We do IT for you.
Discover leading Managed IT Service Providers across USA, Canada & the United Kingdom.
- 100s of leading MSPs
- Find a MSP near you
- Latest IT news for SMBs
Discover how to strategically embrace AI to improve marketing productivity, clean data, repurpose content, streamline CR...

How to Boost Your Company’s Marketing Power with AI
Discover how to strategically embrace AI to improve marketing productivity, clean data, repurpose content, streamline CRM workflows, and create professional marketing assets faster.
Discover how to strategically embrace AI to improve marketing productivity, clean data, repurpose content, streamline CRM workflows, and create professional marketing assets faster.
Read full post on snaptechit.com
Education IT Infrastructure Planning: Dell Solutions for K-12 and Higher Education
Education IT infrastructure planning now needs to account for classrooms, student data, cybersecurity, cloud access, and long-term support across K-12 and higher education environments. The scope has moved beyond isolated device purchases or server upgrades. Each decision affects the environment around it, from network capacity and access controls to how student data is stored, protected, and recovered. The priorities that matter most span K-12 IT infrastructure and higher education IT solutions, from classroom technology infrastructure and student data systems to FERPA-aware planning and rese
Education IT infrastructure planning now needs to account for classrooms, student data, cybersecurity, cloud access, and long-term support across K-12 and higher education environments. The scope has moved beyond isolated device purchases or server upgrades. Each decision affects the environment around it, from network capacity and access controls to how student data is stored, protected, and recovered. The priorities that matter most span K-12 IT infrastructure and higher education IT solutions, from classroom technology infrastructure and student data systems to FERPA-aware planning and research computing in education. What follows is a practical look at where Dell solutions for education fit within a broader strategy. For a broader look at the infrastructure behind education IT planning, our guide to Dell Data Center Solutions for Modern Enterprise IT is a useful next read. Why Education IT Infrastructure Planning Needs a Broader View Education IT infrastructure planning covers more than any single system or upgrade. Classrooms, student records, administrative platforms, cloud tools, and cybersecurity controls all depend on the same underlying environment. When one piece changes, it affects how everything else runs and gets supported. Isolated upgrades can leave schools or universities with an environment that becomes harder to support, secure, and budget
Read full post on davenportgroup.comManaged IT Services Consulting, Sales and Blockchain Technology
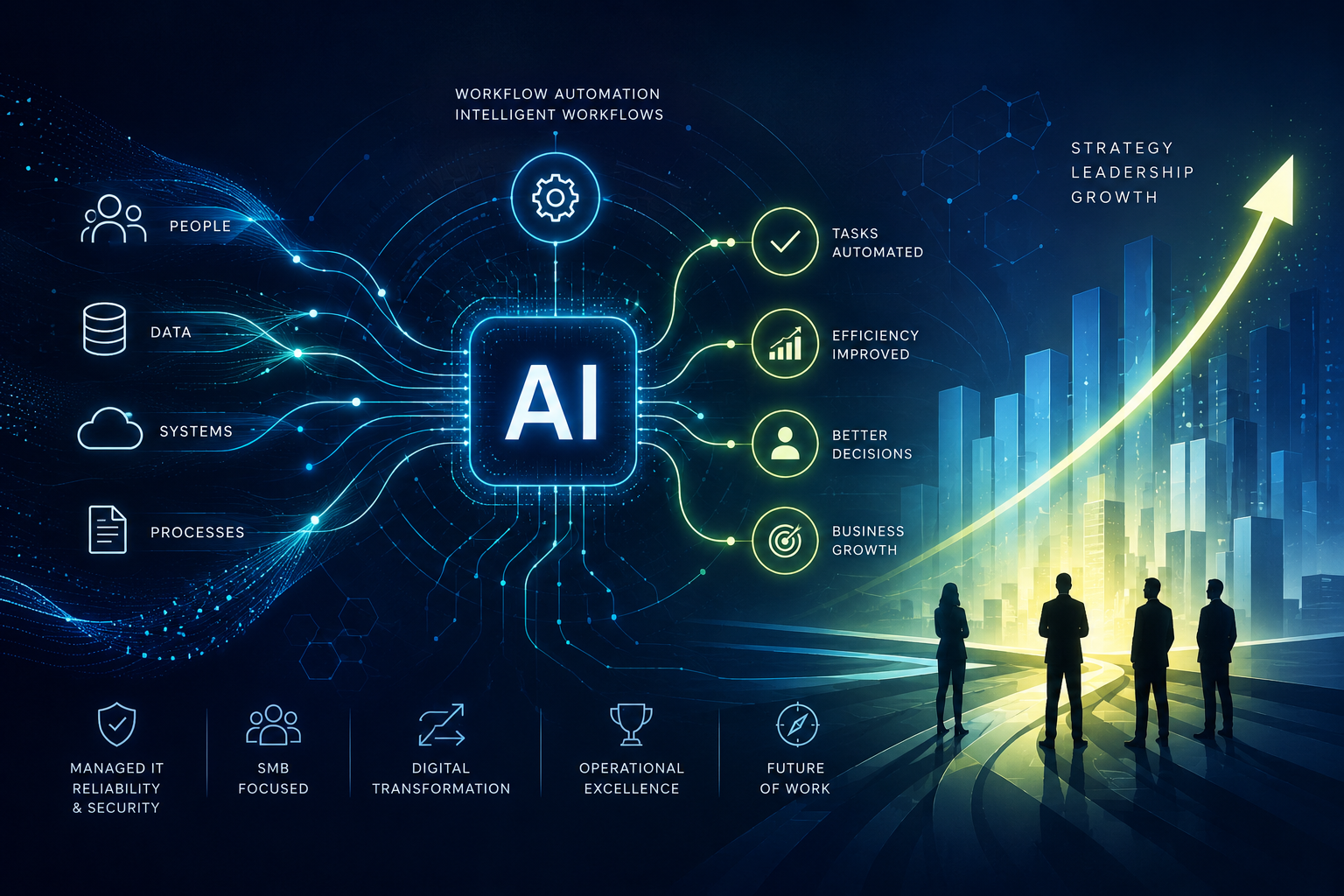
AI Does Not Create Efficiency. Better AI Workflows Do.
