CCI Managed Services
Today our experts monitor and manage over 100 business networks ranging in size from a few desktops to nearly a thousand. By working with organizations of all sizes, we have gained valuable experience and a unique perspective.
We believe in cross-pollination; if we see something working well for one client, we offer solutions that we know work for other clients with similar needs. We follow known recipes for IT solutions, so that we can guarantee results and a strong return on investment.
Information Technology is constantly changing! Our emphasis on continued learning helps to keep our technicians sharp and able to competently deploy today’s solutions.
Our team possess a wide variety of certifications, including A+, Security +, Server +, and multiple IBM, Lenovo, Intel, and Microsoft certifications. But what really sets our technicians apart isn’t just their training and experience. They also possess the ability to listen and communicate both with technical and non-technical people.
We aren’t just technology providers; we believe in working with clients to find solutions to their IT and business needs.
Our deep, meaningful relationships with vendor partners allow us to offer and support best-of-breed solutions to our clients.
If an issue or problem occurs, these strategic partnerships give us the upper hand over competitors. We know where and who to go to obtain ultimate satisfaction for our clients.

Network Security: If People Are the Problem, People Are the Solution
Cybersecurity conversations often focus on the latest tools, platforms, firewalls, monitoring systems, and threat detection technologies. All of those matter. A secure business network absolutely depends on strong technical defenses. But even the best-protected network still has human access points. Employees open emails. They click links. They approve requests. They use passwords. They access cloud… Read More »
Cybersecurity conversations often focus on the latest tools, platforms, firewalls, monitoring systems, and threat detection technologies. All of those matter. A secure business network absolutely depends on strong technical defenses. But even the best-protected network still has human access points. Employees open emails. They click links. They approve requests. They use passwords. They access cloud… Read More »
Read full post on ccimanaged.com
Why Complete Care IT Services Should Replace Traditional Methods of IT Support
The IT Managed Service Provider Market Expands The challenge facing businesses and municipalities everywhere is how to operate securely, efficiently, and confidently in an era when technology risks and complexity continue to grow and threaten productivity. From small professional offices and manufacturers to school districts and town halls across New Hampshire and Vermont, organizations are… Read More »
The IT Managed Service Provider Market Expands The challenge facing businesses and municipalities everywhere is how to operate securely, efficiently, and confidently in an era when technology risks and complexity continue to grow and threaten productivity. From small professional offices and manufacturers to school districts and town halls across New Hampshire and Vermont, organizations are… Read More »
Read full post on ccimanaged.com
EDR and ITDR Strengthen Your Cybersecurity Defense Posture
The Need to Move beyond MFA You know the basics of cybersecurity – strong passwords, multi-factor authentication (MFA), antivirus software, and firewalls. These are still important lines of defense, but as cyber threats have evolved past MFA, so must your protection strategy. Thankfully, advanced technologies such as Endpoint Detection and Response (EDR) and Identity Threat… Read More »
The Need to Move beyond MFA You know the basics of cybersecurity – strong passwords, multi-factor authentication (MFA), antivirus software, and firewalls. These are still important lines of defense, but as cyber threats have evolved past MFA, so must your protection strategy. Thankfully, advanced technologies such as Endpoint Detection and Response (EDR) and Identity Threat… Read More »
Read full post on ccimanaged.com
A New PC is the Better Choice for a Windows 11 Upgrade
As Microsoft has announced the end of support for Windows 10 on October 14, 2025, urgency grows among users of older devices. Upgrading to Windows 11 is not just an option, it’s an imperative for maintaining security, performance, and compatibility. But simply upgrading the software may fall short of delivering the benefits and stability of… Read More »
