Sirkit
Choose the best IT support option below.
Our unified team of certified storage, server, network, security, and desktop analysts are committed to fully managing, supporting, and monitoring everything.
We work directly alongside our clients to gauge life-cycles, replacement costs, budgets, streamline processes, increase efficiencies through the use of new technologies, and make educated decisions that support long-term business strategies.
Our rapid growth is a direct result of maintaining tight-knit relationships with our clients, and pushing our team to learn and challenge new technology.
We like to think that SIRKit will be the last IT partner you ever have.

AI Cyber Attacks: What Business Leaders Need to Understand Right Now
Artificial intelligence has fundamentally changed how cybercriminals operate. AI cyber attacks use machine learning to bypass traditional security measures, targeting businesses through automated phishing campaigns, deepfake fraud, and intelligent malware that adapts in real-time.
Artificial intelligence has fundamentally changed how cybercriminals operate. AI cyber attacks use machine learning to bypass traditional security measures, targeting businesses through automated phishing campaigns, deepfake fraud, and intelligent malware that adapts in real-time.
Read full post on sirkit.ca
Vulnerability Assessment vs Penetration Testing
When it comes to protecting your business from cyber threats, two security testing methods stand out: vulnerability assessments and penetration testing. While both help identify security weaknesses, they serve very different purposes and provide distinct value to your organization.
When it comes to protecting your business from cyber threats, two security testing methods stand out: vulnerability assessments and penetration testing. While both help identify security weaknesses, they serve very different purposes and provide distinct value to your organization.
Read full post on sirkit.ca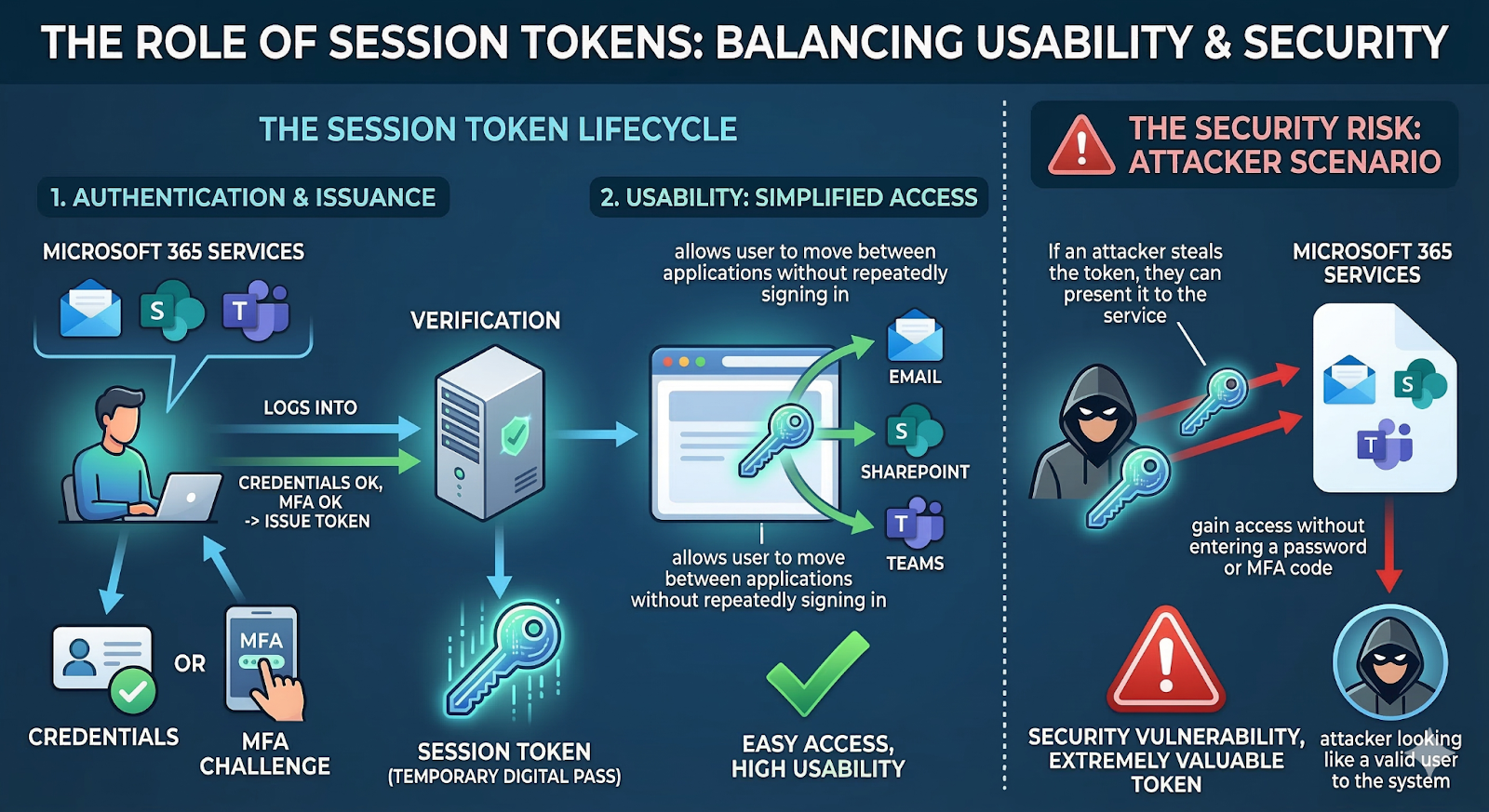
How to Prevent Token Theft and AiTM Attacks
For many organizations, multi-factor authentication (MFA) has become the baseline defense against cyber threats. If employees must verify their identity with a second factor such as a phone approval or one-time code, the assumption is that attackers cannot get in.
For many organizations, multi-factor authentication (MFA) has become the baseline defense against cyber threats. If employees must verify their identity with a second factor such as a phone approval or one-time code, the assumption is that attackers cannot get in.
Read full post on sirkit.ca
On-Premise to Cloud Migration: Understanding the New Security Framework