Are Your AI Workflows Helping Or Hindering? One of the most common assumptions businesses make about AI is that faster automatically means better. A report that takes five minutes instead of thirty feels like progress. An email drafted in seconds feels efficient. A workflow with more automation appears modern and...
Are Your AI Workflows Helping Or Hindering? One of the most common assumptions businesses make about AI is that faster automatically means better. A report that takes five minutes instead of thirty feels like progress. An email drafted in seconds feels efficient. A workflow with more automation appears modern and...
Read full post on pctronics.usChoose the best managed MDU internet provider in the USA. Learn what to look for, compare options, and improve resident satisfaction and retention.

How to Choose Managed MDU Internet in the USA - Datavalet
Choose the best managed MDU internet provider in the USA. Learn what to look for, compare options, and improve resident satisfaction and retention.
Choose the best managed MDU internet provider in the USA. Learn what to look for, compare options, and improve resident satisfaction and retention.
Read full post on datavalet.comUnlock Business Growth With Microsoft Integration Disjointed software applications can act as heavy anchors, slowing down innovation and frustrating y...

Microsoft Integration Strategies to Boost Business Growth
Unlock Business Growth With Microsoft Integration Disjointed software applications can act as heavy anchors, slowing down innovation and frustrating your workforce. Employees waste valuable hours toggling between apps, searching for scattered data, and manually transferring information. If your organization relies on a fragmented tech stack, implementing effective Microsoft integration strategies for business growth can be
Unlock Business Growth With Microsoft Integration Disjointed software applications can act as heavy anchors, slowing down innovation and frustrating your workforce. Employees waste valuable hours toggling between apps, searching for scattered data, and manually transferring information. If your organization relies on a fragmented tech stack, implementing effective Microsoft integration strategies for business growth can be
Read full post on appliedtech.usPublic sector organizations are under pressure from every direction. Modernize services. Protect citizen data. Meet compliance expectations. Respon...

Cyber Resilience in the Public Sector: A Practical Framework for Safer, More Accountable Operations
Public sector organizations are under pressure from every direction. Modernize services. Protect citizen data. Meet compliance expectations. Respond faster when something goes sideways. Easy, right? Not exactly. For state and local agencies, cybersecurity has moved well beyond firewalls, antivirus, and annual check-the-box assessments. It is now tied directly to service continuity, public trust, funding requirements, audit readiness, and operational resilience. The question isn't, “Do we have enough cybersecurity tools?” but rather, “Are we actually using the tools to reduce risk?”
Public sector organizations are under pressure from every direction. Modernize services. Protect citizen data. Meet compliance expectations. Respond faster when something goes sideways. Easy, right? Not exactly. For state and local agencies, cybersecurity has moved well beyond firewalls, antivirus, and annual check-the-box assessments. It is now tied directly to service continuity, public trust, funding requirements, audit readiness, and operational resilience. The question isn't, “Do we have enough cybersecurity tools?” but rather, “Are we actually using the tools to reduce risk?”
Read full post on blog.vectorusa.comWhen asked if they have a continuity plan, most businesses in Bowling Green would actually say yes. And then they’d go on and talk about how they have...

What Is Business Continuity Recovery Planning and Why Does It Actually Work?
When asked if they have a continuity plan, most businesses in Bowling Green would actually say yes. And then they’d go on and talk about how they have all sorts of backups, even some emergency contacts, and how they fully expect that things will be fine during a crisis. There’s no gentle way to put it, but that’s not really a plan. It’s just plain optimism. Business continuity recovery planning is so much more than that. It turns hope into a documented, tested, and repeatable business continuity recovery process that works when systems fail, offices close, or cyberattacks hit. And when it’s do
When asked if they have a continuity plan, most businesses in Bowling Green would actually say yes. And then they’d go on and talk about how they have all sorts of backups, even some emergency contacts, and how they fully expect that things will be fine during a crisis. There’s no gentle way to put it, but that’s not really a plan. It’s just plain optimism. Business continuity recovery planning is so much more than that. It turns hope into a documented, tested, and repeatable business continuity recovery process that works when systems fail, offices close, or cyberattacks hit. And when it’s done right, it won’t simply reduce downtime, but also create confidence across your entire organization.
Read full post on coretechllc.comWith new HIPAA rules coming into play in 2026, covered entities must engage the right IT and cybersecurity services to facilitate their compliance jou...

Top Healthcare IT Services for HIPAA Compliance
With new HIPAA rules coming into play in 2026, covered entities must engage the right IT and cybersecurity services to facilitate their compliance journeys. But which services actually help? Can an MSP (managed service provider) guarantee compliance? (No, they cannot.) We’ve got all the answers in this article. Key takeaways: HIPAA compliance services are professional
With new HIPAA rules coming into play in 2026, covered entities must engage the right IT and cybersecurity services to facilitate their compliance journeys. But which services actually help? Can an MSP (managed service provider) guarantee compliance? (No, they cannot.) We’ve got all the answers in this article. Key takeaways: HIPAA compliance services are professional
Read full post on corsicatech.comData center projects are facing new forecasting risk as power delays, grid interconnection issues, and long-lead commitments affect cash timing, margi...

Why Half of Active Data Center Builds Have Hit Setbacks
Data center projects are facing new forecasting risk as power delays, grid interconnection issues, and long-lead commitments affect cash timing, margins, and financial controls.
