Cybersecurity
Latest cybersecurity news, ransomware alerts, and threat intelligence for growing companies.

This Week In Cybersecurity | May 29th, 2026
This Week in Cybersecurity Each week at Applied Tech we recap the biggest cybersecurity news headlines from the week to keep you informed and ready to face the latest threats. Here’s your breakdown for the week of May 23rd – 29th. Krispy Kreme Settlement After a November 2024 cyberattack compromised the personal information of over
This Week in Cybersecurity Each week at Applied Tech we recap the biggest cybersecurity news headlines from the week to keep you informed and ready to face the latest threats. Here’s your breakdown for the week of May 23rd – 29th. Krispy Kreme Settlement After a November 2024 cyberattack compromised the personal information of over
Read full post on appliedtech.us
AI is making fraud easier and more lucrative, with AI enabled phishing emails seeing 25% higher open rates than human crafted variations
Artificial intelligence has changed the economics of fraud. Scammers no longer need to be skilled writers, native speakers, designers, or even patient researchers to create believable attacks. With AI tools,
Artificial intelligence has changed the economics of fraud. Scammers no longer need to be skilled writers, native speakers, designers, or even patient researchers to create believable attacks. With AI tools,
Read full post on valleytechlogic.com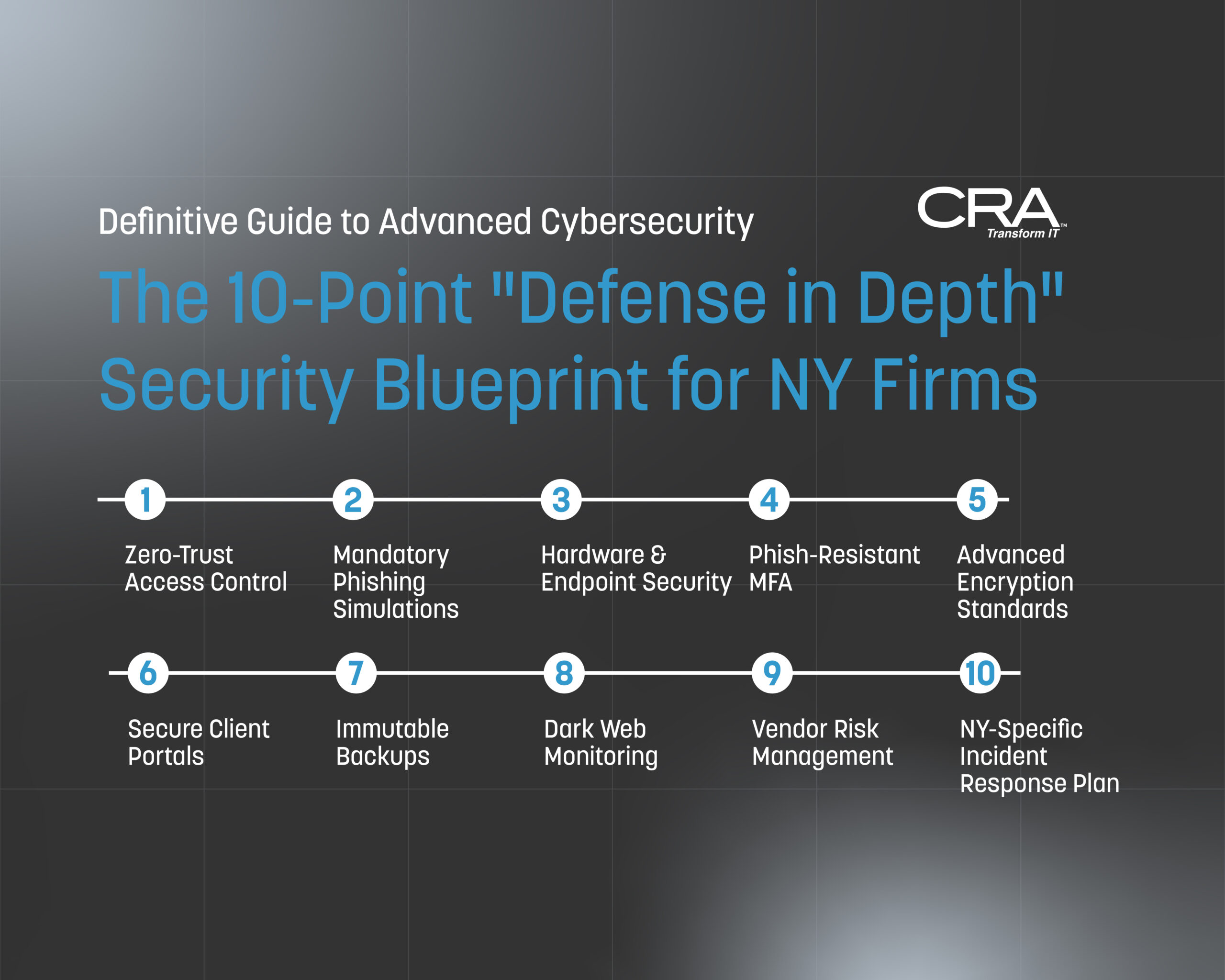
Advanced Cybersecurity for New York Law Firms: The Definitive Guide for Compliance & Protection in 2026
Introduction: The Cost of Complacency in the New York Legal Landscape New York law firms occupy a unique and paradoxical position in the cybersecurity landscape. On one hand, your firm handles some of the most sensitive, high-value information in the world — privileged communications, M&A deal structures, real estate escrow instructions, litigation strategies, and the…
Introduction: The Cost of Complacency in the New York Legal Landscape New York law firms occupy a unique and paradoxical position in the cybersecurity landscape. On one hand, your firm handles some of the most sensitive, high-value information in the world — privileged communications, M&A deal structures, real estate escrow instructions, litigation strategies, and the…
Read full post on consultcra.com
What is MDR? Managed detection and response explained
What is MDR? Managed detection and response is the layer of cybersecurity that sits on top of detection tools and turns alerts into action. EDR software flags suspicious activity. MDR puts trained human analysts behind that software to investigate every alert, confirm whether it represents a real threat, and contain it before damage occurs. For
