Managed Service Providers in New York, USA
Page 4 of 4

FREE DOWNLOAD: The MSP Guide to Achieving Real Operational Value from AI
Use this guide to spark industry-specific cybersecurity conversations that show you understand your clients' risks and realities.
Use this guide to spark industry-specific cybersecurity conversations that show you understand your clients' risks and realities.
Read full post on channelpronetwork.com
How to Spot a Phishing Email
Cybercriminals have become more sophisticated than ever, and thanks to AI, phishing emails are now harder to detect than many people realize. A phishing email is a fraudulent message designed to trick you into clicking a malicious link, opening an infected attachment, or providing sensitive information such as passwords, financial details, or login credentials. These
Cybercriminals have become more sophisticated than ever, and thanks to AI, phishing emails are now harder to detect than many people realize. A phishing email is a fraudulent message designed to trick you into clicking a malicious link, opening an infected attachment, or providing sensitive information such as passwords, financial details, or login credentials. These
Read full post on litechadvisors.com
Building a Cybersecurity Culture in Microsoft 365 SMBs | Sourcepass
For many small and mid-sized businesses, cybersecurity investment starts with tools. Firewalls, endpoint protection, backups, and Microsoft 365 security controls all matter. But tools alone do not create resilience. Most real-world incidents still involve human behavior such as approving a fake MFA prompt, clicking a phishing link, sharing files too broadly, or trusting a spoofed payment request.
For many small and mid-sized businesses, cybersecurity investment starts with tools. Firewalls, endpoint protection, backups, and Microsoft 365 security controls all matter. But tools alone do not create resilience. Most real-world incidents still involve human behavior such as approving a fake MFA prompt, clicking a phishing link, sharing files too broadly, or trusting a spoofed payment request.
Read full post on blog.sourcepass.com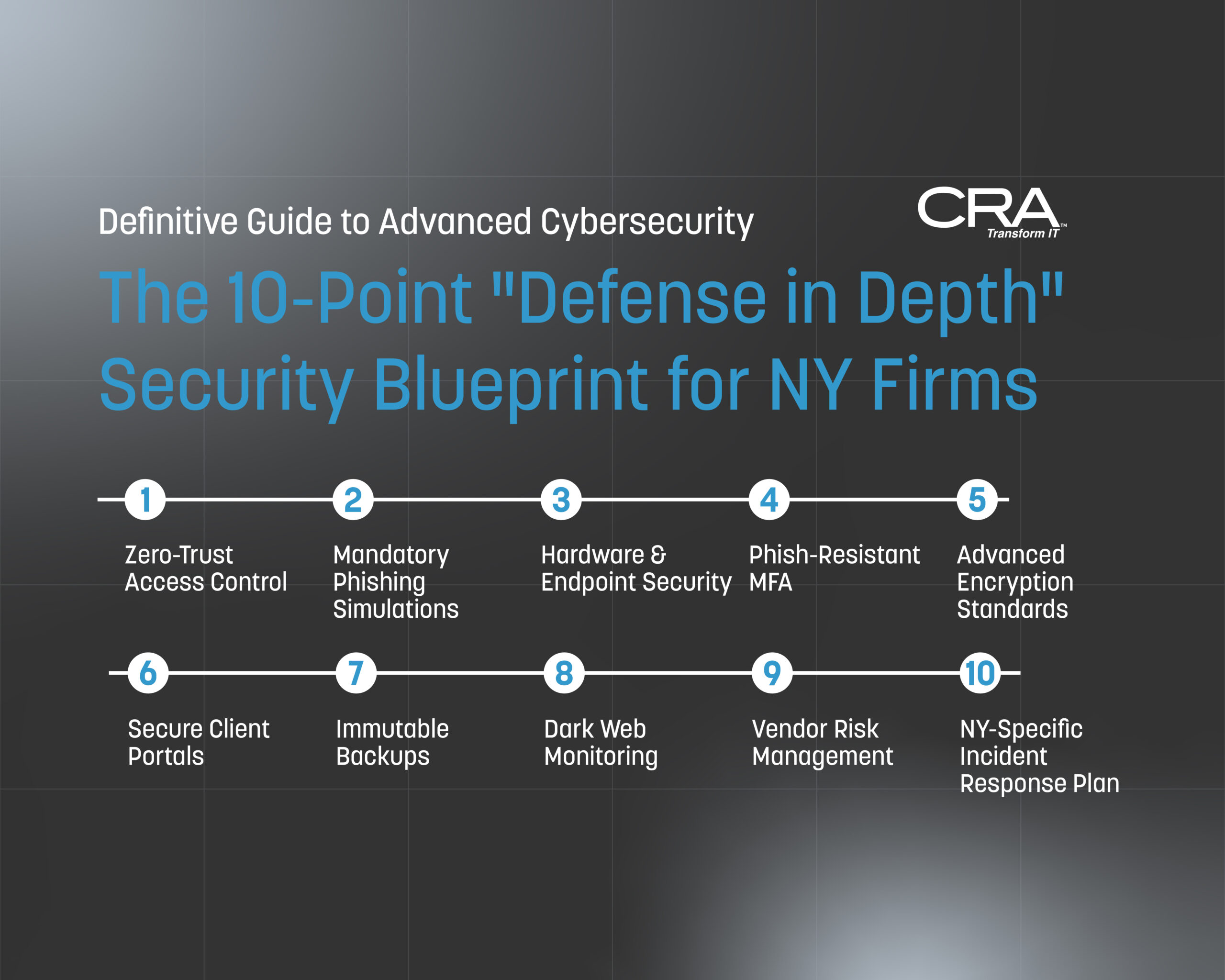
Advanced Cybersecurity for New York Law Firms: The Definitive Guide for Compliance & Protection in 2026
Introduction: The Cost of Complacency in the New York Legal Landscape New York law firms occupy a unique and paradoxical position in the cybersecurity landscape. On one hand, your firm handles some of the most sensitive, high-value information in the world — privileged communications, M&A deal structures, real estate escrow instructions, litigation strategies, and the…
