Wolf Technology Group
Wolf Technology Group is a small business offering a full range of IT Support and Business Technology services to commercial and government clients in the greater Atlanta, GA and Greenville, SC area.
With expertise in IT support, data management, computer support, project management services, secure email administration, Office 365 services and network support, our information technology professionals are ready to assist your organization with complete information systems technical support solutions, and all of your project management needs.
Call Wolf Technology Group today at (833) 482-6435 or contact us online to discuss how we can provide solutions for your company tailored to your specific needs.
AI Consulting
AI Consulting AI consulting for small businesses is about getting practical results for fast—automating repetitive
AI Consulting AI consulting for small businesses is about getting practical results for fast—automating repetitive
Read full post on wolftg.com
Best Practices Against Phishing
What is Phishing According to IBM, phishing attacks are fraudulent emails, text messages, phone calls
What is Phishing According to IBM, phishing attacks are fraudulent emails, text messages, phone calls
Read full post on wolftg.com
Common Phishing Attacks: Pharming
As users become wiser to traditional phishing scams, some fraudsters are abandoning the idea of
As users become wiser to traditional phishing scams, some fraudsters are abandoning the idea of
Read full post on wolftg.com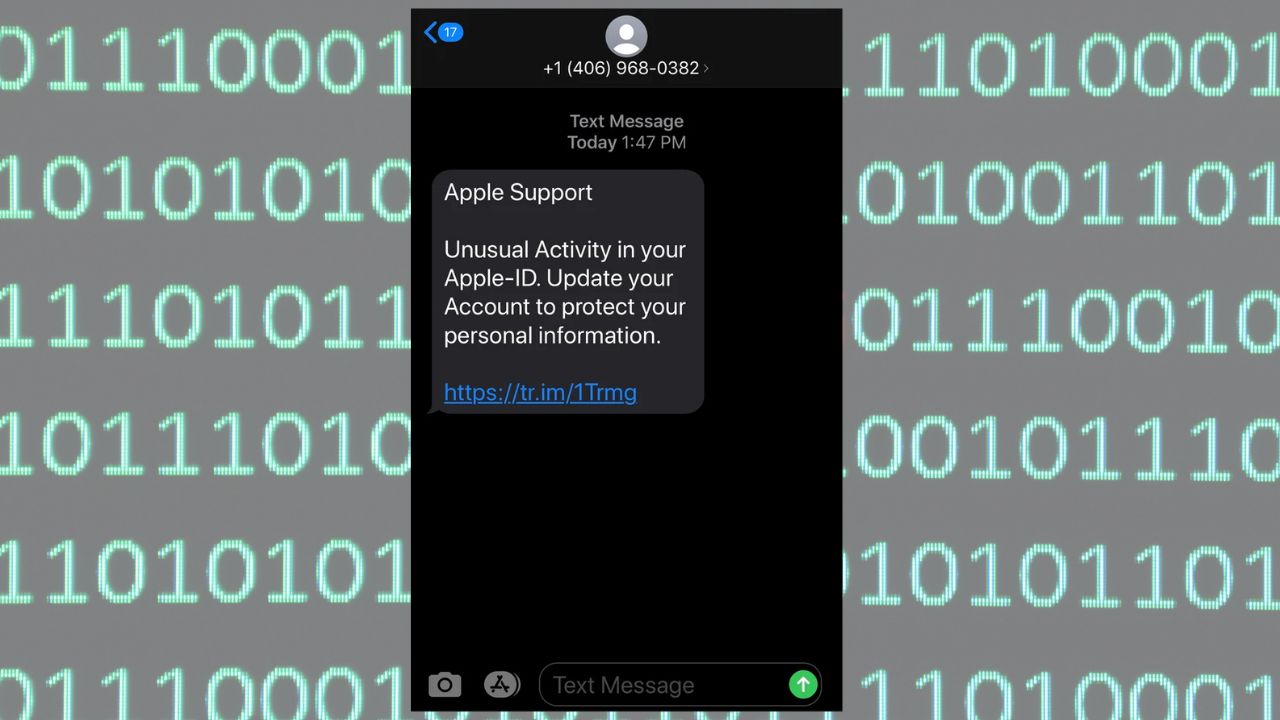
Common Phishing Attacks: Smishing
Vishing is not the only type of phishing that digital fraudsters can perpetrate using a
Vishing is not the only type of phishing that digital fraudsters can perpetrate using a
Read full post on wolftg.com
Common Phishing Attacks: Vishing
Until now, we have discussed phishing attacks that for the most part rely solely on
Until now, we have discussed phishing attacks that for the most part rely solely on
Read full post on wolftg.com
Common Phishing Attacks: Whaling Attacks
Whaling attacks commonly make use of the same techniques as spear phishing campaigns. Here are
Whaling attacks commonly make use of the same techniques as spear phishing campaigns. Here are
Read full post on wolftg.com
Common Phishing Attacks: Spear Phishing
Not all phishing scams embrace âspray and prayâ techniques. Some ruses rely more on a
Not all phishing scams embrace âspray and prayâ techniques. Some ruses rely more on a
Read full post on wolftg.com
Common Phishing Attacks: Deceptive Phishing
Phishing Phishing attacks continue to play a dominant role in the digital threat landscape. In
Phishing Phishing attacks continue to play a dominant role in the digital threat landscape. In
Read full post on wolftg.com
Phishing Scams and How to Recognize Them
Phishing Scams and How to Recognize Them Scammers use email or text messages called phishing
Phishing Scams and How to Recognize Them Scammers use email or text messages called phishing
Read full post on wolftg.com
The Business of Ransomware
The Business of Ransomware As a refresher, ransomware is a malware that is activated by
The Business of Ransomware As a refresher, ransomware is a malware that is activated by
Read full post on wolftg.com