As Microsoft has announced the end of support for Windows 10 on October 14, 2025, urgency grows among users of older devices. Upgrading to Windows 11 is not just an option, it’s an imperative for maintaining security, performance, and compatibility. But simply upgrading the software may fall short of delivering the benefits and stability of… Read More »
Read full post on ccimanaged.com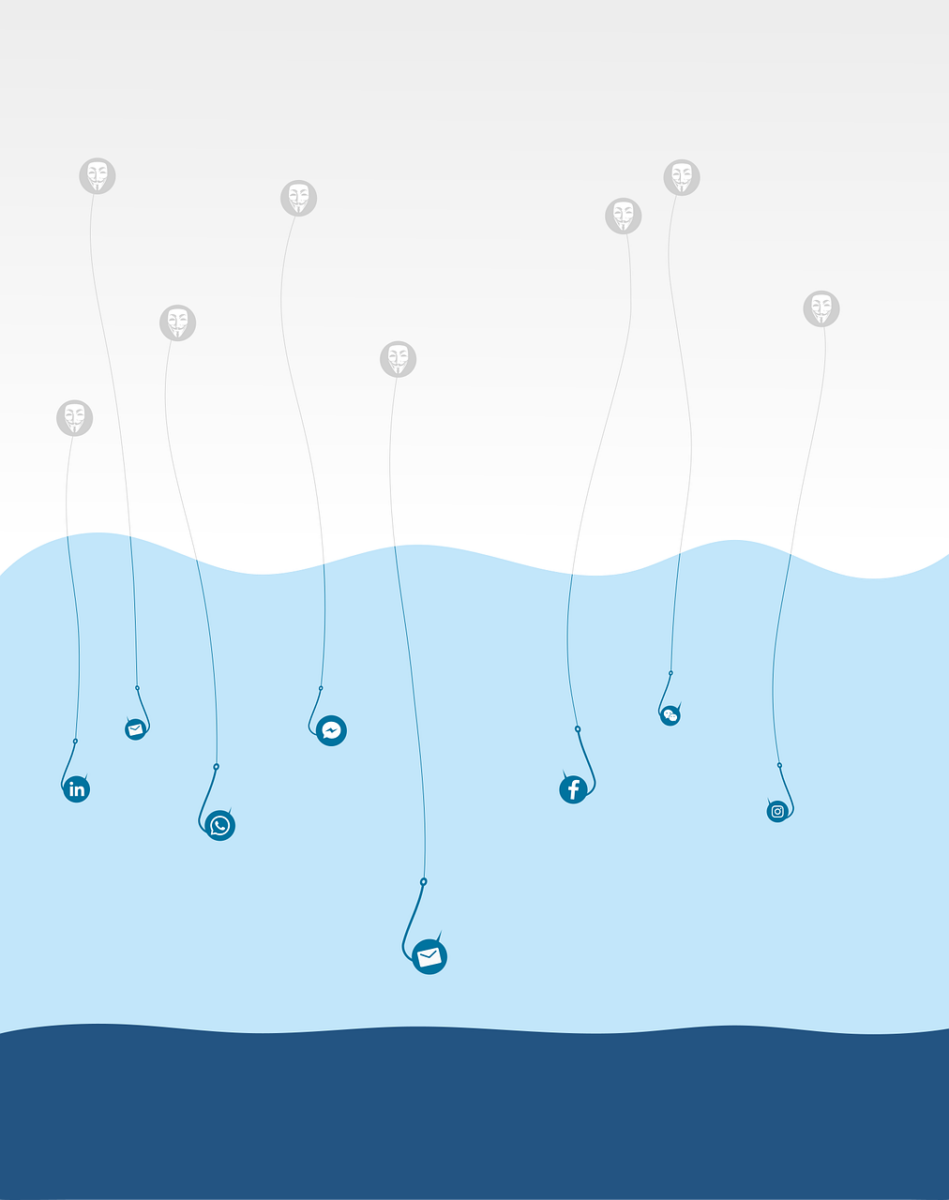
Smart Phishing Emails: If You Take the Bait, it’s Too Late!
Bolder and smarter describe today’s email hackers. One of the most common and dangerous tactics they use is phishing, and it’s only becoming harder to detect. No longer do we see the obvious scam emails full of spelling mistakes and bad grammar. The scam artists have learned and are now carefully crafting messages that appear… Read More »
Bolder and smarter describe today’s email hackers. One of the most common and dangerous tactics they use is phishing, and it’s only becoming harder to detect. No longer do we see the obvious scam emails full of spelling mistakes and bad grammar. The scam artists have learned and are now carefully crafting messages that appear… Read More »
Read full post on ccimanaged.com
Empowering New Hampshire and Vermont Municipalities with Secure IT Solutions
In todayâs digital landscape, municipalities face growing challenges in managing their IT networks and ensuring robust cybersecurity. Towns and cities everywhere need dependable technology solutions to protect sensitive data, ensure operational continuity, and serve their communities effectively. Now smaller towns are becoming bigger targets because of both real and perceived security vulnerabilities. CCI Managed Services⦠Read More »
In todayâs digital landscape, municipalities face growing challenges in managing their IT networks and ensuring robust cybersecurity. Towns and cities everywhere need dependable technology solutions to protect sensitive data, ensure operational continuity, and serve their communities effectively. Now smaller towns are becoming bigger targets because of both real and perceived security vulnerabilities. CCI Managed Services⦠Read More »
Read full post on ccimanaged.com
The Growing Imperative of Managed IT Security for Small and Medium Enterprises
Small Business and Big Threats The integrity and security of data are now paramount concerns for businesses of all sizes. Recent high-profile incidents, such as the CrowdStrike outage and the CDK data security breach, have underscored the vulnerabilities that large enterprises face. However, small and medium enterprises (SMEs) are often at a greater risk due⦠Read More »
Small Business and Big Threats The integrity and security of data are now paramount concerns for businesses of all sizes. Recent high-profile incidents, such as the CrowdStrike outage and the CDK data security breach, have underscored the vulnerabilities that large enterprises face. However, small and medium enterprises (SMEs) are often at a greater risk due⦠Read More »
Read full post on ccimanaged.com
The Layman’s Guide to Managed IT Services
Technology plays a vital role in shaping the success of businesses including yours, mine and everyone else’s. Managing and maintaining that technology means commandeering complex IT systems which is a daunting or impossible task for someone without formal training. This is where Managed IT Services come into play. Let’s break down what managed IT services⦠Read More »
Technology plays a vital role in shaping the success of businesses including yours, mine and everyone else’s. Managing and maintaining that technology means commandeering complex IT systems which is a daunting or impossible task for someone without formal training. This is where Managed IT Services come into play. Let’s break down what managed IT services⦠Read More »
Read full post on ccimanaged.com
The Layman’s Guide to Managed IT Services
Technology plays a vital role in shaping the success of businesses including yours, mine and everyone else’s. Managing and maintaining that technology means commandeering complex IT systems which is a daunting or impossible task for someone without formal training. This is where Managed IT Services come into play. Let’s break down what managed IT services⦠Read More »
Technology plays a vital role in shaping the success of businesses including yours, mine and everyone else’s. Managing and maintaining that technology means commandeering complex IT systems which is a daunting or impossible task for someone without formal training. This is where Managed IT Services come into play. Let’s break down what managed IT services⦠Read More »
Read full post on ccimanaged.com