What is MDR? Managed detection and response is the layer of cybersecurity that sits on top of detection tools and turns alerts into action. EDR software flags suspicious activity. MDR puts trained human analysts behind that software to investigate every alert, confirm whether it represents a real threat, and contain it before damage occurs. For
Read full post on sados.com
NYDFS Warns of Rising Cybersecurity Risks from Frontier AI Models: What Regulated Businesses Should Do Now
As artificial intelligence rapidly transforms the cybersecurity landscape, the New York State Department of Financial Services (NYDFS) has issued a critical advisory warning regulated organizations about the rising threats posed by "Frontier AI Models." These advanced AI systems can dramatically accelerate cyberattacks, making traditional security measures insufficient. With compliance-driven industries like healthcare and finance particularly vulnerable, it's essential for businesses to act now. Discover key recommendations from NYDFS to strengthen your cybersecurity posture and safeguard sen
As artificial intelligence rapidly transforms the cybersecurity landscape, the New York State Department of Financial Services (NYDFS) has issued a critical advisory warning regulated organizations about the rising threats posed by "Frontier AI Models." These advanced AI systems can dramatically accelerate cyberattacks, making traditional security measures insufficient. With compliance-driven industries like healthcare and finance particularly vulnerable, it's essential for businesses to act now. Discover key recommendations from NYDFS to strengthen your cybersecurity posture and safeguard sensitive data against evolving AI-powered threats. Don't wait for the next attack—learn how to proactively enhance your defenses today!
Read full post on systechmsp.com
Your AI Assistant Can Recommend Malware.
It Already Has. Someone on your team needs a tool. A utility to read a stubborn PDF. Something to check why a laptop runs hot and loud. They do not open a search engine and scroll past the ads anymore. They ask the AI assistant. It answers in a second, clean and confident, with a ... Read more
It Already Has. Someone on your team needs a tool. A utility to read a stubborn PDF. Something to check why a laptop runs hot and loud. They do not open a search engine and scroll past the ads anymore. They ask the AI assistant. It answers in a second, clean and confident, with a ... Read more
Read full post on bluelightit.com
What Is an Insider Threat? The Cybersecurity Risk Already Inside Your Business
Most business owners worry about cybercriminals breaking in from the outside, and they should. Phishing emails, ransomware, and fraudulent wire transfers are all real threats. But some of the most damaging security incidents begin much Read More...
