Let's solve your IT challenges.
Discover leading Managed IT Service Providers across USA, Canada & the United Kingdom.
- 100s of leading MSPs
- Find a MSP near you
- Latest IT news for SMBs

Local Admin Access: Convenience or Catastrophe?
Imagine this: your team is working against a tight deadline. A critical application needs an update, but the user doesn’t have permission to install it. Frustration builds. The quickest fix? Give them local admin rights. Problem solved, right? Not quite. That single decision could open the door to a cyberattack that halts your entire operation.
Imagine this: your team is working against a tight deadline. A critical application needs an update, but the user doesn’t have permission to install it. Frustration builds. The quickest fix? Give them local admin rights. Problem solved, right? Not quite. That single decision could open the door to a cyberattack that halts your entire operation.
Read full post on kybersecure.comMSPdb™ News
What Services Do MSPs Actually Provide for Calgary Businesses?
What Services Do MSPs Actually Provide in Calgary? | PCe Solutions What Services Do MSPs Actually Provide for Calgary Businesses? By Peter Perez, Founder & Owner — PCe Solutions | Calgary, Alberta Managed IT services covers far more than helpdesk support — PCe Solutions delivers the full stack of technology management that Calgary businesses need...
What Services Do MSPs Actually Provide in Calgary? | PCe Solutions What Services Do MSPs Actually Provide for Calgary Businesses? By Peter Perez, Founder & Owner — PCe Solutions | Calgary, Alberta Managed IT services covers far more than helpdesk support — PCe Solutions delivers the full stack of technology management that Calgary businesses need...
Read full post on pcesolutions.ca
The AI Skills Gap: How to Diagnose It Before You Train Your Team
Direct answer: Diagnosing your team's AI skills gap means measuring four things before you spend a dollar on training: what tools your employees are already using, which roles stand to gain the most from AI, where each team falls on a simple fluency scale, and how current AI use ties to actual business outcomes. Skip the diagnostic, and you are training blind.
Direct answer: Diagnosing your team's AI skills gap means measuring four things before you spend a dollar on training: what tools your employees are already using, which roles stand to gain the most from AI, where each team falls on a simple fluency scale, and how current AI use ties to actual business outcomes. Skip the diagnostic, and you are training blind.
Read full post on sentrytechsolutions.com
Beyond the Office: Securing Your Data with Offsite Backup
Secure your data against disasters & cyberattacks. Explore a complete guide to implement an effective business offsite backup strategy.
Secure your data against disasters & cyberattacks. Explore a complete guide to implement an effective business offsite backup strategy.
Read full post on mytekrescue.com
Maximizing ROI in Financial Institutions with Managed IT Services
In today’s financial services landscape, IT is no longer just a support function; it’s a strategic investment that directly impacts profitability, risk, and customer experience. Yet many mid-sized financial institutions still struggle to clearly quantify the return on their IT spend. That’s where a Managed IT Services partner like MIS.tech changes the equation. By shifting
In today’s financial services landscape, IT is no longer just a support function; it’s a strategic investment that directly impacts profitability, risk, and customer experience. Yet many mid-sized financial institutions still struggle to clearly quantify the return on their IT spend. That’s where a Managed IT Services partner like MIS.tech changes the equation. By shifting
Read full post on mis.tech
Cloud Computing in Manufacturing: What It Actually Means For The Plant Floor
Cloud computing in manufacturing means moving specific workloads like ERP, monitoring, and analytics to cloud platforms for better visibility, resilience, and scale. Most manufacturers...