Data center projects are facing new forecasting risk as power delays, grid interconnection issues, and long-lead commitments affect cash timing, margins, and financial controls.
Read full post on swktech.comGlobal Leader in Administrative, IT & Financial Managed Services for Legal.

Frontline Managed Services Expands Executive Leadership Team to Support Continued Growth and Innovation for the Legal Sector
Frontline Managed Services Expands Executive Leadership Team to Support Continued Growth and Innovation for the Legal Sector Eric Westrom Named Chief Executive of IT Services and Chief Information Officer; Pinakin Sheth Appointed Chief Financial Officer; Kate Jones Joins as Vice President of Marketing ST. LOUIS, MO — [June 4, 2026] — Frontline Managed Services, a
Frontline Managed Services Expands Executive Leadership Team to Support Continued Growth and Innovation for the Legal Sector Eric Westrom Named Chief Executive of IT Services and Chief Information Officer; Pinakin Sheth Appointed Chief Financial Officer; Kate Jones Joins as Vice President of Marketing ST. LOUIS, MO — [June 4, 2026] — Frontline Managed Services, a
Read full post on frontlinems.comAccording to the National Oceanic and Atmospheric Administration (NOAA), the 2026 Atlantic hurricane season is expected to produce 8 to 14 named s...

Hurricane Season and Business Continuity: Is Your Technology Ready?
According to the National Oceanic and Atmospheric Administration (NOAA), the 2026 Atlantic hurricane season is expected to produce 8 to 14 named storms, including 3 to 6 hurricanes and 1 to 3 major hurricanes. While NOAA forecasts a below-normal season, Florida businesses know that a single storm can disrupt operations for days or
According to the National Oceanic and Atmospheric Administration (NOAA), the 2026 Atlantic hurricane season is expected to produce 8 to 14 named storms, including 3 to 6 hurricanes and 1 to 3 major hurricanes. While NOAA forecasts a below-normal season, Florida businesses know that a single storm can disrupt operations for days or
Read full post on kustura.com
Business Continuity Planning: Why It Matters More Than You Think
In this post, we'll explore what business continuity planning actually is, why it's critical for professional services, the most common causes of downtime, and the practical strategies you can implement to keep your business running when problems occur.
In this post, we'll explore what business continuity planning actually is, why it's critical for professional services, the most common causes of downtime, and the practical strategies you can implement to keep your business running when problems occur.
Read full post on gocourant.comMost business owners think about cybersecurity the wrong way. They picture it as a single moment — the day they buy the software, hire the IT guy, or...

Why Saving Money on IT Often Costs More Than You Think
Most business owners think about cybersecurity the wrong way. They picture it as a single moment — the day they buy the software, hire the IT guy, or sign off on the policy. Box checked. Done. Back to running the business.
Most business owners think about cybersecurity the wrong way. They picture it as a single moment — the day they buy the software, hire the IT guy, or sign off on the policy. Box checked. Done. Back to running the business.
Read full post on lddconsulting.comWhat Services Do MSPs Actually Provide in Calgary? | PCe Solutions What Services Do MSPs Actually Provide for Calgary Businesses? By Peter Perez, Foun...
What Services Do MSPs Actually Provide for Calgary Businesses?
What Services Do MSPs Actually Provide in Calgary? | PCe Solutions What Services Do MSPs Actually Provide for Calgary Businesses? By Peter Perez, Founder & Owner — PCe Solutions | Calgary, Alberta Managed IT services covers far more than helpdesk support — PCe Solutions delivers the full stack of technology management that Calgary businesses need...
What Services Do MSPs Actually Provide in Calgary? | PCe Solutions What Services Do MSPs Actually Provide for Calgary Businesses? By Peter Perez, Founder & Owner — PCe Solutions | Calgary, Alberta Managed IT services covers far more than helpdesk support — PCe Solutions delivers the full stack of technology management that Calgary businesses need...
Read full post on pcesolutions.caServing businesses with Cyber Security, Managed IT, Compliance and AI Implementation.

The AI Skills Gap: How to Diagnose It Before You Train Your Team
Direct answer: Diagnosing your team's AI skills gap means measuring four things before you spend a dollar on training: what tools your employees are already using, which roles stand to gain the most from AI, where each team falls on a simple fluency scale, and how current AI use ties to actual business outcomes. Skip the diagnostic, and you are training blind.
Direct answer: Diagnosing your team's AI skills gap means measuring four things before you spend a dollar on training: what tools your employees are already using, which roles stand to gain the most from AI, where each team falls on a simple fluency scale, and how current AI use ties to actual business outcomes. Skip the diagnostic, and you are training blind.