Most business owners worry about cybercriminals breaking in from the outside, and they should. Phishing emails, ransomware, and fraudulent wire transfers are all real threats. But some of the most damaging security incidents begin much Read More...
Read full post on taznetworks.com
FBI Warning: A New Phishing Scam Is Breaking Into Microsoft 365 Accounts Without Stealing Passwords
If you use Microsoft 365 for work — email, Teams, OneDrive, SharePoint — there’s a new phishing scam you need to know about. The FBI issued a public warning about it on May 21, 2026, and it’s worth your attention for one big reason: it gets into your account without ever stealing your password, and
If you use Microsoft 365 for work — email, Teams, OneDrive, SharePoint — there’s a new phishing scam you need to know about. The FBI issued a public warning about it on May 21, 2026, and it’s worth your attention for one big reason: it gets into your account without ever stealing your password, and
Read full post on wendego.com
Cybersecurity Shifts Since 2023 (2026 Guide)
What’s Changed in Cybersecurity Since 2023? Here’s What Matters in 2026 If you read a cybersecurity trends article from 2023, half of it still applies. The other half is out of date. This post answers the question most business owners are asking: what is genuinely different now, and what do I need to do about
What’s Changed in Cybersecurity Since 2023? Here’s What Matters in 2026 If you read a cybersecurity trends article from 2023, half of it still applies. The other half is out of date. This post answers the question most business owners are asking: what is genuinely different now, and what do I need to do about
Read full post on novatech.net
What Business Owners Should Know About MFA Fatigue Attacks
A business owner sees a security alert and feels a little relief. The company has MFA turned on, so even if someone steals a password, they still need that second approval before they can get in. That is true, and it is one reason MFA remains one of the most important protections a business can
