Find MSPs specializing in your industry.
Discover leading Managed IT Service Providers across USA, Canada & the United Kingdom.
- 100s of leading MSPs
- Find a MSP near you
- Latest IT news for SMBs

The Hidden Data Leak: Managing “Shadow AI” in Your Business
Learn about the security risks of "Shadow AI" and how to implement safe, enterprise-grade "walled gardens" to protect your proprietary data.
Learn about the security risks of "Shadow AI" and how to implement safe, enterprise-grade "walled gardens" to protect your proprietary data.
Read full post on mytekrescue.comMSPdb™ News

What’s New with Microsoft Copilot: 10 Key Features Your Team Should Know
Microsoft Copilot is becoming more useful inside the tools your team already uses every day. This blog breaks down 10 key features including Excel cleanup, agent-based analysis, Word drafting, PowerPoint creation, calendar scheduling, and inbox follow-up.
Microsoft Copilot is becoming more useful inside the tools your team already uses every day. This blog breaks down 10 key features including Excel cleanup, agent-based analysis, Word drafting, PowerPoint creation, calendar scheduling, and inbox follow-up.
Read full post on snaptechit.com
Adversary-in-the-Middle Attacks: How Phishing Sites Steal Your Active Login
You click a link, sign in, approve the MFA prompt, and get on with your day. Completely unaware that someone else just logged into your account at the same moment. That scenario surprises many businesses, particularly those that rely on multi-factor authentication (MFA) to protect cloud accounts. But this is exactly how Adversary-in-the-Middle (AiTM) phishing
You click a link, sign in, approve the MFA prompt, and get on with your day. Completely unaware that someone else just logged into your account at the same moment. That scenario surprises many businesses, particularly those that rely on multi-factor authentication (MFA) to protect cloud accounts. But this is exactly how Adversary-in-the-Middle (AiTM) phishing
Read full post on avenirit.com
Migrating to Azure: Common Mistakes Businesses Must Avoid
Cloud migration is no longer a future initiative. It has become a business survival strategy.…
Cloud migration is no longer a future initiative. It has become a business survival strategy.…
Read full post on blog.synergyit.ca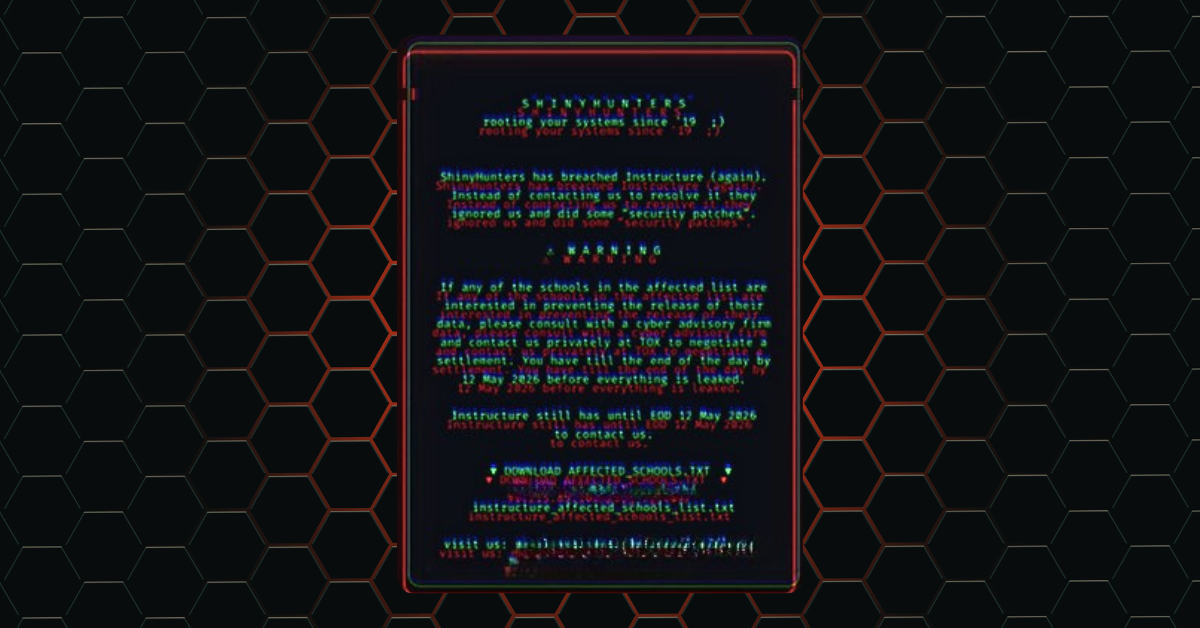
Education platform Canvas reached settlement with ransomware group “ShinyHunters” to prevent the release of data affecting 275 million users
At the worst possible time, millions of students and educators found themselves locked out of Canvas, the digital backbone of classrooms across the country. What started as a cybersecurity incident
At the worst possible time, millions of students and educators found themselves locked out of Canvas, the digital backbone of classrooms across the country. What started as a cybersecurity incident
Read full post on valleytechlogic.com
Cyber insurance is making small businesses grow up fast
For much of the 25 years we have spent supporting businesses on Vancouver Island, the phrase “cyber insurance” rarely came up in conversation. In our early days, cybersecurity meant having a decent antivirus and telling your team not to open suspicious attachments. If insurance existed at all, it was a niche product for tech companies,...
