Mindcore Technologies
As world-class subject matter experts in applied information technologies, we focus on relevant & high impact client solutions & endeavor to maintain an unmatched commitment to the highest standards in technology infrastructure and discipline.
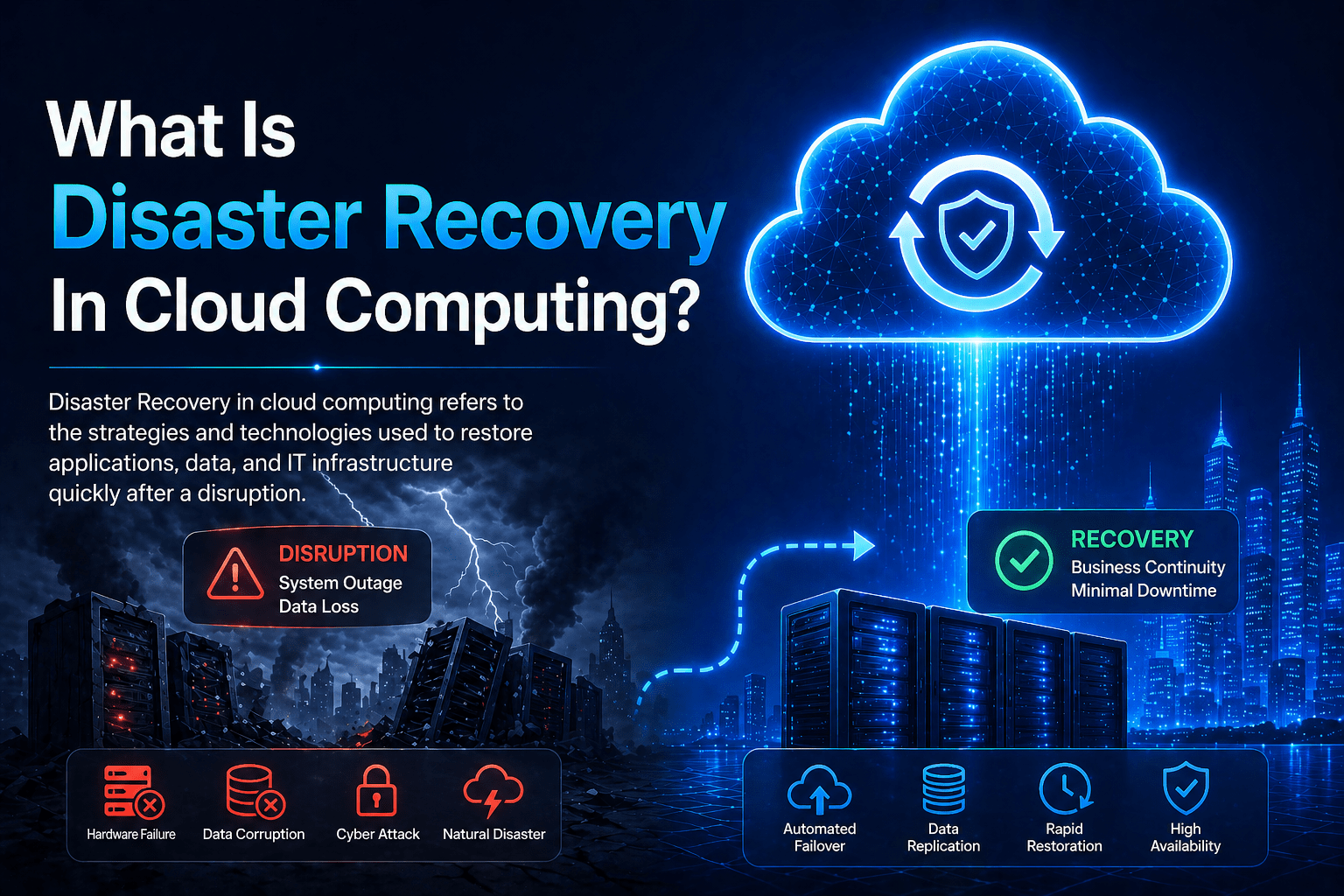
What Is Disaster Recovery In Cloud Computing?
Disaster recovery in cloud computing refers to the strategies, technologies, and processes that use cloud infrastructure to restore IT systems and business operations following a disruptive event. It encompasses everything from how data is replicated to secondary cloud locations, to how systems are recovered and operational in the event of a significant failure. Cloud computing
Disaster recovery in cloud computing refers to the strategies, technologies, and processes that use cloud infrastructure to restore IT systems and business operations following a disruptive event. It encompasses everything from how data is replicated to secondary cloud locations, to how systems are recovered and operational in the event of a significant failure. Cloud computing
Read full post on mind-core.com
What Is Cloud Disaster Recovery?