Introduction: The Cost of Complacency in the New York Legal Landscape New York law firms occupy a unique and paradoxical position in the cybersecurity landscape. On one hand, your firm handles some of the most sensitive, high-value information in the world — privileged communications, M&A deal structures, real estate escrow instructions, litigation strategies, and the…
Read full post on consultcra.com
How Dashlane’s Admin-Assisted Recovery Works for Members of Professional Plans
Learn about Dashlane’s admin-assisted recovery process for professional plan subscribers not using single sign-on (SSO).
Learn about Dashlane’s admin-assisted recovery process for professional plan subscribers not using single sign-on (SSO).
Read full post on dashlane.com
NYDFS Warns of Rising Cybersecurity Risks from Frontier AI Models: What Regulated Businesses Should Do Now
As artificial intelligence rapidly transforms the cybersecurity landscape, the New York State Department of Financial Services (NYDFS) has issued a critical advisory warning regulated organizations about the rising threats posed by "Frontier AI Models." These advanced AI systems can dramatically accelerate cyberattacks, making traditional security measures insufficient. With compliance-driven industries like healthcare and finance particularly vulnerable, it's essential for businesses to act now. Discover key recommendations from NYDFS to strengthen your cybersecurity posture and safeguard sen
As artificial intelligence rapidly transforms the cybersecurity landscape, the New York State Department of Financial Services (NYDFS) has issued a critical advisory warning regulated organizations about the rising threats posed by "Frontier AI Models." These advanced AI systems can dramatically accelerate cyberattacks, making traditional security measures insufficient. With compliance-driven industries like healthcare and finance particularly vulnerable, it's essential for businesses to act now. Discover key recommendations from NYDFS to strengthen your cybersecurity posture and safeguard sensitive data against evolving AI-powered threats. Don't wait for the next attack—learn how to proactively enhance your defenses today!
Read full post on systechmsp.com
How Small Organizations Are Using Embedded AI to Reduce Administrative Burden
Embedded AI is helping small organizations reclaim time, reduce stress, and operate with more confidence.
Embedded AI is helping small organizations reclaim time, reduce stress, and operate with more confidence.
Read full post on wcatech.com