A business owner sees a security alert and feels a little relief. The company has MFA turned on, so even if someone steals a password, they still need that second approval before they can get in. That is true, and it is one reason MFA remains one of the most important protections a business can
Read full post on fantasticit.com
Microsoft Sentinel: AI-Powered SIEM for Proactive Security
The Cybersecurity Reality Businesses Can No Longer Ignore Cyberattacks are no longer targeting only large…
The Cybersecurity Reality Businesses Can No Longer Ignore Cyberattacks are no longer targeting only large…
Read full post on blog.synergyit.ca
Empowering Leaders: Cybersecurity for Executives Explained
Cybersecurity for executives is now a major business priority, as phishing, ransomware, deepfakes, and email scams can expose sensitive data, disrupt operations, and lead to costly breaches. Strong leadership, layered security solutions, regular staff training, and routine cybersecurity audits all help reduce risks and keep organizations prepared for evolving cyber threats. The stakes have never been
Cybersecurity for executives is now a major business priority, as phishing, ransomware, deepfakes, and email scams can expose sensitive data, disrupt operations, and lead to costly breaches. Strong leadership, layered security solutions, regular staff training, and routine cybersecurity audits all help reduce risks and keep organizations prepared for evolving cyber threats. The stakes have never been
Read full post on pegasustechnologies.com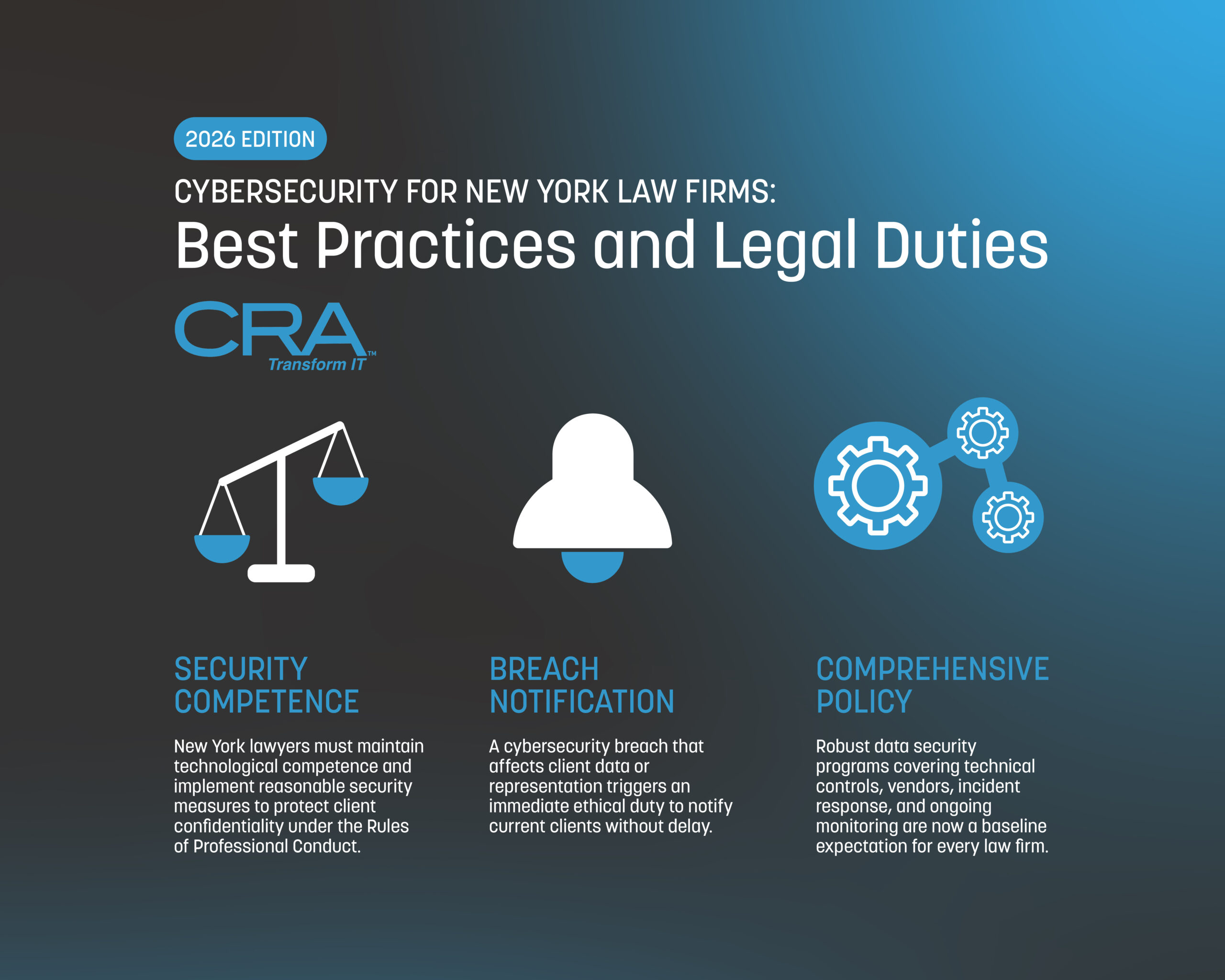
Cybersecurity for New York Law Firms: Best Practices – 2026 Edition
Cybersecurity Best Practices and Legal Duties for Law Offices in NYC - 2026 Edition Law firms in New York are sitting on a goldmine of confidential client info, which, let’s be honest, makes them a tempting target for cybercriminals after financial records, trade secrets, and all sorts of sensitive legal docs. The sheer volume…
Cybersecurity Best Practices and Legal Duties for Law Offices in NYC - 2026 Edition Law firms in New York are sitting on a goldmine of confidential client info, which, let’s be honest, makes them a tempting target for cybercriminals after financial records, trade secrets, and all sorts of sensitive legal docs. The sheer volume…