Cloud disaster recovery (cloud DR) is the use of cloud infrastructure and services to restore IT systems and data after a significant failure event — a ransomware attack, a natural disaster, a major hardware failure, or any other event that renders primary systems unavailable. Disaster recovery is distinct from backup. Backup preserves data. Disaster recovery
Cloud disaster recovery (cloud DR) is the use of cloud infrastructure and services to restore IT systems and data after a significant failure event — a ransomware attack, a natural disaster, a major hardware failure, or any other event that renders primary systems unavailable. Disaster recovery is distinct from backup. Backup preserves data. Disaster recovery
Read full post on mind-core.com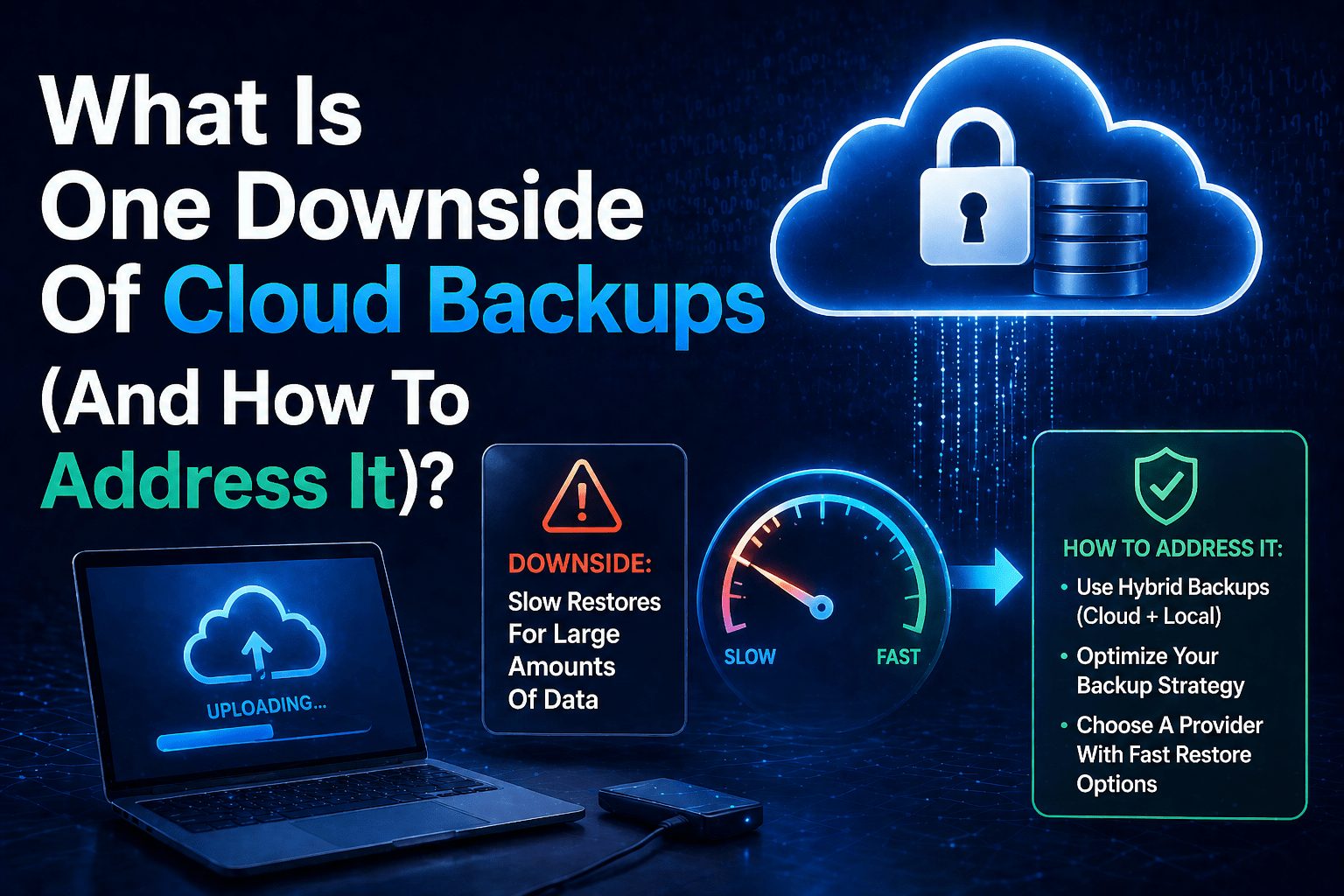
What Is One Downside Of Cloud Backups (And How To Address It)?
Cloud backup has clear advantages: geographic separation, ransomware resilience, automatic scaling, and reduced hardware management overhead. But it has a significant operational limitation that organizations frequently underestimate until a recovery event makes it concrete: recovery speed. Restoring large volumes of data from cloud storage over an internet connection is slow. How slow depends on data
Cloud backup has clear advantages: geographic separation, ransomware resilience, automatic scaling, and reduced hardware management overhead. But it has a significant operational limitation that organizations frequently underestimate until a recovery event makes it concrete: recovery speed. Restoring large volumes of data from cloud storage over an internet connection is slow. How slow depends on data
Read full post on mind-core.com