LI Tech Advisors
Our Mission is to provide our clients with the IT services and expertise to efficiently operate their school or business.

How to Spot a Phishing Email
Cybercriminals have become more sophisticated than ever, and thanks to AI, phishing emails are now harder to detect than many people realize. A phishing email is a fraudulent message designed to trick you into clicking a malicious link, opening an infected attachment, or providing sensitive information such as passwords, financial details, or login credentials. These
Cybercriminals have become more sophisticated than ever, and thanks to AI, phishing emails are now harder to detect than many people realize. A phishing email is a fraudulent message designed to trick you into clicking a malicious link, opening an infected attachment, or providing sensitive information such as passwords, financial details, or login credentials. These
Read full post on litechadvisors.com
What Is Email Spoofing?
Email spoofing is when someone sends an email that appears to come from your domain even though it did not actually originate from your company. The message may look completely legitimate, displaying your business name, email address, logo, and signature, but it was sent by someone else entirely. While email spoofing is not a new
Email spoofing is when someone sends an email that appears to come from your domain even though it did not actually originate from your company. The message may look completely legitimate, displaying your business name, email address, logo, and signature, but it was sent by someone else entirely. While email spoofing is not a new
Read full post on litechadvisors.com
How to Securely Back Up Microsoft Authenticator and Recover Your Accounts Faster
How to Properly Back Up Microsoft Authenticator (and Save Yourself Hours of Hassle) We’ve seen this happen far too often. A user upgrades to a new phone, downloads Microsoft Authenticator, signs in, and suddenly every account is missing. No authentication codes, no access to critical apps, and an urgent call to IT support. What should
How to Properly Back Up Microsoft Authenticator (and Save Yourself Hours of Hassle) We’ve seen this happen far too often. A user upgrades to a new phone, downloads Microsoft Authenticator, signs in, and suddenly every account is missing. No authentication codes, no access to critical apps, and an urgent call to IT support. What should
Read full post on litechadvisors.com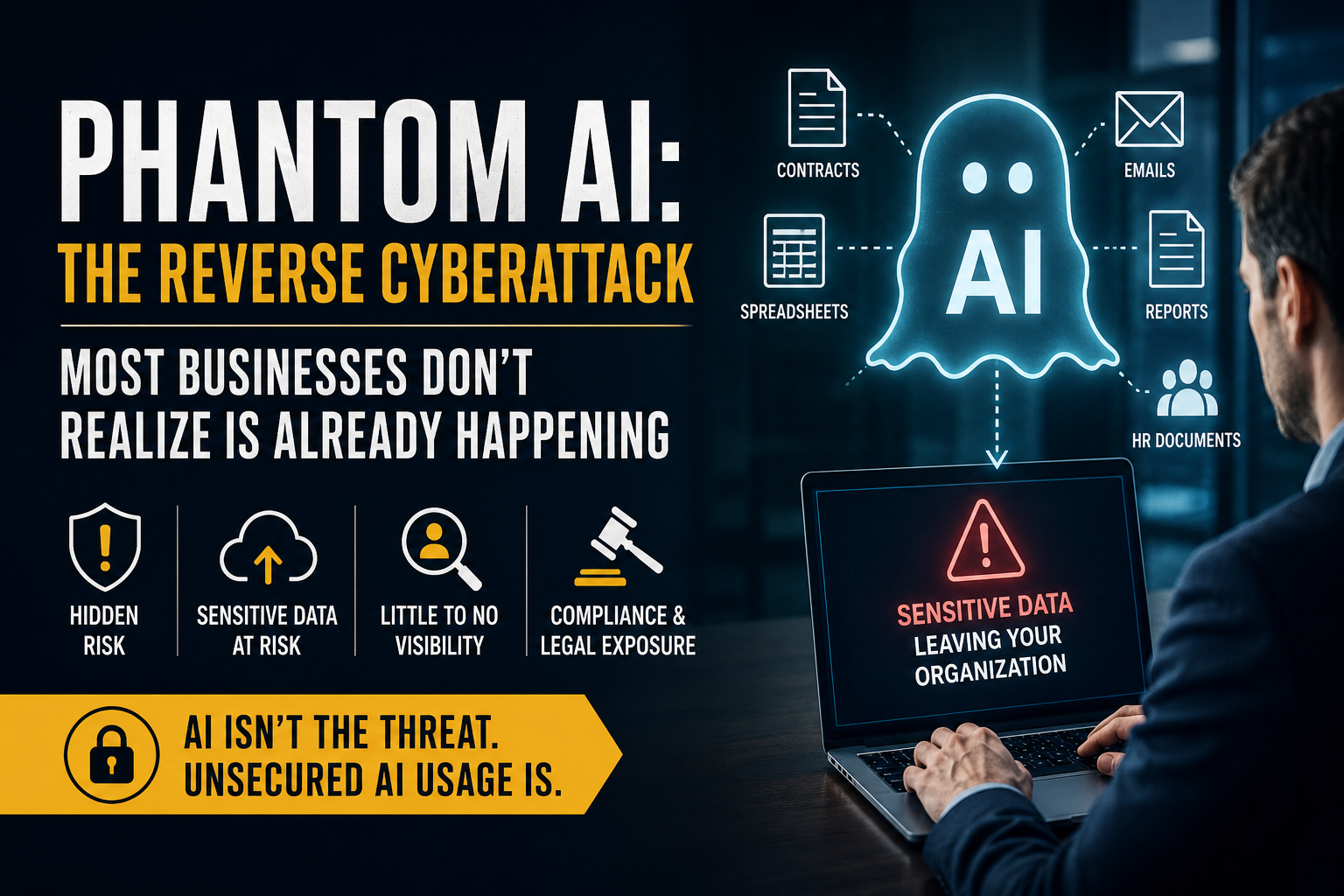
Phantom AI: The Reverse Cyberattack Most Businesses Don’t Realize Is Already Happening
For years, cybersecurity strategies have focused on one primary concern: keeping attackers out. Organizations have invested heavily in firewalls, endpoint protection, email security, cybersecurity awareness training, multi-factor authentication, and monitoring systems designed to stop external threats from gaining access to sensitive business information. But a new risk is rapidly emerging — and it is fundamentally
For years, cybersecurity strategies have focused on one primary concern: keeping attackers out. Organizations have invested heavily in firewalls, endpoint protection, email security, cybersecurity awareness training, multi-factor authentication, and monitoring systems designed to stop external threats from gaining access to sensitive business information. But a new risk is rapidly emerging — and it is fundamentally
Read full post on litechadvisors.com
How to Protect Your Business From Email Spoofing
Email spoofing is becoming more common in 2026 across all industries. The good news is that most businesses can stop it with a few simple fixes. If someone is sending fake emails that look like they came from your domain, it usually does not mean your email was hacked. Instead, it means your domain is
