How AT&T’s 1993 Ads Saw the Future
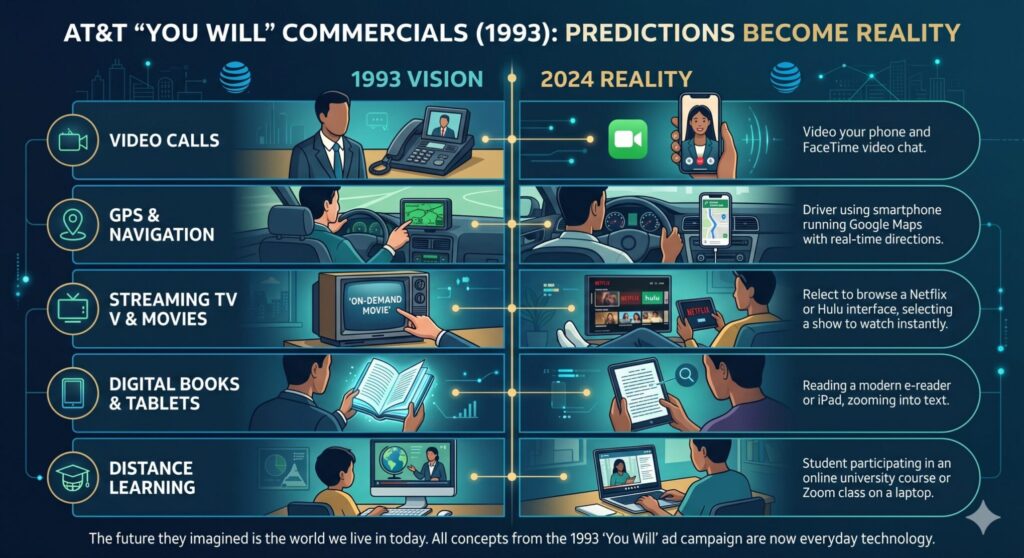
The “You Will” Prophecies: How AT&T’s 1993 Ads Saw the Future In 1993, the internet was a novelty mostly relegated to academic and military institutions. Dial-up connections hummed with erratic screeches, and cell phones, if you had one, resembled actual bricks. Yet, in the midst of this early technological landscape, AT&T launched an advertising campaign
The “You Will” Prophecies: How AT&T’s 1993 Ads Saw the Future In 1993, the internet was a novelty mostly relegated to academic and military institutions. Dial-up connections hummed with erratic screeches, and cell phones, if you had one, resembled actual bricks. Yet, in the midst of this early technological landscape, AT&T launched an advertising campaign
Read full post on fuellednetworks.com
Fake Tech Support Scams: A Survival Guide for Ottawa Businesses
Ever been startled by a sudden pop-up, screaming about a catastrophic virus and urging you to call a "tech support" number immediately? It feels like a digital mugging, doesn't it? You're not alone. This is the realm of fake tech support scams, a shadowy corner of the internet where deception reigns supreme.
Ever been startled by a sudden pop-up, screaming about a catastrophic virus and urging you to call a "tech support" number immediately? It feels like a digital mugging, doesn't it? You're not alone. This is the realm of fake tech support scams, a shadowy corner of the internet where deception reigns supreme.
Read full post on capitaltek.com