For much of the 25 years we have spent supporting businesses on Vancouver Island, the phrase “cyber insurance” rarely came up in conversation. In our early days, cybersecurity meant having a decent antivirus and telling your team not to open suspicious attachments. If insurance existed at all, it was a niche product for tech companies,...
Read full post on daxtech.ca
What Business Owners Should Know About Vendor Access
A vendor needs to log in to update your accounting software. A copier technician needs network access to troubleshoot a printing issue. A consultant needs temporary access to a shared folder. A software provider asks for administrator privileges so they can “take care of it faster.” For many small and mid-sized businesses, these requests feel
A vendor needs to log in to update your accounting software. A copier technician needs network access to troubleshoot a printing issue. A consultant needs temporary access to a shared folder. A software provider asks for administrator privileges so they can “take care of it faster.” For many small and mid-sized businesses, these requests feel
Read full post on fantasticit.com
What to Look for in a Phoenix Managed IT Provider
Whether you’re an ambitious startup in Tempe or an established firm in Scottsdale, business growth is exciting. But as your company expands, you may find that your digital needs are changing. Business leaders in Phoenix are constantly on the receiving end of a barrage of cybersecurity threats. That’s not even to mention the strict compliance
Whether you’re an ambitious startup in Tempe or an established firm in Scottsdale, business growth is exciting. But as your company expands, you may find that your digital needs are changing. Business leaders in Phoenix are constantly on the receiving end of a barrage of cybersecurity threats. That’s not even to mention the strict compliance
Read full post on onboardit.com
Xigent & VergeIO: Title Sponsors of ND IT Symposium 2026
Xigent & VergeIO connected with IT leaders at the North Dakota IT Symposium to tackle real infrastructure challenges and what’s next for virtualization A Great Day Connecting at the Symposium Xigent had an incredible day at the North Dakota IT Symposium, spending time with IT leaders from across the region who are tackling real infrastructure
Xigent & VergeIO connected with IT leaders at the North Dakota IT Symposium to tackle real infrastructure challenges and what’s next for virtualization A Great Day Connecting at the Symposium Xigent had an incredible day at the North Dakota IT Symposium, spending time with IT leaders from across the region who are tackling real infrastructure
Read full post on xigentsolutions.com
The Hidden Risks of “Cheap” IT: Why Validation Matters
When systems are running smoothly, IT support can feel like a place to reduce costs. If nothing is breaking, it’s easy to assume a lower-cost provider is doing the job just as well. While lower-cost services don’t automatically equate to poor quality, they often lack the invisible safeguards that protect a business when unexpected challenges
When systems are running smoothly, IT support can feel like a place to reduce costs. If nothing is breaking, it’s easy to assume a lower-cost provider is doing the job just as well. While lower-cost services don’t automatically equate to poor quality, they often lack the invisible safeguards that protect a business when unexpected challenges
Read full post on infinitelyvirtual.com
Premier Networx Launches Innovation Lab Scholars Program to Expand Access to STEM Education in the CSRA
At Premier Networx, we believe access to technology education can create life-changing opportunities. As technology continues to shape the future...
At Premier Networx, we believe access to technology education can create life-changing opportunities. As technology continues to shape the future...
Read full post on premworx.com