
What is Co-Managed IT?
Co-Managed IT is a collaborative approach where an organization’s internal IT team partners with an external Managed Service Provider (MSP) to share the responsibility of managing their IT infrastructure and services. This approach allows businesses to leverage the expertise and resources of both parties, combining the internal knowledge and control of the organization with the ... Read more
Co-Managed IT is a collaborative approach where an organization’s internal IT team partners with an external Managed Service Provider (MSP) to share the responsibility of managing their IT infrastructure and services. This approach allows businesses to leverage the expertise and resources of both parties, combining the internal knowledge and control of the organization with the ... Read more
Read full post on uprite.com
What 36-Month ROI Looks Like with Managed Secure Edge
Managed Secure Edge ROI is the measurable financial return an organization achieves by replacing a fragmented legacy network and security stack with a single managed SASE or SSE platform over a defined period. For a typical mid-market company running 10 to 15 locations, the 36-month ROI ranges from 65% to 162%, with a payback period ... Read more
Managed Secure Edge ROI is the measurable financial return an organization achieves by replacing a fragmented legacy network and security stack with a single managed SASE or SSE platform over a defined period. For a typical mid-market company running 10 to 15 locations, the 36-month ROI ranges from 65% to 162%, with a payback period ... Read more
Read full post on meriplex.com
Why Security Awareness Training Matters for Your Employees and Your Business
The majority of security breaches are due to human error. In order to minimize this risk, your business needs to address potential cybersecurity mistakes through an awareness training program. This program will identify areas of weakness and how to respond to them, as well as policies and legal requirements. Employee security awareness training is the protector of both your brand and the Personal Identifiable Information (PII) of your customers. Your IT services in Austin will perform significantly better if your team is on the same page about how to handle sensitive data.
The majority of security breaches are due to human error. In order to minimize this risk, your business needs to address potential cybersecurity mistakes through an awareness training program. This program will identify areas of weakness and how to respond to them, as well as policies and legal requirements. Employee security awareness training is the protector of both your brand and the Personal Identifiable Information (PII) of your customers. Your IT services in Austin will perform significantly better if your team is on the same page about how to handle sensitive data.
