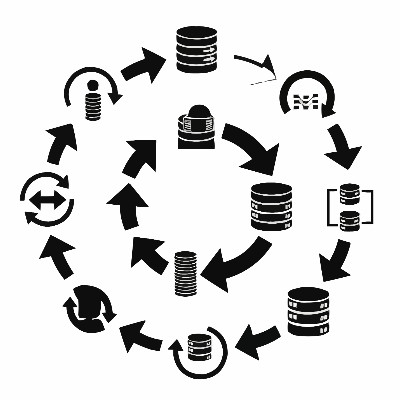
The Business Reality of Hardware Lifecycles
Most business owners treat their office computers like breakroom microwaves: they expect them to work until they physically stop turning on. It’s a logical approach for a toaster, but in the professional world, a computer becomes "old" long before it actually breaks.
Most business owners treat their office computers like breakroom microwaves: they expect them to work until they physically stop turning on. It’s a logical approach for a toaster, but in the professional world, a computer becomes "old" long before it actually breaks.
Read full post on phantomts.com
How to Manage BYOD (Without the Headache)
With smartphones as accessible as they are, it’s no small wonder how company-only policies have all but faded into obscurity in the workplace. Whether you allow it or not, you can bet that your team is using their smartphones to get work done, whether it’s checking email from their couch or sending you a quick DM. In other words, you need a Bring Your Own Device (BYOD) policy, as it is practically the new accepted standard.
With smartphones as accessible as they are, it’s no small wonder how company-only policies have all but faded into obscurity in the workplace. Whether you allow it or not, you can bet that your team is using their smartphones to get work done, whether it’s checking email from their couch or sending you a quick DM. In other words, you need a Bring Your Own Device (BYOD) policy, as it is practically the new accepted standard.
Read full post on phantomts.com
Before You Dispose of Your Hardware, Make Sure You Dispose of Your Data
When the time comes to upgrade any of your business tech, it makes sense that most of your attention would be on maximizing the value you get out of your new hardware. However, it is critical that you also continue to think about your discarded hardware… specifically, the data it contains. In short, deleting files simply isn’t enough. You need to be confident that any information is truly purged or physically destroyed when you’re replacing your hardware.
When the time comes to upgrade any of your business tech, it makes sense that most of your attention would be on maximizing the value you get out of your new hardware. However, it is critical that you also continue to think about your discarded hardware… specifically, the data it contains. In short, deleting files simply isn’t enough. You need to be confident that any information is truly purged or physically destroyed when you’re replacing your hardware.
Read full post on phantomts.com