Let IT Be.
Discover leading Managed IT Service Providers across USA, Canada & the United Kingdom.
- 100s of leading MSPs
- Find a MSP near you
- Latest IT news for SMBs
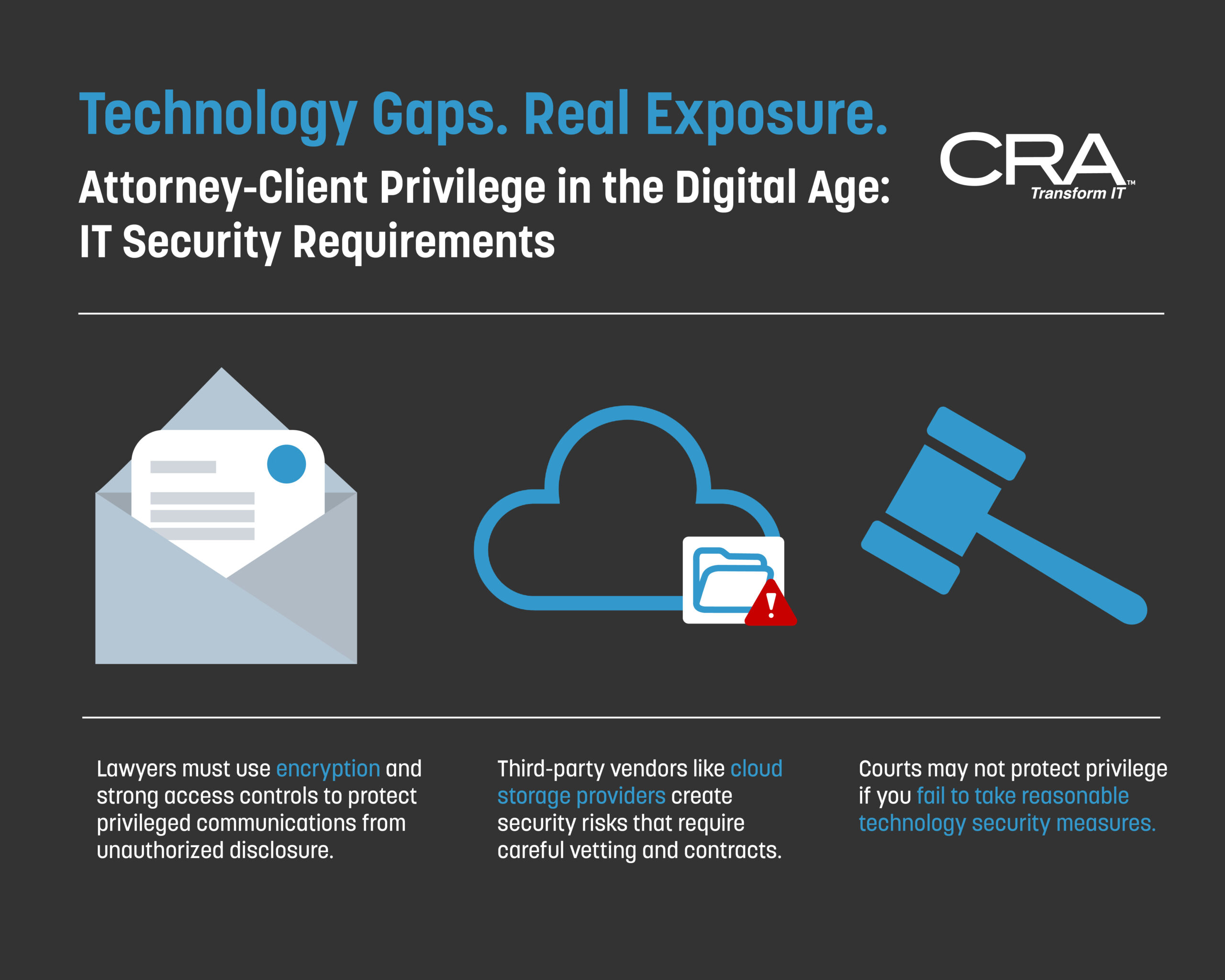
Attorney-Client Privilege IT Security: Modern Protection Strategies
Lawyers have always been required to protect client secrets, but technology has made this job much harder. Attorney client privilege IT security now requires specific technical measures like encryption, access controls, and secure communication systems to meet ethical standards. A single mistake with email, cloud storage, or mobile devices can expose confidential information and put…
Lawyers have always been required to protect client secrets, but technology has made this job much harder. Attorney client privilege IT security now requires specific technical measures like encryption, access controls, and secure communication systems to meet ethical standards. A single mistake with email, cloud storage, or mobile devices can expose confidential information and put…
Read full post on consultcra.comMSPdb™ News

Maryland Personal Information Protection Act (PIPA): What SMBs Must Do in 2026
Running a small or mid-size business in Maryland feels heavier in 2026. More rules. More audits. More emails about breaches you hope never happen to you. PIPA is one of those laws people heard about years ago but didn’t really act on. That’s changed now. Enforcement is tighter. Insurers are stricter. And one bad incident can spiral fast. This is where Managed IT Services in Maryland stop being a “nice to have” and become a basic survival necessity. Why PIPA Matters More in Maryland in 2026 Businesses in Maryland deal with lots of sensitive data: medical records, government files, and financial
Running a small or mid-size business in Maryland feels heavier in 2026. More rules. More audits. More emails about breaches you hope never happen to you. PIPA is one of those laws people heard about years ago but didn’t really act on. That’s changed now. Enforcement is tighter. Insurers are stricter. And one bad incident can spiral fast. This is where Managed IT Services in Maryland stop being a “nice to have” and become a basic survival necessity. Why PIPA Matters More in Maryland in 2026 Businesses in Maryland deal with lots of sensitive data: medical records, government