Read full post on blog.centretechnologies.com
Proven On-site Tech Support Services in Houston – 4 Reasons COBAIT Is the Smart Choice
Let’s be honest, when your business technology goes down, everything stops. And every minute of downtime is money out of your pocket. That’s exactly why finding the right on-site tech support services in Houston matters more than most business owners realize. COBAIT is a trusted name in business IT to support Texas, and they’ve built a reputation around showing fast and fixing things. It doesn’t matter if you’re running a small law firm near Galleria or managing a growing healthcare practice
Let’s be honest, when your business technology goes down, everything stops. And every minute of downtime is money out of your pocket. That’s exactly why finding the right on-site tech support services in Houston matters more than most business owners realize. COBAIT is a trusted name in business IT to support Texas, and they’ve built a reputation around showing fast and fixing things. It doesn’t matter if you’re running a small law firm near Galleria or managing a growing healthcare practice
Read full post on cobait.com
Azure Local 2604: SAN Support Changes the Conversation for Enterprise Hybrid Infrastructure
Azure Local version 2604, released in April 2026, introduces generally available SAN support and disaggregated deployment architecture, allowing organizations to separate compute growth from storage growth for the first time on the platform. Fibre Channel SAN storage can now be attached to Azure Local clusters while preserving Azure Arc integration, Azure-native management, and the full
Azure Local version 2604, released in April 2026, introduces generally available SAN support and disaggregated deployment architecture, allowing organizations to separate compute growth from storage growth for the first time on the platform. Fibre Channel SAN storage can now be attached to Azure Local clusters while preserving Azure Arc integration, Azure-native management, and the full
Read full post on virtuas.com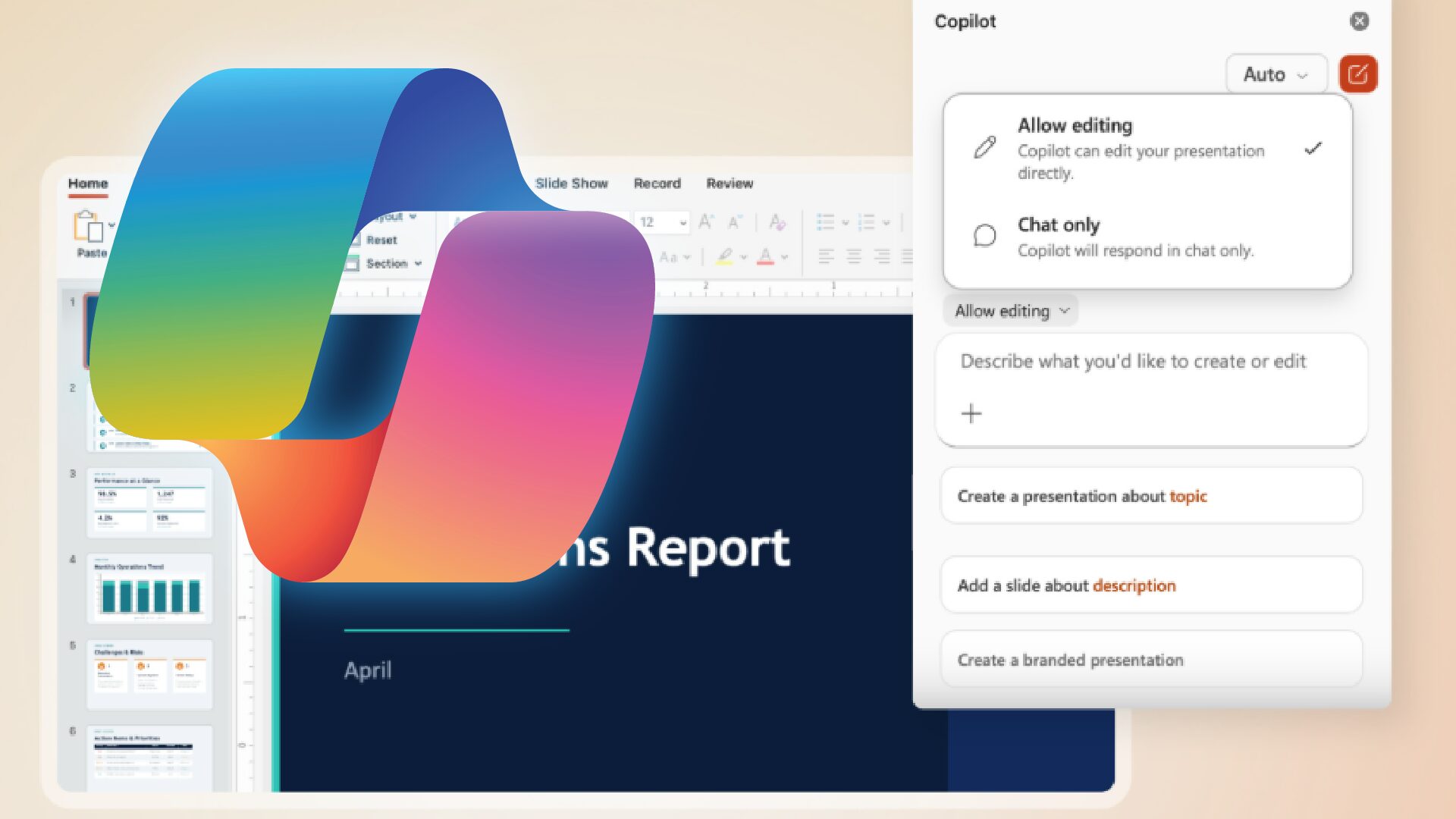
Microsoft Copilot Just Changed How You Work in Word, Excel, and PowerPoint
If you have Microsoft 365 Copilot and you opened Word, Excel, or PowerPoint recently, you may have noticed something different. The Copilot experience you were used to, the one that answered questions and offered suggestions you could choose to accept or ignore, has been replaced with something more capable. As of April 22, 2026, Microsoft
If you have Microsoft 365 Copilot and you opened Word, Excel, or PowerPoint recently, you may have noticed something different. The Copilot experience you were used to, the one that answered questions and offered suggestions you could choose to accept or ignore, has been replaced with something more capable. As of April 22, 2026, Microsoft
Read full post on aldridge.com