Cloud migration doesn’t just change where your systems live. It changes how security works.
Cloud migration doesn’t just change where your systems live. It changes how security works.
Read full post on sirkit.ca![What’s the Cost of Managed IT Services? [2026 Update]](/storage/images/posts/2026/02/whats-the-cost-of-managed-it-services-2026-update.png)
What’s the Cost of Managed IT Services? [2026 Update]
When executives ask about the cost of Managed IT Services, they’re usually looking for a number they can confidently budget against. That’s fair.
When executives ask about the cost of Managed IT Services, they’re usually looking for a number they can confidently budget against. That’s fair.
Read full post on sirkit.ca
What Does Cyber Insurance Cover
Cyber insurance can help absorb the financial impact of a cyber incident, but it’s conditional. What gets paid depends on how the policy defines a covered event, which security controls were in place, and whether the incident unfolded the way the insurer expects.
Cyber insurance can help absorb the financial impact of a cyber incident, but it’s conditional. What gets paid depends on how the policy defines a covered event, which security controls were in place, and whether the incident unfolded the way the insurer expects.
Read full post on sirkit.ca
Building a Resilient IT Infrastructure for 30+ Employee Organizations: A Practical Blueprint
At 10 employees, a few quick fixes and “we’ll deal with it later” habits can keep things moving, until you hit the point where managed IT services become the difference between scaling smoothly and constant firefighting.
At 10 employees, a few quick fixes and “we’ll deal with it later” habits can keep things moving, until you hit the point where managed IT services become the difference between scaling smoothly and constant firefighting.
Read full post on sirkit.ca
The New Vendor Fraud Playbook (and How to Stop It)
Vendor impersonation scams are no longer just an accounts payable problem but part of broader governance risks facing leadership teams.
Vendor impersonation scams are no longer just an accounts payable problem but part of broader governance risks facing leadership teams.
Read full post on sirkit.ca
Why IT Spend Feels Unpredictable, and How CFOs Can Stabilize It
IT has become one of the largest and most volatile operating expenses in mid-market organizations. Cloud, SaaS, cybersecurity, and licensing all scale with usage, not approvals, which creates significant variance month to month.
IT has become one of the largest and most volatile operating expenses in mid-market organizations. Cloud, SaaS, cybersecurity, and licensing all scale with usage, not approvals, which creates significant variance month to month.
Read full post on sirkit.ca