Read full post on sentrytechsolutions.com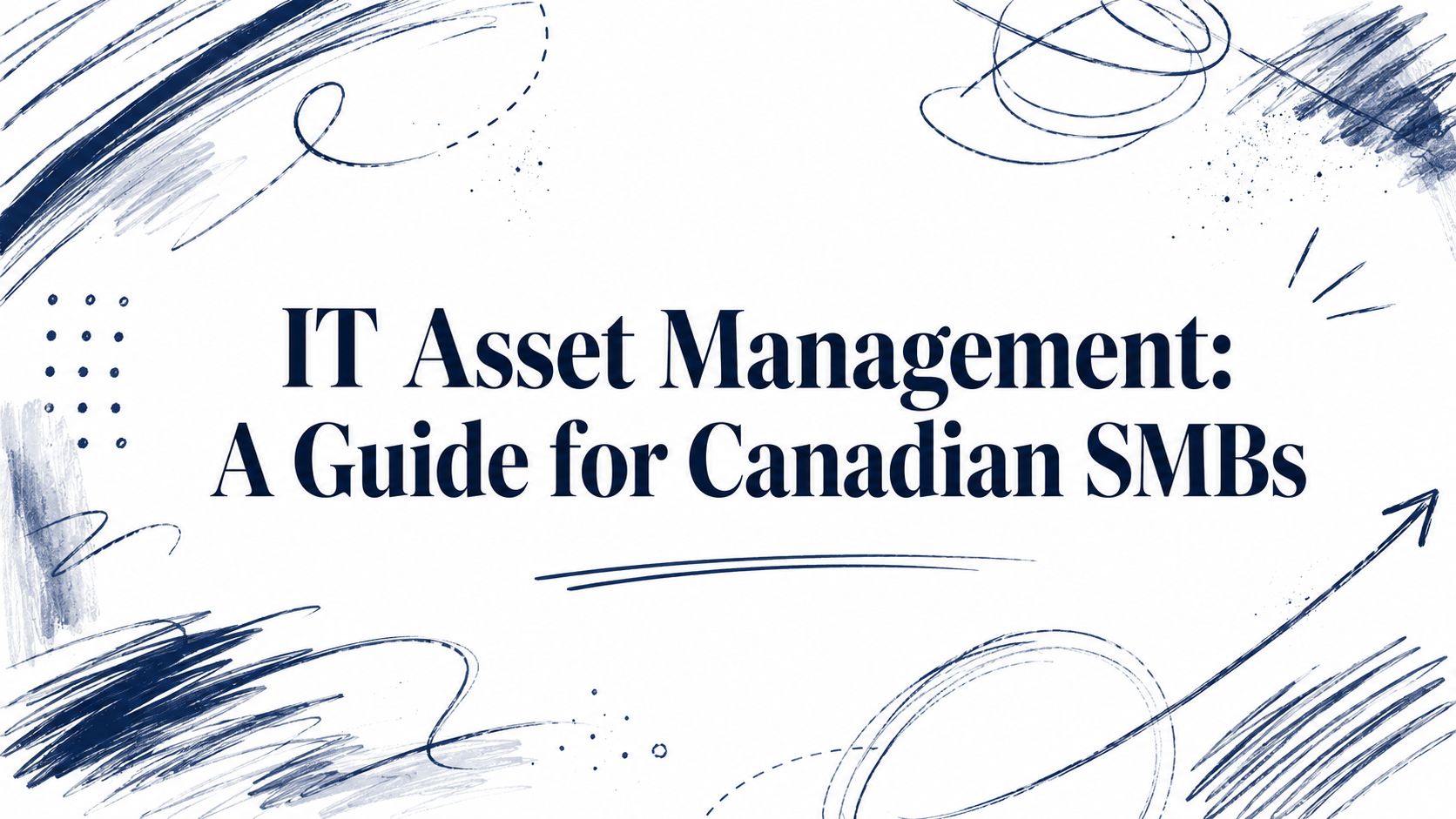
IT Asset Management: A Guide for Canadian SMBs
Learn how effective IT asset management can boost security, control costs, and drive growth for your Canadian SMB. A practical guide to getting started.
Learn how effective IT asset management can boost security, control costs, and drive growth for your Canadian SMB. A practical guide to getting started.
Read full post on cloudorbis.com
Beyond the Office: Securing Your Data with Offsite Backup
Secure your data against disasters & cyberattacks. Explore a complete guide to implement an effective business offsite backup strategy.
Secure your data against disasters & cyberattacks. Explore a complete guide to implement an effective business offsite backup strategy.
Read full post on mytekrescue.com
Maximizing ROI in Financial Institutions with Managed IT Services
In today’s financial services landscape, IT is no longer just a support function; it’s a strategic investment that directly impacts profitability, risk, and customer experience. Yet many mid-sized financial institutions still struggle to clearly quantify the return on their IT spend. That’s where a Managed IT Services partner like MIS.tech changes the equation. By shifting
In today’s financial services landscape, IT is no longer just a support function; it’s a strategic investment that directly impacts profitability, risk, and customer experience. Yet many mid-sized financial institutions still struggle to clearly quantify the return on their IT spend. That’s where a Managed IT Services partner like MIS.tech changes the equation. By shifting
Read full post on mis.tech
Cloud Computing in Manufacturing: What It Actually Means For The Plant Floor
Cloud computing in manufacturing means moving specific workloads like ERP, monitoring, and analytics to cloud platforms for better visibility, resilience, and scale. Most manufacturers...
Cloud computing in manufacturing means moving specific workloads like ERP, monitoring, and analytics to cloud platforms for better visibility, resilience, and scale. Most manufacturers...