Cloud computing in manufacturing means moving specific workloads like ERP, monitoring, and analytics to cloud platforms for better visibility, resilience, and scale. Most manufacturers...
Read full post on letscale.com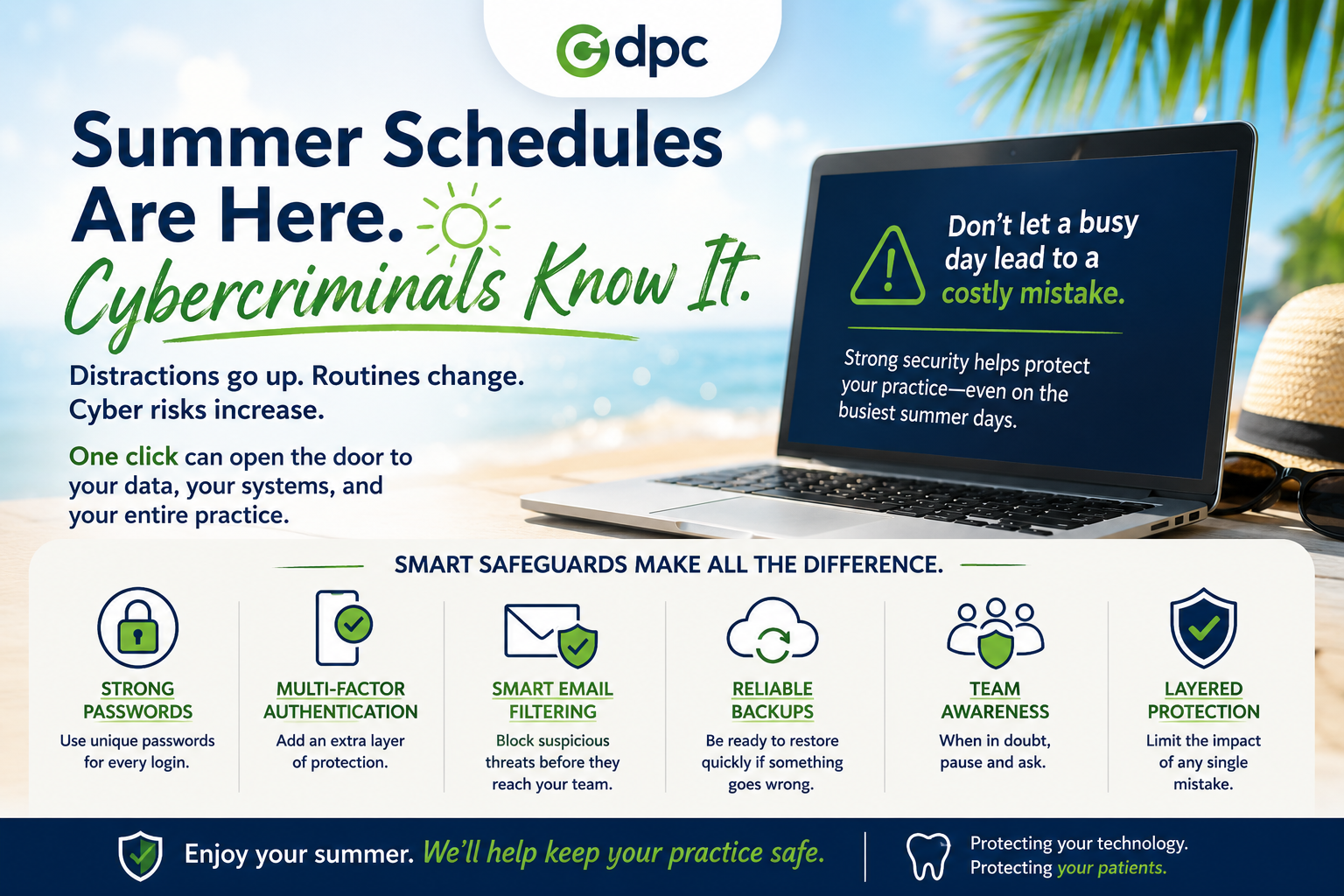
Summer Schedules Are Here. Cybercriminals Know It.
Summer Schedules Are Here. Cybercriminals Know It. Summer is a welcome change of pace. Kids are out of school. Vacations are on the calendar. Team members are taking well-deserved time
Summer Schedules Are Here. Cybercriminals Know It. Summer is a welcome change of pace. Kids are out of school. Vacations are on the calendar. Team members are taking well-deserved time
Read full post on dpctechnology.com
Your MSP Should Not Be Making IT More Complicated
After reading a disappointing article from another MSP that seemed to confuse complexity with value, Leapfrog Services CTO Emmett “Trey” Hawkins III felt compelled to offer a clearer point of view. In this Frogview, Trey explains why the best MSPs do not pile on products, platforms, and noise. They simplify, align, and strengthen IT so ... Read more
After reading a disappointing article from another MSP that seemed to confuse complexity with value, Leapfrog Services CTO Emmett “Trey” Hawkins III felt compelled to offer a clearer point of view. In this Frogview, Trey explains why the best MSPs do not pile on products, platforms, and noise. They simplify, align, and strengthen IT so ... Read more
Read full post on leapfrogservices.com
Fractional CIO & vCISO Services: The Complete Guide
Mid-market businesses are caught in a bind: you need executive-level IT strategy and security leadership, but a full-time CIO or CISO comes with a six-figure salary, a months-long hiring process, and the organizational weight of a permanent C-suite addition that many growing companies aren’t ready to absorb. Fractional CIO and vCISO services exist to solve ... Read more
Mid-market businesses are caught in a bind: you need executive-level IT strategy and security leadership, but a full-time CIO or CISO comes with a six-figure salary, a months-long hiring process, and the organizational weight of a permanent C-suite addition that many growing companies aren’t ready to absorb. Fractional CIO and vCISO services exist to solve ... Read more
Read full post on meriplex.com
Why Device Lifecycle Management Matters More Than Ever
Why Device Lifecycle Management Matters More Than Ever The shift to hybrid work was supposed to be temporary. Then it wasn’t. Today, IT teams at small and mid-sized businesses are managing a sprawling, distributed fleet of devices they never planned for, many of which operate entirely outside traditional oversight. Device lifecycle management has moved from
Why Device Lifecycle Management Matters More Than Ever The shift to hybrid work was supposed to be temporary. Then it wasn’t. Today, IT teams at small and mid-sized businesses are managing a sprawling, distributed fleet of devices they never planned for, many of which operate entirely outside traditional oversight. Device lifecycle management has moved from
Read full post on velonexit.com
Building a Long-Lasting Partnership with Your Managed IT Service Provider
A managed IT service provider does much more than resolve technical issues. For example, the right partner helps businesses proactively manage technology, reduce risks, and plan for future growth. A long-term partnership with a managed IT service provider creates consistency. Additionally, it helps the provider gain a deeper understanding of your operations, goals, and challenges.…
A managed IT service provider does much more than resolve technical issues. For example, the right partner helps businesses proactively manage technology, reduce risks, and plan for future growth. A long-term partnership with a managed IT service provider creates consistency. Additionally, it helps the provider gain a deeper understanding of your operations, goals, and challenges.…
Read full post on swifttechsolutions.com