Read full post on consultcra.com
8 Cyber Security Threats All SMBs Face
You read the news and hear about cyber attacks on big businesses and think, “that would never happen to me.” It’s an easy trap to fall into. Many Small & Medium Business (SMB) owners operate under the guise that cyber criminals go after the big fish – the ones with lots of money, sensitive data, ... Read more
You read the news and hear about cyber attacks on big businesses and think, “that would never happen to me.” It’s an easy trap to fall into. Many Small & Medium Business (SMB) owners operate under the guise that cyber criminals go after the big fish – the ones with lots of money, sensitive data, ... Read more
Read full post on uprite.com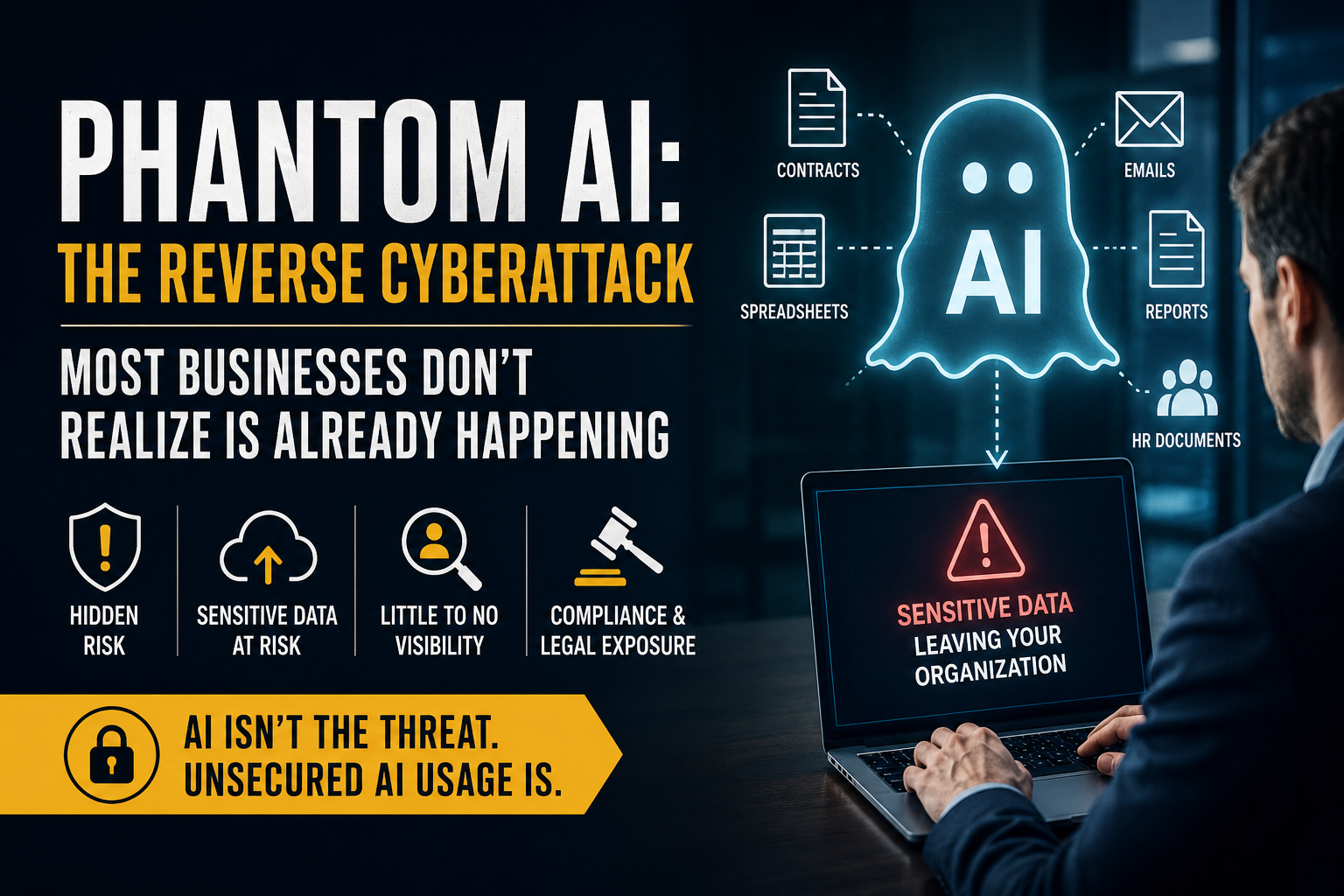
Phantom AI: The Reverse Cyberattack Most Businesses Don’t Realize Is Already Happening
For years, cybersecurity strategies have focused on one primary concern: keeping attackers out. Organizations have invested heavily in firewalls, endpoint protection, email security, cybersecurity awareness training, multi-factor authentication, and monitoring systems designed to stop external threats from gaining access to sensitive business information. But a new risk is rapidly emerging — and it is fundamentally
For years, cybersecurity strategies have focused on one primary concern: keeping attackers out. Organizations have invested heavily in firewalls, endpoint protection, email security, cybersecurity awareness training, multi-factor authentication, and monitoring systems designed to stop external threats from gaining access to sensitive business information. But a new risk is rapidly emerging — and it is fundamentally
Read full post on litechadvisors.com
Cybersecurity Isn’t One Decision… It’s 50 Small Ones
Most business owners think about cybersecurity the wrong way. They picture it as a single moment — the day they buy the software, hire the IT guy, or sign off on the policy. Box checked. Done. Back to running the business.