Read full post on letscale.com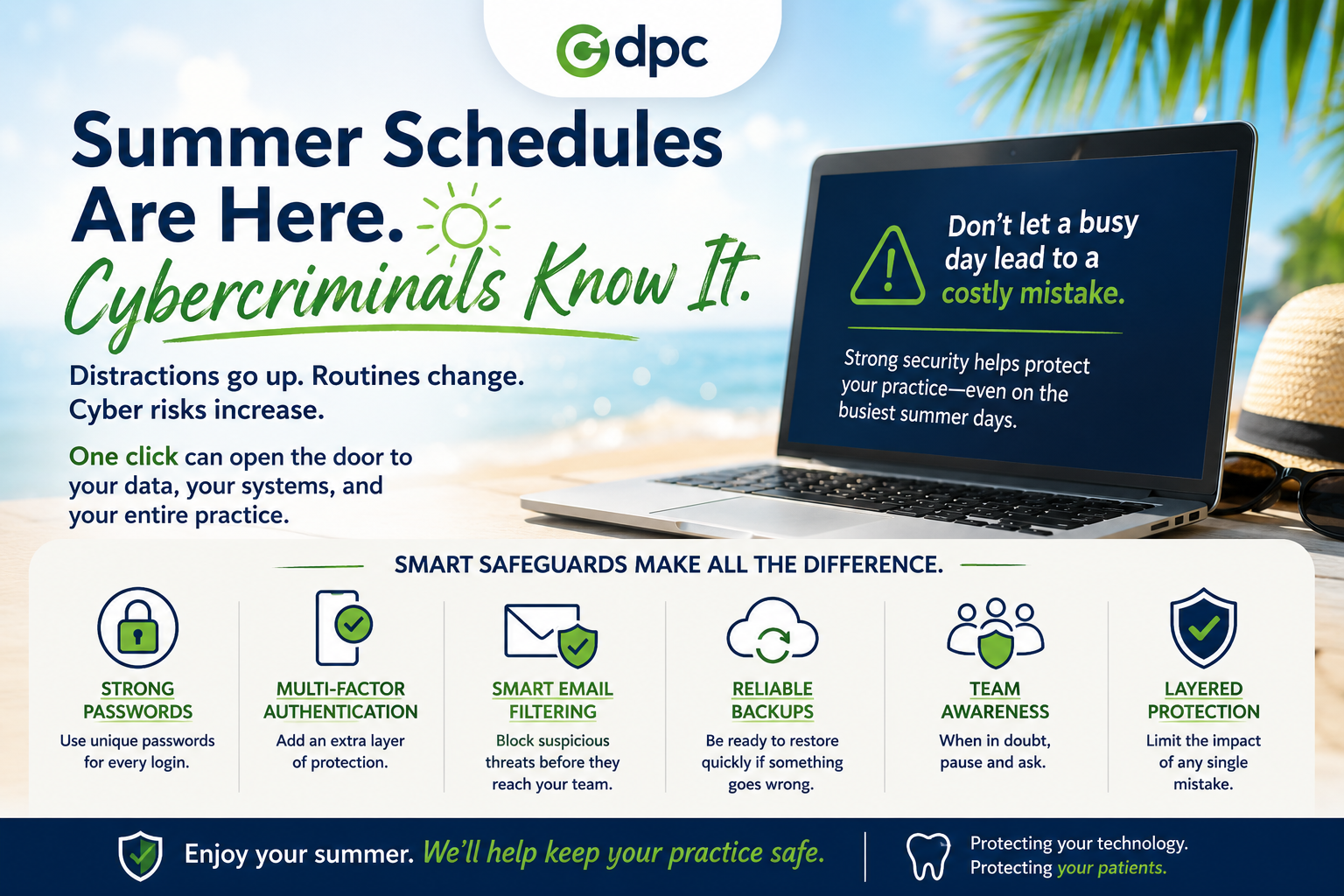
Summer Schedules Are Here. Cybercriminals Know It.
Summer Schedules Are Here. Cybercriminals Know It. Summer is a welcome change of pace. Kids are out of school. Vacations are on the calendar. Team members are taking well-deserved time
Summer Schedules Are Here. Cybercriminals Know It. Summer is a welcome change of pace. Kids are out of school. Vacations are on the calendar. Team members are taking well-deserved time
Read full post on dpctechnology.com
Your MSP Should Not Be Making IT More Complicated
After reading a disappointing article from another MSP that seemed to confuse complexity with value, Leapfrog Services CTO Emmett “Trey” Hawkins III felt compelled to offer a clearer point of view. In this Frogview, Trey explains why the best MSPs do not pile on products, platforms, and noise. They simplify, align, and strengthen IT so ... Read more
After reading a disappointing article from another MSP that seemed to confuse complexity with value, Leapfrog Services CTO Emmett “Trey” Hawkins III felt compelled to offer a clearer point of view. In this Frogview, Trey explains why the best MSPs do not pile on products, platforms, and noise. They simplify, align, and strengthen IT so ... Read more
Read full post on leapfrogservices.com
Fractional CIO & vCISO Services: The Complete Guide
Mid-market businesses are caught in a bind: you need executive-level IT strategy and security leadership, but a full-time CIO or CISO comes with a six-figure salary, a months-long hiring process, and the organizational weight of a permanent C-suite addition that many growing companies aren’t ready to absorb. Fractional CIO and vCISO services exist to solve ... Read more
Mid-market businesses are caught in a bind: you need executive-level IT strategy and security leadership, but a full-time CIO or CISO comes with a six-figure salary, a months-long hiring process, and the organizational weight of a permanent C-suite addition that many growing companies aren’t ready to absorb. Fractional CIO and vCISO services exist to solve ... Read more
Read full post on meriplex.com
Why Device Lifecycle Management Matters More Than Ever
Why Device Lifecycle Management Matters More Than Ever The shift to hybrid work was supposed to be temporary. Then it wasn’t. Today, IT teams at small and mid-sized businesses are managing a sprawling, distributed fleet of devices they never planned for, many of which operate entirely outside traditional oversight. Device lifecycle management has moved from
Why Device Lifecycle Management Matters More Than Ever The shift to hybrid work was supposed to be temporary. Then it wasn’t. Today, IT teams at small and mid-sized businesses are managing a sprawling, distributed fleet of devices they never planned for, many of which operate entirely outside traditional oversight. Device lifecycle management has moved from
Read full post on velonexit.com
Building a Long-Lasting Partnership with Your Managed IT Service Provider
A managed IT service provider does much more than resolve technical issues. For example, the right partner helps businesses proactively manage technology, reduce risks, and plan for future growth. A long-term partnership with a managed IT service provider creates consistency. Additionally, it helps the provider gain a deeper understanding of your operations, goals, and challenges.…
A managed IT service provider does much more than resolve technical issues. For example, the right partner helps businesses proactively manage technology, reduce risks, and plan for future growth. A long-term partnership with a managed IT service provider creates consistency. Additionally, it helps the provider gain a deeper understanding of your operations, goals, and challenges.…
Read full post on swifttechsolutions.com
What is a ClickFix Scam and How Do You Protect Yourself?

