RESULTS Technology
Choose the best IT support option below.
Our team of experienced IT experts works with you to develop a cohesive technology support plan specifically designed to move your business forward.

How Fidelity State Bank Achieved IT Compliance Success
“That was an eye-opening … learning experience, knowing that [RESULTS Technology] was working behind the scenes to make sure that we were kept up to date, compliant, and secure.” —Noel Gaucin, VP Loan Officer for Fidelity State Bank & Trust Company Running a community bank is all about striking the right balance: delivering great service
“That was an eye-opening … learning experience, knowing that [RESULTS Technology] was working behind the scenes to make sure that we were kept up to date, compliant, and secure.” —Noel Gaucin, VP Loan Officer for Fidelity State Bank & Trust Company Running a community bank is all about striking the right balance: delivering great service
Read full post on resultstechnology.com
How to Run a Bank Incident Response Tabletop Exercise That Actually Improves Readiness
An incident response tabletop exercise is a structured, interactive discussion where a team walks through a simulated security threat to evaluate and improve their incident response plan. It allows staff to practice their roles in a low-stress environment, identifying gaps in communication, technical controls, and procedures before a real crisis occurs. Federal and state examiners
An incident response tabletop exercise is a structured, interactive discussion where a team walks through a simulated security threat to evaluate and improve their incident response plan. It allows staff to practice their roles in a low-stress environment, identifying gaps in communication, technical controls, and procedures before a real crisis occurs. Federal and state examiners
Read full post on resultstechnology.com
What Remote Banking Means for Community Bank IT Infrastructure
Customers love the convenience of remote banking. Whether they are depositing a birthday check from their kitchen table or checking their account balance from the couch at midnight, they expect seamless access to their money. For a community bank, providing this level of convenience is a fantastic way to build loyalty. However, it also introduces
Customers love the convenience of remote banking. Whether they are depositing a birthday check from their kitchen table or checking their account balance from the couch at midnight, they expect seamless access to their money. For a community bank, providing this level of convenience is a fantastic way to build loyalty. However, it also introduces
Read full post on resultstechnology.com
7 IT Documents Community Banks Need Ready for Exams
Bank exams can cause unnecessary stress, especially when examiners start asking for your IT paperwork. Regulators want to see undeniable proof that your community bank actively manages its cybersecurity and network infrastructure. They are looking for clear, organized, and updated records that show you have a handle on potential risks. Achieving regulatory compliance in banking
Bank exams can cause unnecessary stress, especially when examiners start asking for your IT paperwork. Regulators want to see undeniable proof that your community bank actively manages its cybersecurity and network infrastructure. They are looking for clear, organized, and updated records that show you have a handle on potential risks. Achieving regulatory compliance in banking
Read full post on resultstechnology.com
How to Identify Blind Spots in Your Bank’s Security Monitoring Tools
Running a community bank means wearing a lot of hats, but keeping customer data safe is always at the top of the list. Even with the best intentions, monitoring blind spots poses a serious risk to your institution. Cyber threats evolve constantly, frequently shifting their capabilities and targets to bypass standard defenses. On top of
Running a community bank means wearing a lot of hats, but keeping customer data safe is always at the top of the list. Even with the best intentions, monitoring blind spots poses a serious risk to your institution. Cyber threats evolve constantly, frequently shifting their capabilities and targets to bypass standard defenses. On top of
Read full post on resultstechnology.com
Which Bank Security Controls Matter Most to Cyber Insurance and Why?
Remember when renewing your bank’s insurance policy felt like a formality? You’d sign a few papers, pay the premium, and get back to serving your customers. Those days are gone. Today, the questionnaire for cyber insurance for banks can feel more like a full-scope audit than a simple renewal application. Insurers have paid out massive
Remember when renewing your bank’s insurance policy felt like a formality? You’d sign a few papers, pay the premium, and get back to serving your customers. Those days are gone. Today, the questionnaire for cyber insurance for banks can feel more like a full-scope audit than a simple renewal application. Insurers have paid out massive
Read full post on resultstechnology.com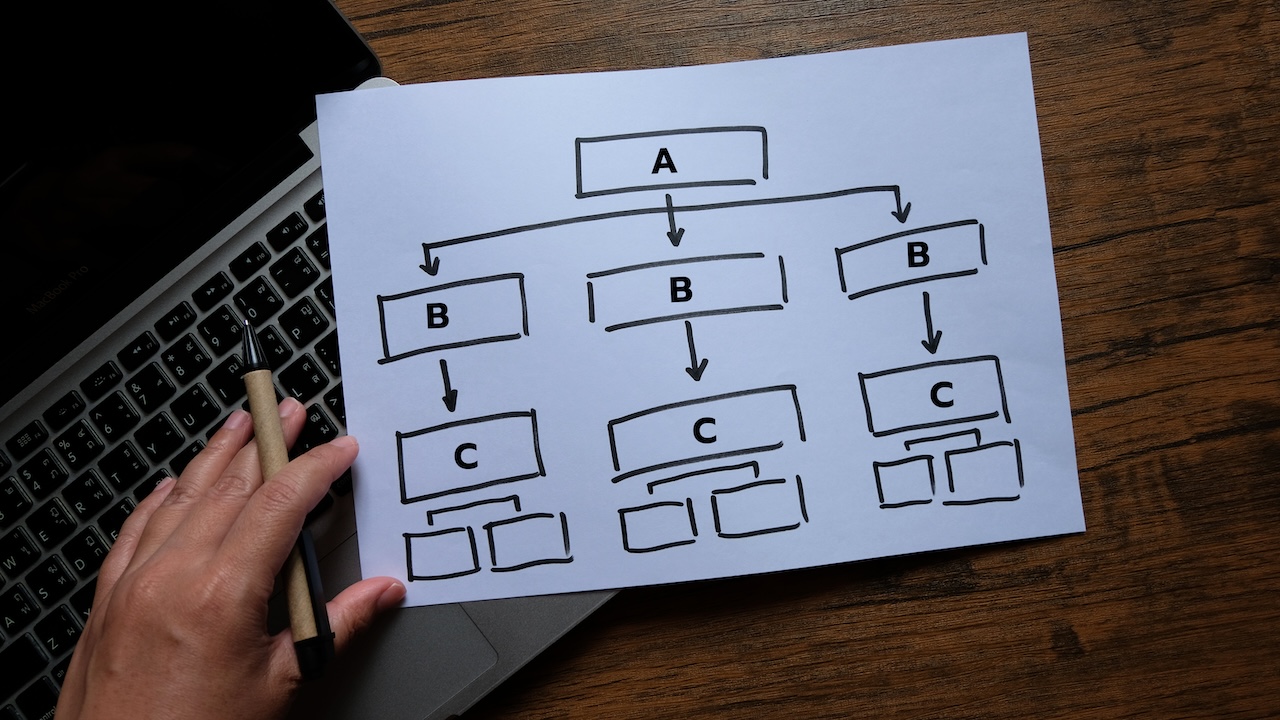
How to Build a Data Flow Diagram That Actually Helps During an IT Exam
The notification just landed in your inbox: the examiners are coming. For many community bank IT officers, this moment triggers a scramble to update policies, gather logs, and double-check vendor contracts. But there is one document that often gets overlooked until the last minute—your network diagram. More specifically, your data flow diagram. It’s easy to
The notification just landed in your inbox: the examiners are coming. For many community bank IT officers, this moment triggers a scramble to update policies, gather logs, and double-check vendor contracts. But there is one document that often gets overlooked until the last minute—your network diagram. More specifically, your data flow diagram. It’s easy to
Read full post on resultstechnology.com