Most business owners think about cybersecurity the wrong way. They picture it as a single moment — the day they buy the software, hire the IT guy, or sign off on the policy. Box checked. Done. Back to running the business.
Read full post on lddconsulting.com
Why Your Business Needs a Cyber Incident Response Plan: What to Do After an Attack
A cyber incident response plan is your organization's playbook for detecting, responding to, and recovering from security breaches, ransomware attacks, data theft, and other cyber threats. Think of it as your fire escape plan, but for digital disasters.
A cyber incident response plan is your organization's playbook for detecting, responding to, and recovering from security breaches, ransomware attacks, data theft, and other cyber threats. Think of it as your fire escape plan, but for digital disasters.
Read full post on gocourant.com
Why SMBs Should Partner with SOC 2 Certified MSPs
In today’s rapidly evolving digital landscape, small and medium-sized businesses (SMBs) face unprecedented challenges when it comes to data security, compliance, and operational resilience. Cyber threats are becoming more sophisticated, while customers and business partners increasingly expect organizations to maintain strong security and privacy standards. For SMBs, partnering with a SOC 2 certified Managed Service
In today’s rapidly evolving digital landscape, small and medium-sized businesses (SMBs) face unprecedented challenges when it comes to data security, compliance, and operational resilience. Cyber threats are becoming more sophisticated, while customers and business partners increasingly expect organizations to maintain strong security and privacy standards. For SMBs, partnering with a SOC 2 certified Managed Service
Read full post on trndigital.com
Law Firm Cybersecurity: Essential Practices for Protection
Cybersecurity for law firms protects confidential client data and reduces exposure to data breaches. Strong legal cybersecurity strategies help firms maintain compliance with legal and regulatory requirements while protecting client information. According to Securities Docket, a comprehensive study by the Swiss tech company Proton found that one in five law firms in the U.S. were targeted by a
Cybersecurity for law firms protects confidential client data and reduces exposure to data breaches. Strong legal cybersecurity strategies help firms maintain compliance with legal and regulatory requirements while protecting client information. According to Securities Docket, a comprehensive study by the Swiss tech company Proton found that one in five law firms in the U.S. were targeted by a
Read full post on pegasustechnologies.com
Cybersecurity by Inches
Written by Jonathan Perz, Manager of Information Security at Abacus Technologies Quick summary Cybersecurity is not a...
Written by Jonathan Perz, Manager of Information Security at Abacus Technologies Quick summary Cybersecurity is not a...
Read full post on abacustechnologies.comFailed to load more articles
You're all caught up!
Check back later for more cybersecurity news.