Key Takeaways from Crowdstrike's Global Threat Report
The world of cybersecurity is entering what experts call the "agentic era." Companies are handing the keys over to smart AI agents to write code, manage cloud systems, and handle day-to-day work at lightning speed.
The world of cybersecurity is entering what experts call the "agentic era." Companies are handing the keys over to smart AI agents to write code, manage cloud systems, and handle day-to-day work at lightning speed.
Read full post on allcovered.com
The ROI of a Managed AI Strategy: Real Outcomes for Construction, Education & Nonprofit Organizations
Artificial intelligence is no longer a future-state technology reserved for Fortune 500 companies. It is here, it is accessible, and, when implemented through a strategic, managed framework, it is delivering real, quantifiable returns for organizations of every size, including the construction firm bidding on its next project, the school district managing 3,000 students, and the
Artificial intelligence is no longer a future-state technology reserved for Fortune 500 companies. It is here, it is accessible, and, when implemented through a strategic, managed framework, it is delivering real, quantifiable returns for organizations of every size, including the construction firm bidding on its next project, the school district managing 3,000 students, and the
Read full post on networkoutsource.com
Managed IT Services Statistics & MSP Industry Trends (2026)
This report was compiled by Sagiss, a managed IT service provider serving SMBs in the Dallas-Fort Worth area.
This report was compiled by Sagiss, a managed IT service provider serving SMBs in the Dallas-Fort Worth area.
Read full post on sagiss.com
IT Audit Checks: 6 Critical Midyear Reviews That Prevent Costly Business Disruptions
As businesses move through the second half of the year, many technology problems begin to surface. Not because systems suddenly fail, but because small issues were left unchecked for too long. That’s why midyear IT audit checks are one of the smartest preventative measures an organization can take. A midyear IT audit gives businesses the...
As businesses move through the second half of the year, many technology problems begin to surface. Not because systems suddenly fail, but because small issues were left unchecked for too long. That’s why midyear IT audit checks are one of the smartest preventative measures an organization can take. A midyear IT audit gives businesses the...
Read full post on fogosolutions.com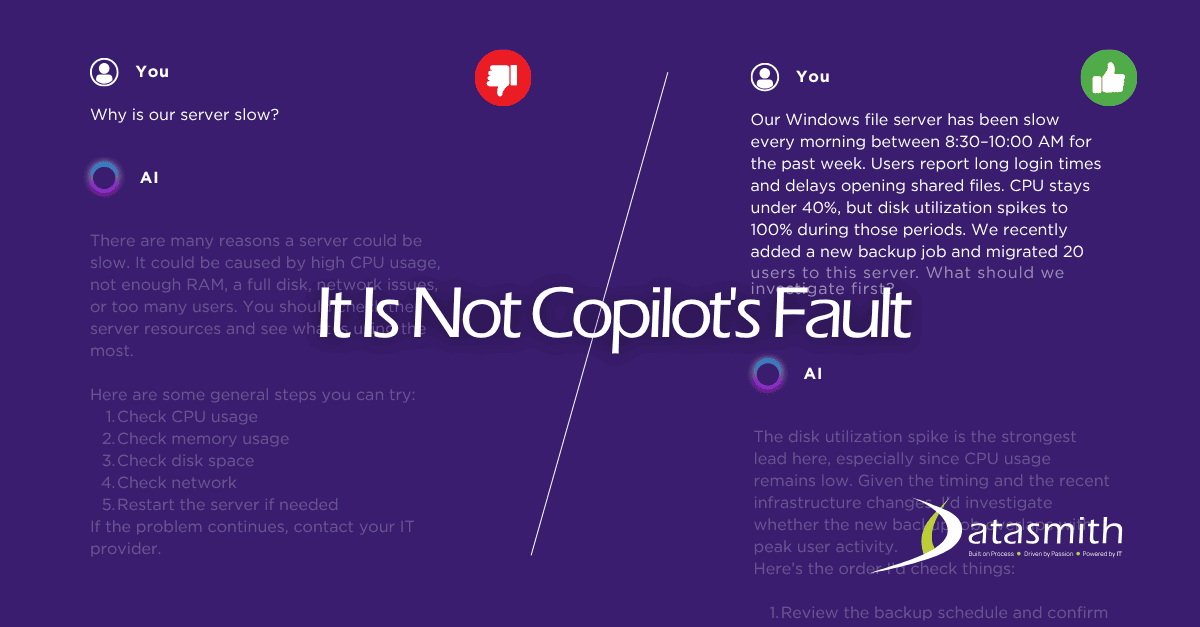
Is Microsoft Copilot a Good AI Tool for Small Businesses? An Honest Answer.
