Wellteck IT
Wellteck IT keeps your technology running smoothly while you focus on your business.

AI-Powered Threats: How They Work and How to Defend Against Them
Cybersecurity is a dynamic and evolving landscape where innovation and technology continuously reshape the boundaries of what's possible, as well as what’s needed. As we talked about in our article about Artificial Intelligence in cybersecurity, AI is a double-edged sword that can be used to protect or as a threat. On one side, AI acts
Cybersecurity is a dynamic and evolving landscape where innovation and technology continuously reshape the boundaries of what's possible, as well as what’s needed. As we talked about in our article about Artificial Intelligence in cybersecurity, AI is a double-edged sword that can be used to protect or as a threat. On one side, AI acts
Read full post on wellteck.com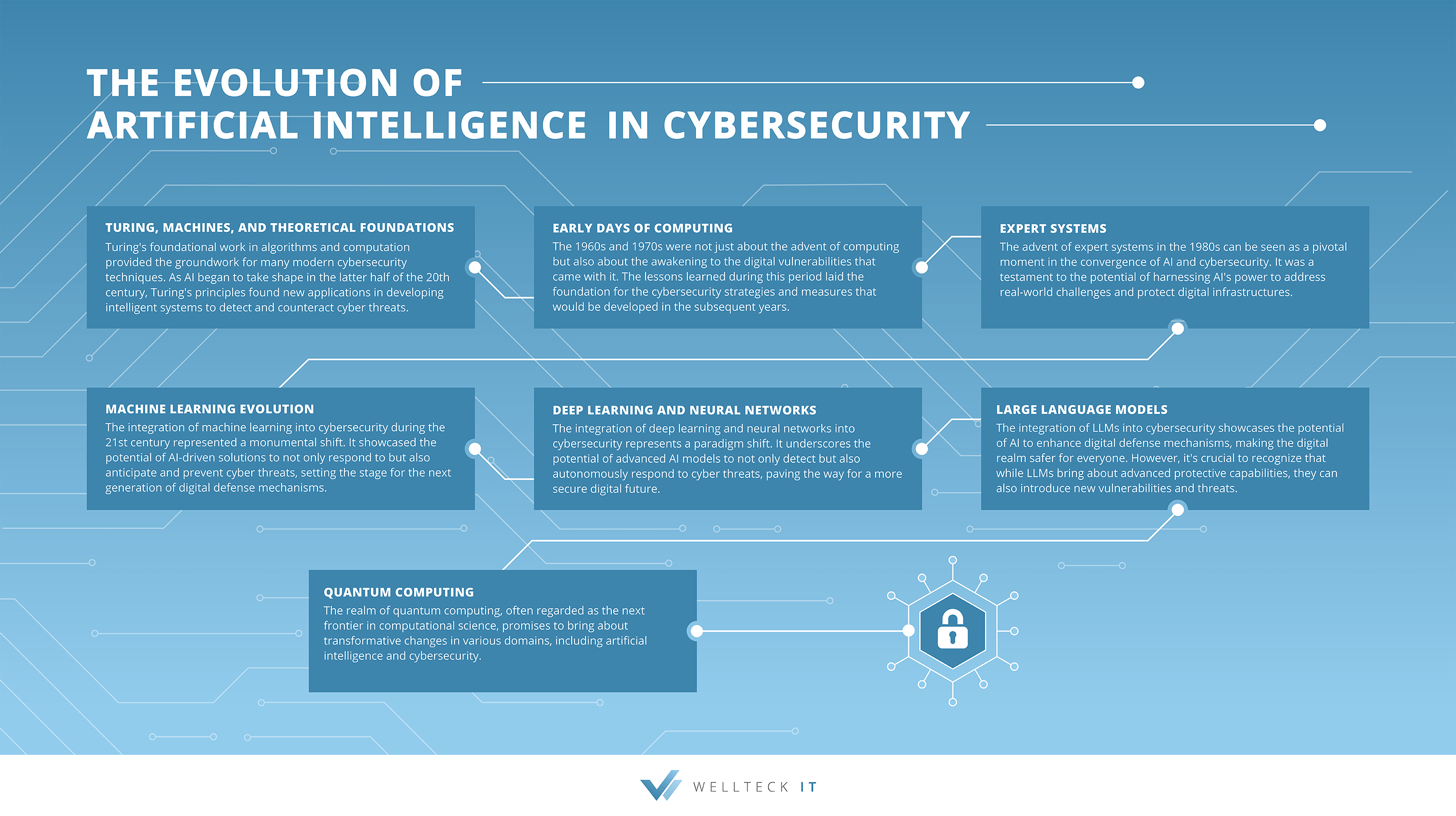
The Evolution of Artificial Intelligence in Cybersecurity
In the ever-evolving landscape of technology, few fields have garnered as much attention and intrigue as Artificial Intelligence (AI) and cybersecurity. Their intertwined journey—from the rudimentary prototypes of the past to the sophisticated systems of today—stands as a testament to human ingenuity and adaptability. This symbiotic relationship has consistently remained at the forefront of technology
In the ever-evolving landscape of technology, few fields have garnered as much attention and intrigue as Artificial Intelligence (AI) and cybersecurity. Their intertwined journey—from the rudimentary prototypes of the past to the sophisticated systems of today—stands as a testament to human ingenuity and adaptability. This symbiotic relationship has consistently remained at the forefront of technology
Read full post on wellteck.com
Wellteck IT Acquired by VC3
COLUMBIA, SC AND MIDLAND, TX - VC3, a market-leading managed service provider serving municipalities, financial services organizations, and commercial businesses across the country, announced today the acquisition of Wellteck IT, a leading provider of enterprise-quality managed IT services, cybersecurity, and IT consulting in Texas. The addition of this established firm further expands the VC3 solution
COLUMBIA, SC AND MIDLAND, TX - VC3, a market-leading managed service provider serving municipalities, financial services organizations, and commercial businesses across the country, announced today the acquisition of Wellteck IT, a leading provider of enterprise-quality managed IT services, cybersecurity, and IT consulting in Texas. The addition of this established firm further expands the VC3 solution
Read full post on wellteck.com
Securing Remote and Home Work Environments
The next normal of work is here. Following the COVID-19 pandemic, the majority of businesses transitioned to remote work settings. Companies found that not only was remote work beneficial for employee health and safety, but it also offered flexibility and potential cost savings. But with every innovation and change, new challenges emerge. As our work
The next normal of work is here. Following the COVID-19 pandemic, the majority of businesses transitioned to remote work settings. Companies found that not only was remote work beneficial for employee health and safety, but it also offered flexibility and potential cost savings. But with every innovation and change, new challenges emerge. As our work
Read full post on wellteck.com
People Protect The Business: The Human Element in Cybersecurity
Introduction As we become more dependent on technology to run our businesses (and our daily lives), the risks associated with cybercrimes continue to rise. It's essential for businesses to recognize the importance of cybersecurity and take the necessary steps to protect themselves now to avoid significant problems in the future. Let’s talk about the important
Introduction As we become more dependent on technology to run our businesses (and our daily lives), the risks associated with cybercrimes continue to rise. It's essential for businesses to recognize the importance of cybersecurity and take the necessary steps to protect themselves now to avoid significant problems in the future. Let’s talk about the important