MSPdb™ News

How to Spot a Phishing Email
Cybercriminals have become more sophisticated than ever, and thanks to AI, phishing emails are now harder to detect than many people realize. A phishing email is a fraudulent message designed to trick you into clicking a malicious link, opening an infected attachment, or providing sensitive information such as passwords, financial details, or login credentials. These
Cybercriminals have become more sophisticated than ever, and thanks to AI, phishing emails are now harder to detect than many people realize. A phishing email is a fraudulent message designed to trick you into clicking a malicious link, opening an infected attachment, or providing sensitive information such as passwords, financial details, or login credentials. These
Read full post on litechadvisors.com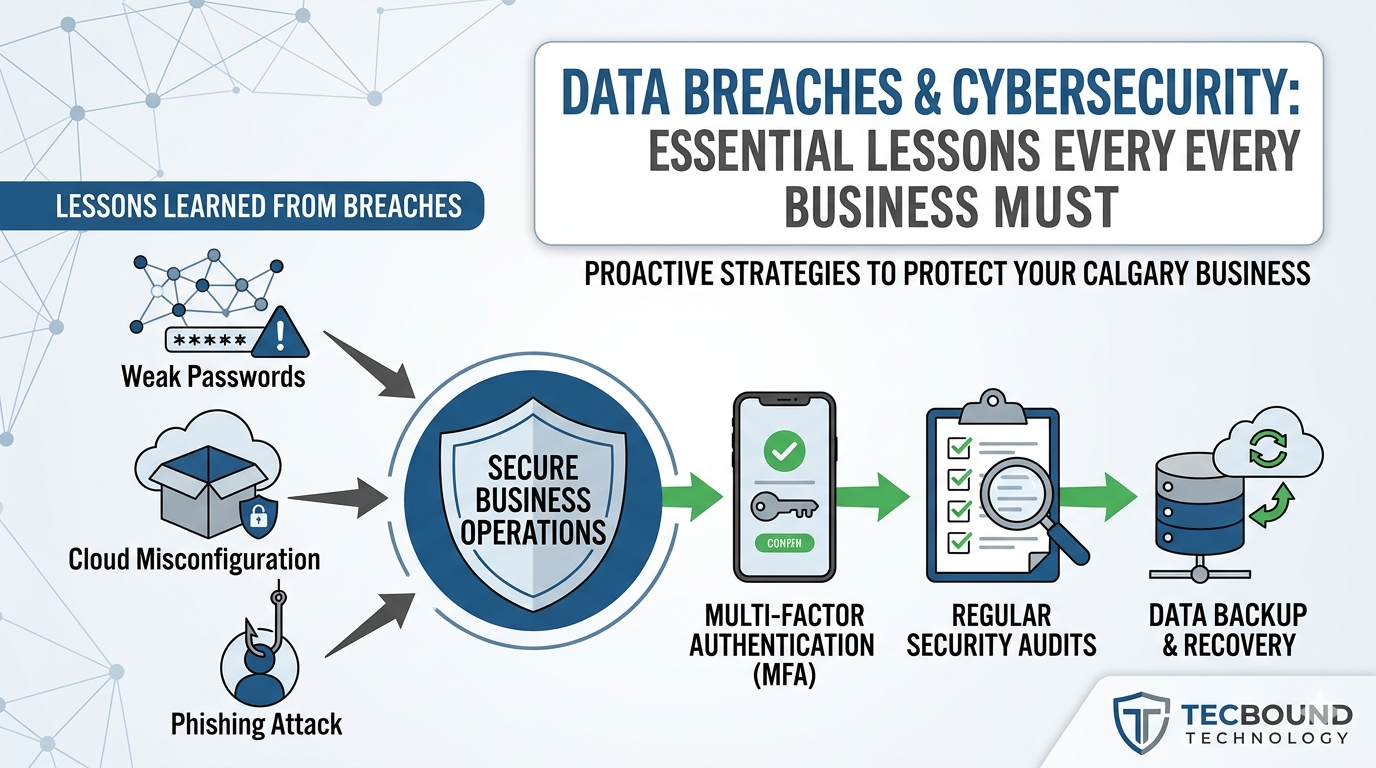
Data Breach Cybersecurity Lessons for Businesses | Tecbound
Business cybersecurity team reviewing data breach risks and prevention strategies
Business cybersecurity team reviewing data breach risks and prevention strategies
Read full post on tecbound.com
Cybersecurity for Venture Capital Firms: Protecting Deal Flow, Capital Movement, and Portfolio Communications
Venture capital firms rarely start the cybersecurity conversation with compliance. They start it when a partner cannot get support on the road, a capital call depends on a clean wire process, a provider misses a project deadline, or sensitive information is being passed to portfolio companies through ad hoc channels. For GPs, Managing Directors, CFOs,
Venture capital firms rarely start the cybersecurity conversation with compliance. They start it when a partner cannot get support on the road, a capital call depends on a clean wire process, a provider misses a project deadline, or sensitive information is being passed to portfolio companies through ad hoc channels. For GPs, Managing Directors, CFOs,
Read full post on coretelligent.com
Benefits of Cybersecurity Awareness Training for Employees
Cybersecurity awareness training helps employees recognize threats before they become costly problems.
Cybersecurity awareness training helps employees recognize threats before they become costly problems.
