Got IT?
Discover leading Managed IT Service Providers across USA, Canada & the United Kingdom.
- 100s of leading MSPs
- Find a MSP near you
- Latest IT news for SMBs

How Long Attackers Stay in a Network Before They’re Discovered
When people imagine a cyberattack, they often picture a dramatic event — systems suddenly shutting down or files becoming encrypted. But many cyber incidents don’t unfold that way. In many cases, attackers quietly gain access to a network and remain there for weeks or even months before being discovered. This period is known as “dwell
When people imagine a cyberattack, they often picture a dramatic event — systems suddenly shutting down or files becoming encrypted. But many cyber incidents don’t unfold that way. In many cases, attackers quietly gain access to a network and remain there for weeks or even months before being discovered. This period is known as “dwell
Read full post on citynet.netMSPdb™ News
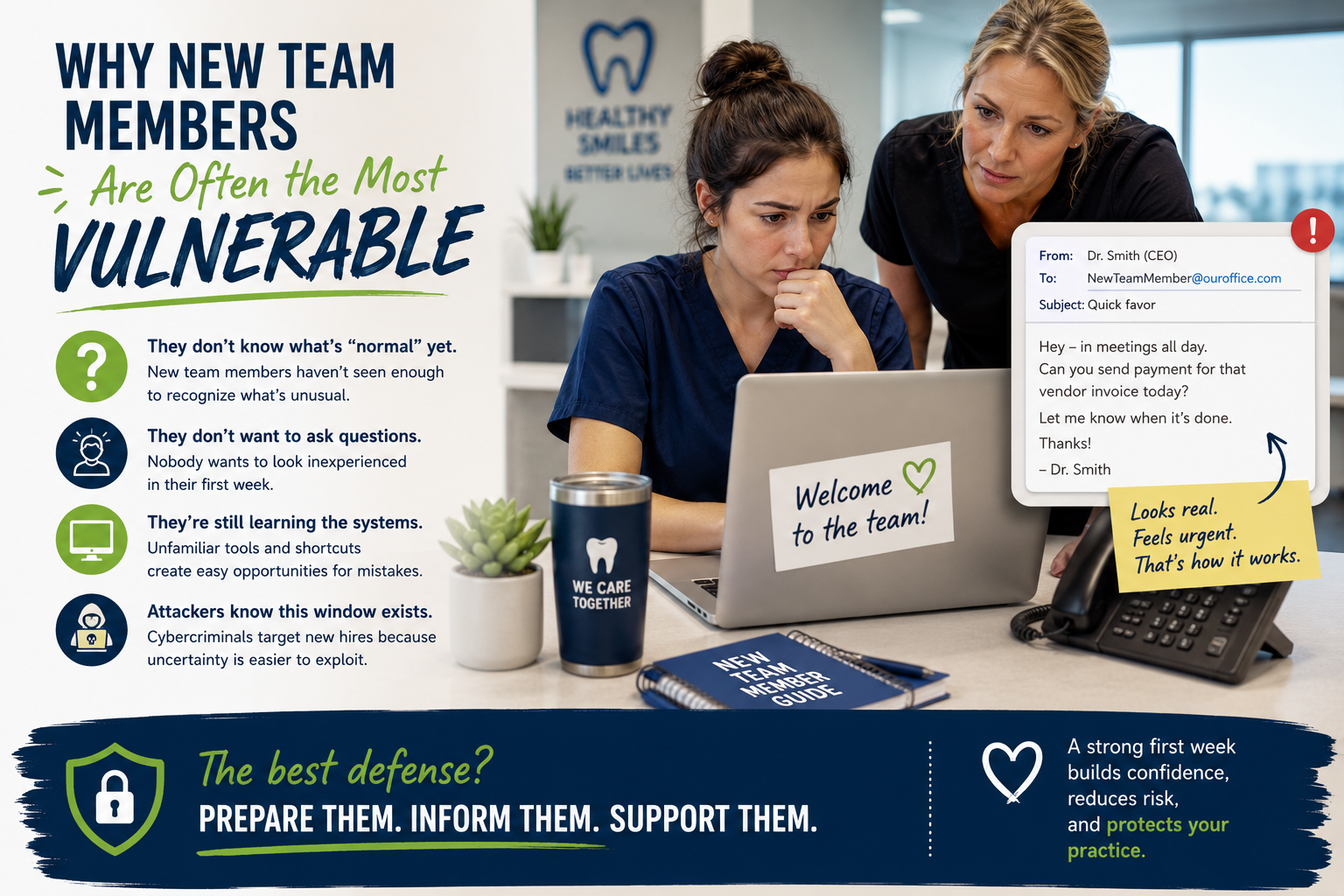
The First Week Mistake No Dental Practice Plans For
The First Week Mistake No Dental Practice Plans For It usually starts with a simple message. “Hey, can you help me with this really quick?” “Can you send over that
The First Week Mistake No Dental Practice Plans For It usually starts with a simple message. “Hey, can you help me with this really quick?” “Can you send over that
Read full post on dpctechnology.com
Copilot Hack: Scheduled Prompts Act as Your Helpful Assistant

Cybersecurity by Inches
Written by Jonathan Perz, Manager of Information Security at Abacus Technologies Quick summary Cybersecurity is not a...