Email spoofing is becoming more common in 2026 across all industries. The good news is that most businesses can stop it with a few simple fixes. If someone is sending fake emails that look like they came from your domain, it usually does not mean your email was hacked. Instead, it means your domain is
Read full post on litechadvisors.com
Why Are My Emails Going to Spam? A Business Guide to Email Deliverability
A Long Island Business Guide to Email Deliverability If your business emails are suddenly landing in your clients’ spam folders, you are not alone. Across Long Island and beyond, businesses are realizing that important emails — proposals, invoices, customer replies, marketing campaigns, and even simple conversations are never making it to the inbox. At LI
A Long Island Business Guide to Email Deliverability If your business emails are suddenly landing in your clients’ spam folders, you are not alone. Across Long Island and beyond, businesses are realizing that important emails — proposals, invoices, customer replies, marketing campaigns, and even simple conversations are never making it to the inbox. At LI
Read full post on litechadvisors.com
Phantom AI: The Hidden AI Risk Already Inside Most Businesses
Most business owners believe the biggest AI risk is employees using artificial intelligence incorrectly. We see it differently. The larger threat may actually be something many organizations don’t even realize is already happening inside their environment: Phantom AI. What Is Phantom AI? “Phantom AI” refers to employees using AI tools throughout the workday without formal
Most business owners believe the biggest AI risk is employees using artificial intelligence incorrectly. We see it differently. The larger threat may actually be something many organizations don’t even realize is already happening inside their environment: Phantom AI. What Is Phantom AI? “Phantom AI” refers to employees using AI tools throughout the workday without formal
Read full post on litechadvisors.com
AI in 2026: From Automation to Full Business Integration
AI in 2026: From Automation to Full Business IntegrationHow businesses are moving beyond tools and embedding AI into daily operations, decision-making, and workflows. At LI Tech Advisors, we’re seeing a clear shift in how organizations approach artificial intelligence (AI). What started as simple automation and productivity tools has evolved into something much more impactful full
AI in 2026: From Automation to Full Business IntegrationHow businesses are moving beyond tools and embedding AI into daily operations, decision-making, and workflows. At LI Tech Advisors, we’re seeing a clear shift in how organizations approach artificial intelligence (AI). What started as simple automation and productivity tools has evolved into something much more impactful full
Read full post on litechadvisors.com
Is Outdated Technology Holding Your Business Back?
Is Outdated Technology Holding Your Business Back? Technology should be driving your business forward not slowing it down. Yet many organizations are still relying on outdated computers and aging equipment that quietly impact productivity, security, and overall performance. At first glance, keeping older devices may seem like a cost-saving decision. But over time, those savings
Is Outdated Technology Holding Your Business Back? Technology should be driving your business forward not slowing it down. Yet many organizations are still relying on outdated computers and aging equipment that quietly impact productivity, security, and overall performance. At first glance, keeping older devices may seem like a cost-saving decision. But over time, those savings
Read full post on litechadvisors.com