If your business runs on Microsoft 365 and you are wondering whether Copilot is worth your time, the short answer
If your business runs on Microsoft 365 and you are wondering whether Copilot is worth your time, the short answer
Read full post on datasmithnetworks.com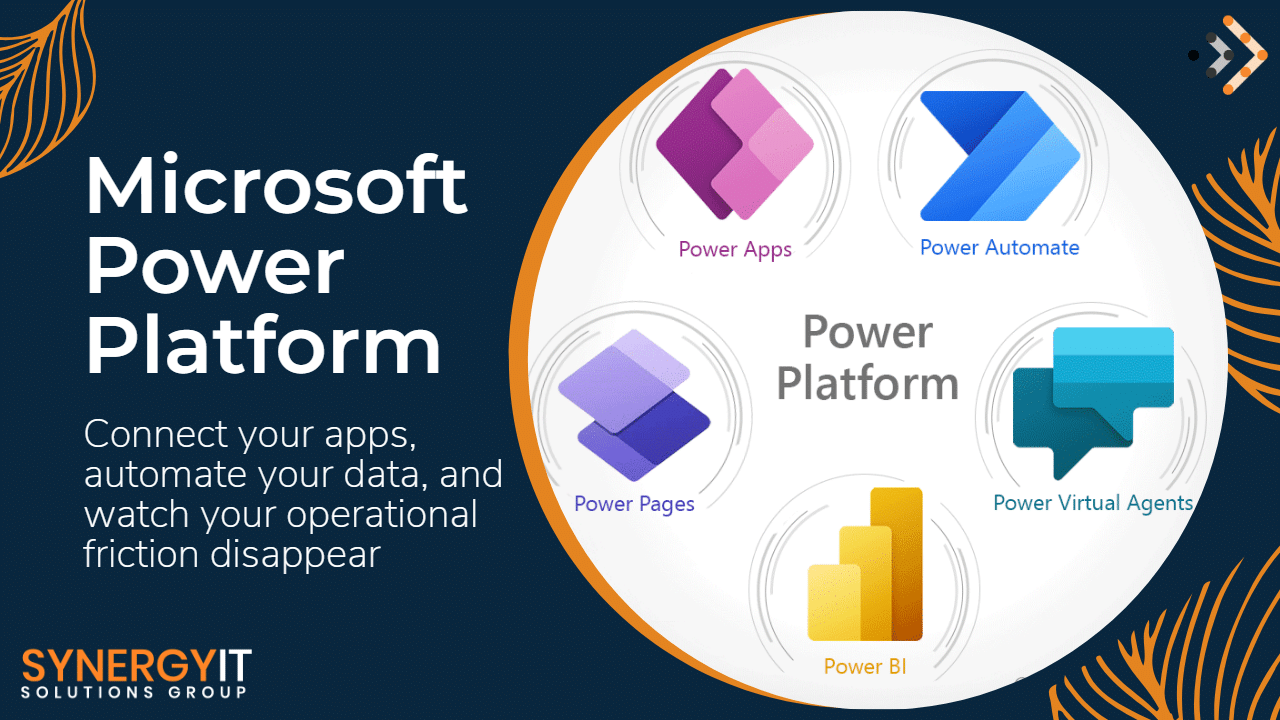
Automate Your Business with Power Automate: Save Time & Costs
Every business leader wants the same thing: more productivity, lower operational costs, and faster growth.…
Every business leader wants the same thing: more productivity, lower operational costs, and faster growth.…
Read full post on blog.synergyit.ca
AI Is Already in Your Business. Who’s Keeping It in Check?
AI probably did not enter your business through a formal rollout. It probably showed up in the tools your team already uses every day, like an AI button in email or another one in a Read More...
AI probably did not enter your business through a formal rollout. It probably showed up in the tools your team already uses every day, like an AI button in email or another one in a Read More...
Read full post on taznetworks.com
Smart Businesses: Top 5 Traits of Ideal IT Partners
In today’s fast-paced digital world, technology is the engine that drives your business forward. For many business owners, managing IT can be a major headache, pulling focus away from core operations. That’s why finding the right IT partner is more important than ever. The ideal partner does more than just fix problems; they provide strategic
In today’s fast-paced digital world, technology is the engine that drives your business forward. For many business owners, managing IT can be a major headache, pulling focus away from core operations. That’s why finding the right IT partner is more important than ever. The ideal partner does more than just fix problems; they provide strategic
Read full post on vcsolutions.com
Zero Trust in Action: Leveraging Microsoft Security Stack to Safeguard the Hybrid Enterprise
Discover how Zero Trust and Microsoft Security Stack safeguard hybrid enterprises from advanced cyber threats. Learn key strategies for 2026.
Discover how Zero Trust and Microsoft Security Stack safeguard hybrid enterprises from advanced cyber threats. Learn key strategies for 2026.
Read full post on trndigital.com
New SharePoint Sharing Rule: What Your Business Needs to Know Before July 2026
All those SharePoint files you’ve shared with clients, vendors or other partners outside your organization could be inaccessible in July 2026. Why? New SharePoint sharing rules start that month. The core change is occurring because Microsoft is moving away from link-based access to a more secure identity-based access model. Every external person you share files…
All those SharePoint files you’ve shared with clients, vendors or other partners outside your organization could be inaccessible in July 2026. Why? New SharePoint sharing rules start that month. The core change is occurring because Microsoft is moving away from link-based access to a more secure identity-based access model. Every external person you share files…
Read full post on skyterratech.comFailed to load more articles
You're all caught up!
Check back later for more home news.
MSPdb™ News

Adversary-in-the-Middle Attacks: How Phishing Sites Steal Your Active Login
You click a link, sign in, approve the MFA prompt, and get on with your day. Completely unaware that someone else just logged into your account at the same moment.That scenario surprises many businesses, particularly those that rely on multi-factor authentication (MFA) to protect cloud accounts. But this is exactly how Adversary-in-the-Middle (AiTM) phishing attacks
You click a link, sign in, approve the MFA prompt, and get on with your day. Completely unaware that someone else just logged into your account at the same moment.That scenario surprises many businesses, particularly those that rely on multi-factor authentication (MFA) to protect cloud accounts. But this is exactly how Adversary-in-the-Middle (AiTM) phishing attacks
Read full post on techriver.com
Selling Your Business? Start with Your Tech Stack
Selling your business? Your tech stack is not a back-office detail. It is a valuation lever. Buyers pay more for companies with clean, documented, secure technology, and discount companies that do not. Start cleaning up your IT two to three years before the sale, not two to three months!
