Managed Service Providers in New Jersey, USA

AI Data Governance Field Guide: 5 AI Best Practices to Protect Your Org
IT and security leaders are often feeling pressure to deploy AI tools faster than the organization is ready for them. As a result, what starts off as AI agent integration and AI-assisted workflow leads to terabytes of sensitive information flowing through systems that employees assume are secure.
IT and security leaders are often feeling pressure to deploy AI tools faster than the organization is ready for them. As a result, what starts off as AI agent integration and AI-assisted workflow leads to terabytes of sensitive information flowing through systems that employees assume are secure.
Read full post on allcovered.com
How Power Delays Break Construction WIP for Data Center Contractors
Grid interconnection delays and long-lead equipment can throw construction WIP reporting out of alignment. For data center contractors, the result can be inaccurate percent-complete calculations, cash flow strain, audit risk, and lost backlog opportunities.
Grid interconnection delays and long-lead equipment can throw construction WIP reporting out of alignment. For data center contractors, the result can be inaccurate percent-complete calculations, cash flow strain, audit risk, and lost backlog opportunities.
Read full post on swktech.com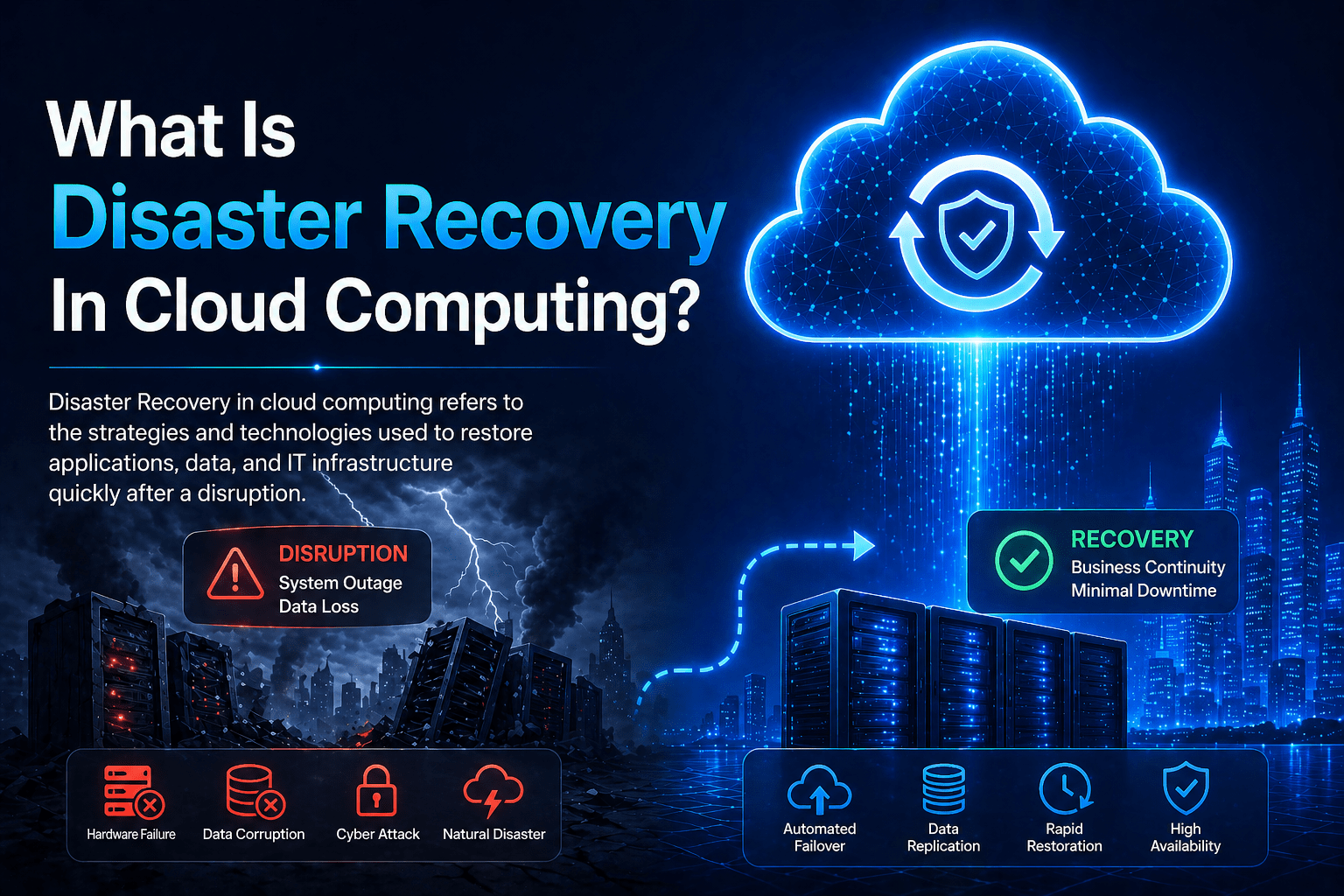
What Is Disaster Recovery In Cloud Computing?
Disaster recovery in cloud computing refers to the strategies, technologies, and processes that use cloud infrastructure to restore IT systems and business operations following a disruptive event. It encompasses everything from how data is replicated to secondary cloud locations, to how systems are recovered and operational in the event of a significant failure. Cloud computing
Disaster recovery in cloud computing refers to the strategies, technologies, and processes that use cloud infrastructure to restore IT systems and business operations following a disruptive event. It encompasses everything from how data is replicated to secondary cloud locations, to how systems are recovered and operational in the event of a significant failure. Cloud computing
Read full post on mind-core.com