Thrive
Choose the best IT support option below.
Thrive’s NextGen platform enables customers to increase business efficiencies through standardization, scalability, and automation, delivering oversized technology returns on investment (ROI).
They accomplish this with advisory services, vCISO, vCIO, consulting, project implementation, solution architects, and a best-in-class subscription-based technology platform.
Thrive delivers exceptional high-touch service through its POD approach of subject matter experts and global 24x7x365 SOC, NOC, and centralized services teams.

The need for the human touch in an AI-dominated world
The famous American author Mark Twain is reported to have written to the New York Journal in June 1897 after several newspapers had claimed he was gravely ill or dead, stating: “Reports of my death…
The famous American author Mark Twain is reported to have written to the New York Journal in June 1897 after several newspapers had claimed he was gravely ill or dead, stating: “Reports of my death…
Read full post on computerweekly.com
Thrive CFO on standing out in a ‘fragmented’ IT marketplace
Matt Kosovksy’s path to a permanent CFO seat came after nearly a decade in leadership at employee-owned private equity firm Berkshire Partners. In January, he officially stepped into the top financial job at IT managed…
Matt Kosovksy’s path to a permanent CFO seat came after nearly a decade in leadership at employee-owned private equity firm Berkshire Partners. In January, he officially stepped into the top financial job at IT managed…
Read full post on cfo.com
Before you run with AI, you must crawl the hard yards and learn to walk
“We must do something with AI” is increasingly what passes for strategy in many boardrooms and in discussions among frontline employees. Almost everyone feels the pressure to use AI – they’re just not sure what…
“We must do something with AI” is increasingly what passes for strategy in many boardrooms and in discussions among frontline employees. Almost everyone feels the pressure to use AI – they’re just not sure what…
Read full post on node-magazine.com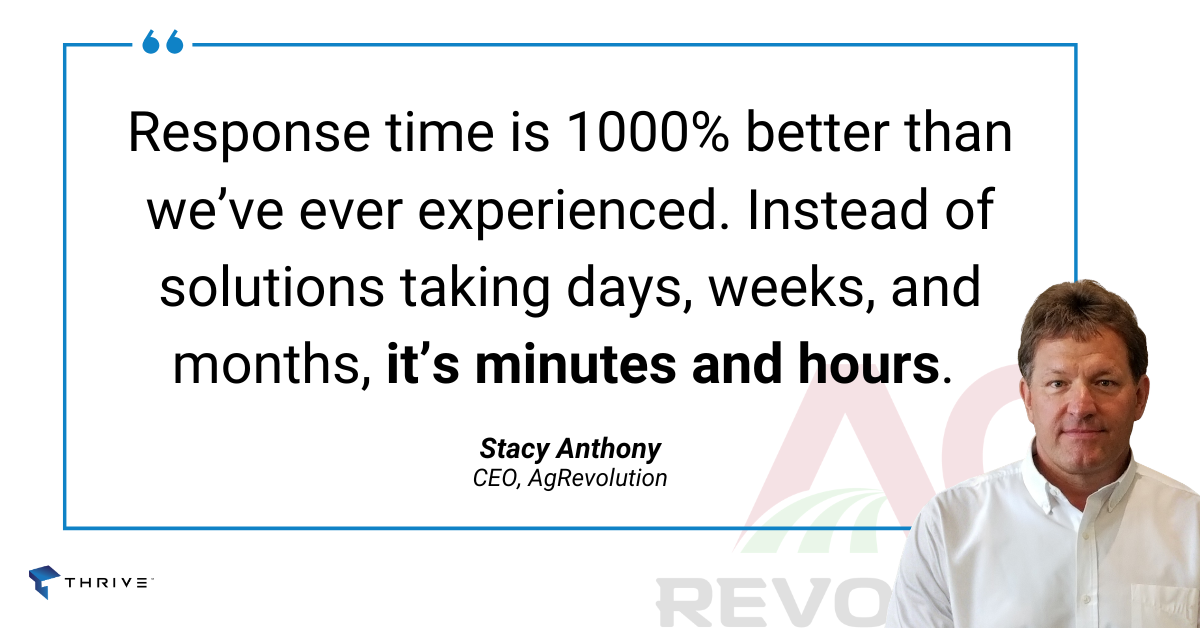
From Island to Partner: AgRevolution’s Growth Through Strategic Technology Alignment
AgRevolution arrived in the agricultural equipment industry with bold intentions. Founded in January 2021 and based in Evansville, Indiana, the company was built on a mission to fill market gaps left by competitors exiting…
AgRevolution arrived in the agricultural equipment industry with bold intentions. Founded in January 2021 and based in Evansville, Indiana, the company was built on a mission to fill market gaps left by competitors exiting…
Read full post on thrivenextgen.com
British businesses are being dragged into cyber wars they never signed up for
They’re not getting involved in making foreign policy decisions or building weapons systems. They’re just running their business. But in the current threat environment, that difference is becoming ever more irrelevant. State-aligned threat actors are…
They’re not getting involved in making foreign policy decisions or building weapons systems. They’re just running their business. But in the current threat environment, that difference is becoming ever more irrelevant. State-aligned threat actors are…
Read full post on lbc.co.uk
Modern Microsoft 365 Governance for the AI Era: A Thrive Perspective
Strong governance has always served as the cornerstone of a secure, efficient, and well-managed digital workplace. Microsoft 365 has become the primary productivity platform for most organizations; however, without deliberate and effective governance, even robust…
Strong governance has always served as the cornerstone of a secure, efficient, and well-managed digital workplace. Microsoft 365 has become the primary productivity platform for most organizations; however, without deliberate and effective governance, even robust…
Read full post on thrivenextgen.com
The Comma that Broke the Internet: Inside the cPanel Infrastructure Meltdown
The Day the Keys to the Kingdom Went Missing In the quiet architecture of the internet, cPanel and WebHost Manager (WHM) serve as the management plane the largely invisible interface where the digital world is…
The Day the Keys to the Kingdom Went Missing In the quiet architecture of the internet, cPanel and WebHost Manager (WHM) serve as the management plane the largely invisible interface where the digital world is…
Read full post on thrivenextgen.com