Read full post on wellteck.com
Cybersecurity Awareness: Enable Multi-Factor Authentication
It’s the last day of Cybersecurity Awareness Month, and today’s action step is a big one… Multi-Factor Authentication. “Remind me what that is again…?” Multi-Factor Authentication (also known as MFA, Two-Factor Authentication, or 2FA) is when a second verification step—your password being the first step—is required to log into an account. The most widely known
It’s the last day of Cybersecurity Awareness Month, and today’s action step is a big one… Multi-Factor Authentication. “Remind me what that is again…?” Multi-Factor Authentication (also known as MFA, Two-Factor Authentication, or 2FA) is when a second verification step—your password being the first step—is required to log into an account. The most widely known
Read full post on wellteck.com
Cybersecurity Awareness: Use Strong Passwords
This week’s action step for Cybersecurity Awareness Month is all about passwords. Everyone’s favorite topic (not really). In fact… …75% of Americans are frustrated with password management. And it makes sense. Every account has different length, strength, and character requirements. Not to mention separate accounts for work and personal use. It’s exhausting. We all know
This week’s action step for Cybersecurity Awareness Month is all about passwords. Everyone’s favorite topic (not really). In fact… …75% of Americans are frustrated with password management. And it makes sense. Every account has different length, strength, and character requirements. Not to mention separate accounts for work and personal use. It’s exhausting. We all know
Read full post on wellteck.com
Cybersecurity Awareness: Update Your Software
We're continuing our series for Cybersecurity Awareness Month focused on several key action steps to protect yourself and your company. Key Action Step #2: Update Your Software There are two types of “updater” personality types… There are the “bleeding edge” updaters and the “if it ain’t broke, don’t fix it” updaters. Truth be told, they
We're continuing our series for Cybersecurity Awareness Month focused on several key action steps to protect yourself and your company. Key Action Step #2: Update Your Software There are two types of “updater” personality types… There are the “bleeding edge” updaters and the “if it ain’t broke, don’t fix it” updaters. Truth be told, they
Read full post on wellteck.com
Cybersecurity Awareness: Think Before You Click
This is the first of several key action steps to protect yourself and your business from cyber attacks as we go through Cybersecurity Awareness Month. Key Action Step #1: Think Before You Click Known as “phishing attacks”, clicking deceptive, fake, or malicious links is the most common type of cyber attack, accounting for over 80%
This is the first of several key action steps to protect yourself and your business from cyber attacks as we go through Cybersecurity Awareness Month. Key Action Step #1: Think Before You Click Known as “phishing attacks”, clicking deceptive, fake, or malicious links is the most common type of cyber attack, accounting for over 80%
Read full post on wellteck.com
How To Stop Thinking About Your IT (The Right Way)
Introduction The more you have to think about your IT, the less it’s doing its job. Like most business owners and executives, you have a lot of areas demanding your attention. You have employees to lead, customers to serve, and products and services to deliver. Unless you’re an IT company, you probably didn’t go into
Introduction The more you have to think about your IT, the less it’s doing its job. Like most business owners and executives, you have a lot of areas demanding your attention. You have employees to lead, customers to serve, and products and services to deliver. Unless you’re an IT company, you probably didn’t go into
Read full post on wellteck.com