Read full post on wactel.com
Downtime Is a Cybersecurity Problem, Not Just an IT Problem
Downtime can affect payroll, customer service, compliance, productivity, revenue, and reputation. For small businesses and government contractors, outages are no longer just technical issues. This blog explains why downtime should be treated as a cybersecurity and business resilience problem, and how organizations can better prepare for disruptions.
Downtime can affect payroll, customer service, compliance, productivity, revenue, and reputation. For small businesses and government contractors, outages are no longer just technical issues. This blog explains why downtime should be treated as a cybersecurity and business resilience problem, and how organizations can better prepare for disruptions.
Read full post on v2systems.com
The “Session Cookie” Hijack: Why MFA Can’t Always Save You
MFA is a strong front-door lock. But it’s not the only thing that decides whether someone can get in.After you sign in, your browser keeps you logged in using a session token (often stored as a cookie). It’s the digital version of a wristband at an event: once you’ve been checked, the wristband proves you
MFA is a strong front-door lock. But it’s not the only thing that decides whether someone can get in.After you sign in, your browser keeps you logged in using a session token (often stored as a cookie). It’s the digital version of a wristband at an event: once you’ve been checked, the wristband proves you
Read full post on techriver.com
The Importance of Cyber Security Training for Your Team
Cybersecurity is no longer just the responsibility of IT departments. Every employee has to play a role in protecting business systems, data, and operations. Even with advanced firewalls, antivirus tools, and monitoring systems in place, one careless click from an employee can expose an entire organization to serious cyber threats. That’s why cybersecurity training has
Cybersecurity is no longer just the responsibility of IT departments. Every employee has to play a role in protecting business systems, data, and operations. Even with advanced firewalls, antivirus tools, and monitoring systems in place, one careless click from an employee can expose an entire organization to serious cyber threats. That’s why cybersecurity training has
Read full post on sunitsolutions.ca
What Counts as Real 24x7 SOC Coverage?
Many organizations believe they have 24x7 security monitoring because alerts are generated around the clock. Logs are being collected. A provider may be watching a queue. An internal team may receive after-hours notifications. But 24x7 monitoring is not always the same as 24x7 SOC coverage. The distinction matters because security operations are not defined by whether a tool can produce an alert at 2:00 a.m. They are defined by what happens after that alert appears. Who reviews it? What context do they have? Can they connect the signal to related activity across the environment? Do they kno
Many organizations believe they have 24x7 security monitoring because alerts are generated around the clock. Logs are being collected. A provider may be watching a queue. An internal team may receive after-hours notifications. But 24x7 monitoring is not always the same as 24x7 SOC coverage. The distinction matters because security operations are not defined by whether a tool can produce an alert at 2:00 a.m. They are defined by what happens after that alert appears. Who reviews it? What context do they have? Can they connect the signal to related activity across the environment? Do they know when to escalate? Is someone accountable for driving the next step? Is remediation tracked through closure? That is the gap between detection and response. Detection tells you something may be wrong. Response determines whether the organization can act on it in time. For IT and security leaders, the better question is not, “Do we have 24x7 monitoring?” It is, “Can a security event move from signal to decision to action at any hour?”
Read full post on blog.vectorusa.com
Your Ultimate Guide to Cybersecurity Insurance
Cyberattacks are no longer rare, high-profile events reserved for large enterprises. Today, attackers increasingly target small and mid-sized businesses because...
Cyberattacks are no longer rare, high-profile events reserved for large enterprises. Today, attackers increasingly target small and mid-sized businesses because...
Read full post on athensmicro.com
SOC 2 for Startups and SMBs: What it Costs and What to Expect
If you run a tech startup or small business that handles customer data, you’ve probably heard of SOC 2 – the gold-standard audit report that demonstrates your company follows strong security controls. Prospective clients (especially enterprise ones) might even be asking for “SOC 2 compliance” before signing a deal. But for startups and SMBs, pursuing
If you run a tech startup or small business that handles customer data, you’ve probably heard of SOC 2 – the gold-standard audit report that demonstrates your company follows strong security controls. Prospective clients (especially enterprise ones) might even be asking for “SOC 2 compliance” before signing a deal. But for startups and SMBs, pursuing
Read full post on cinchit.comPopular MSPs
View AllStay Updated
Get the latest cybersecurity advice for growing companies delivered to your inbox.