Selling your business? Your tech stack is not a back-office detail. It is a valuation lever. Buyers pay more for companies with clean, documented, secure technology, and discount companies that do not. Start cleaning up your IT two to three years before the sale, not two to three months!
Read full post on sentrytechsolutions.com
Managed IT Services Near Me vs. National Providers: The Local Advantage
Are you comparing managed IT services near you to national providers? See why Cleveland businesses get better results with a local IT partner like infinIT. In This Article: When you search “managed IT services near me,” you’re telling Google something important about what you actually need. You’re not looking for a brand name. You’re looking
Are you comparing managed IT services near you to national providers? See why Cleveland businesses get better results with a local IT partner like infinIT. In This Article: When you search “managed IT services near me,” you’re telling Google something important about what you actually need. You’re not looking for a brand name. You’re looking
Read full post on infinit.us
Essential IT Contract Negotiation Tips for ROI Success
Be honest… how often have you thought about negotiating your IT contract with your provider? Many don’t, and as a result, their businesses are susceptible to slow response times, hidden fees, and set lists of vendors.This isn’t sustainable. A real partnership is, and is established through a balanced contract that promotes proactivity and accountability. Let’s talk about what goes into these types of contracts.
Be honest… how often have you thought about negotiating your IT contract with your provider? Many don’t, and as a result, their businesses are susceptible to slow response times, hidden fees, and set lists of vendors.This isn’t sustainable. A real partnership is, and is established through a balanced contract that promotes proactivity and accountability. Let’s talk about what goes into these types of contracts.
Read full post on coretechllc.com
Tabletop Exercises Explained for Business Continuity
How a two-hour meeting can reveal the gaps in your business continuity plan before a crisis does You have a business continuity plan. You think. Maybe it is a document on a shared drive. Maybe it is a set of procedures your IT provider put together. Maybe it exists mostly in the heads of two
How a two-hour meeting can reveal the gaps in your business continuity plan before a crisis does You have a business continuity plan. You think. Maybe it is a document on a shared drive. Maybe it is a set of procedures your IT provider put together. Maybe it exists mostly in the heads of two
Read full post on novatech.net
Cybersecurity Risk Assessment Checklist: 8 Essential Steps
Download our risk assessment checklist to identify vulnerabilities and strengthen your cybersecurity. Easy steps for effective risk management.
Download our risk assessment checklist to identify vulnerabilities and strengthen your cybersecurity. Easy steps for effective risk management.
Read full post on mytekrescue.com
What Are Network Security Threats and Solutions?
Network security threats are malicious activities that compromise the confidentiality, integrity, or availability of computer networks and connected systems. Common threats include ransomware attacks, phishing campaigns, malware infections, DDoS attacks, man-in-the-middle (MitM) attacks, insider threats, and zero-day exploits. These attacks disrupt operations, expose sensitive information, cause financial losses, and create significant business risks. They may... Source
Network security threats are malicious activities that compromise the confidentiality, integrity, or availability of computer networks and connected systems. Common threats include ransomware attacks, phishing campaigns, malware infections, DDoS attacks, man-in-the-middle (MitM) attacks, insider threats, and zero-day exploits. These attacks disrupt operations, expose sensitive information, cause financial losses, and create significant business risks. They may... Source
Read full post on cloudavize.com
Your IT Staff Is Stretched Thin — Now What?
Direct Answer: When your IT staff is overwhelmed, the practical fix is adding outside support through co-managed IT — not replacing your team, but giving them backup coverage where they need it most. You hired one IT person — maybe two — and for a while, it worked. But somewhere between adding new staff, switching
Direct Answer: When your IT staff is overwhelmed, the practical fix is adding outside support through co-managed IT — not replacing your team, but giving them backup coverage where they need it most. You hired one IT person — maybe two — and for a while, it worked. But somewhere between adding new staff, switching
Read full post on adaptiveis.net
Why Businesses Are Replacing Legacy Firewalls with Next-Generation Security Platforms
Cybersecurity has changed dramatically over the last few years. The traditional firewall that once protected…
Cybersecurity has changed dramatically over the last few years. The traditional firewall that once protected…
Read full post on blog.synergyit.ca
Managed IT for Hybrid Teams
The hybrid work model was supposed to be the best of both worlds. Flexibility for employees, continuity for the business, no more debating whether remote work actually gets anything done. And for a lot of companies, it has delivered on that promise. But it’s also created a layer of IT complexity that most businesses didn’t
The hybrid work model was supposed to be the best of both worlds. Flexibility for employees, continuity for the business, no more debating whether remote work actually gets anything done. And for a lot of companies, it has delivered on that promise. But it’s also created a layer of IT complexity that most businesses didn’t
Read full post on lgnetworksinc.com
Just Added to MSPdb™
MSP 100 - Founders Circle

Is Your IT Playing Like a Champion?
What the Padres and Dodgers Can Teach Businesses About IT It’s baseball season, and if you’re in Southern California, that means arguments about the Padres, Dodgers and the Angels are heating up (well maybe not the Angels). But here’s a question nobody’s asking at the office: does your IT setup play like a championship team
What the Padres and Dodgers Can Teach Businesses About IT It’s baseball season, and if you’re in Southern California, that means arguments about the Padres, Dodgers and the Angels are heating up (well maybe not the Angels). But here’s a question nobody’s asking at the office: does your IT setup play like a championship team
Read full post on networktitan.comMSP Jobs
All JobsMSP Marketplace
View AllMSP Events
View allMSP Summit 2026
Las Vegas, NV
Channel Partners Expo
Orlando, FL
IT Nation Connect
Virtual Event
Sign in to create your MSP event
MSP Marketing
7 Proven Strategies to Generate More MSP Leads in 2026
How to Build a Referral Program That Actually Works
SEO for MSPs: Rank Higher and Get Found by SMBs
Get more leads for your MSP