Written by Jonathan Perz, Manager of Information Security at Abacus Technologies Quick summary Cybersecurity is not a...
Read full post on abacustechnologies.com
AI Acceptable Use Policy for Business: Why Every Company Needs One
What is an AI acceptable use policy for business? An AI acceptable use policy for business is a formal document that governs how employees are permitted to use AI tools, which platforms are sanctioned, and what data can and cannot be shared with those systems. Without one, businesses face a growing wave of shadow AI
What is an AI acceptable use policy for business? An AI acceptable use policy for business is a formal document that governs how employees are permitted to use AI tools, which platforms are sanctioned, and what data can and cannot be shared with those systems. Without one, businesses face a growing wave of shadow AI
Read full post on bestructured.com
The Benefits of Upgrading Your IT Strategy with Managed Services
As technology changes, businesses face more pressure to maintain secure, efficient, and scalable IT environments. As a result, traditional IT management approaches are no longer enough to keep up with growing operational demands. Because of this, many businesses are upgrading their IT strategy with managed services. Specifically, they do this to improve performance, reduce downtime,…
As technology changes, businesses face more pressure to maintain secure, efficient, and scalable IT environments. As a result, traditional IT management approaches are no longer enough to keep up with growing operational demands. Because of this, many businesses are upgrading their IT strategy with managed services. Specifically, they do this to improve performance, reduce downtime,…
Read full post on swifttechsolutions.com
What Is the Difference Between Cyber Recovery, Disaster Recovery, and Backup as a Service?
Explore the key differences Cyber Recovery, Disaster Recovery, and Backup and what each really protects When a cyberattack hits your organization, the question is not whether you have backups; it is whether those backups are clean, isolated, and recoverable in hours, not days. Most businesses have invested in Backup as a Service (BaaS) or Disaster
Explore the key differences Cyber Recovery, Disaster Recovery, and Backup and what each really protects When a cyberattack hits your organization, the question is not whether you have backups; it is whether those backups are clean, isolated, and recoverable in hours, not days. Most businesses have invested in Backup as a Service (BaaS) or Disaster
Read full post on xigentsolutions.com
Remote IT Support in Dallas | Tools, Setup & Security Guide 2026
Remote IT support in Dallas has become the preferred choice for growing DFW businesses that need fast, reliable IT help without the cost of an in-house team. Whether your team works from the office, from home, or across multiple locations
Remote IT support in Dallas has become the preferred choice for growing DFW businesses that need fast, reliable IT help without the cost of an in-house team. Whether your team works from the office, from home, or across multiple locations
Read full post on ightysupport.com
External Penetration Testing: Why It Matters for Your Business
Today’s volatile cybersecurity environment calls for a much more in-depth approach to monitoring, like external penetration testing.
Today’s volatile cybersecurity environment calls for a much more in-depth approach to monitoring, like external penetration testing.
Read full post on calitgroup.com
What Is Third-Party Vendor Risk Management?
Third-party vendor risk management is the process of identifying, assessing, and reducing risks caused by external service providers that your business depends on.
Third-party vendor risk management is the process of identifying, assessing, and reducing risks caused by external service providers that your business depends on.
Read full post on coretechllc.com
How to Choose the Right Managed IT Services Provider in St. Louis
Finding the right managed IT services provider can make a big difference for businesses in St. Louis. With technology playing a key role in daily operations, having a reliable partner to manage IT needs is essential. Midwest Networking Services is one of the local companies known for delivering quality IT support, but how do you decide if they or another provider is the best fit for your business? This guide breaks down what to look for when choosing a managed IT services company in St....
Finding the right managed IT services provider can make a big difference for businesses in St. Louis. With technology playing a key role in daily operations, having a reliable partner to manage IT needs is essential. Midwest Networking Services is one of the local companies known for delivering quality IT support, but how do you decide if they or another provider is the best fit for your business? This guide breaks down what to look for when choosing a managed IT services company in St....
Read full post on midwestnetworking.com