files, and financial information. Even smaller firms touch personal data more than they realize. PIPA doesn’t care about your size. It cares about how you protect information. In 2026, the risk feels more real. Cyber insurance renewals now ask about controls. State audits look closer. Clients ask questions. If your answer is vague, that’s a problem. Managed IT Services in Maryland help fill those gaps without forcing you to hire a full internal team. For many SMBs, that’s the only realistic option. Local industries that feel this pressure most: If data lives on your systems, PIPA applies. Simple as that. Real Numbers SMBs Should Pay Attention To Here’s where things stop being abstract. These are real ranges Maryland SMBs are seeing. Businesses relying on casual IT support often miss these marks. That delay alone can trigger legal and financial trouble. IT support in Maryland that’s proactive, not reactive, changes that math. How Managed IT Services Support PIPA Compliance Step 1: Risk & Data Assessment A simple risk register and a compliance gap report. No fluff. Just facts. Step 2: Stabilization A stable, monitored setup that doesn’t fall apart under pressure. Step 3: Security Baseline Security controls that actually line up with PIPA rules. Step 4: Continuous Monitoring An ongoing compliance posture with managed IT services for Maryland compliance that holds up over time. No scrambling later. PIPA Compliance and Risk in 2026 PIPA expects reasonable security. That phrase sounds vague. In practice, it means documented controls, monitoring, and fast response. If something breaks, you must know. And act. Common issues seen in Maryland SMBs: Good IT support in Maryland doesn’t just fix laptops. It helps you show auditors and insurers that you took protection seriously. That paper trail matters more than people think. PIPA also overlaps with HIPAA and CMMC for many Maryland businesses. Managed services bundle these needs together, so you’re not paying three times for the same work. Maryland Infrastructure Realities Nobody Talks About Not every office has perfect internet. Or clean power. Or secure wiring. Older buildings across the state make things harder. Some common local challenges: Most managed IT Services in Maryland are designed around this. Dual internet lines. Cloud backups with local copies. Secure Wi-Fi segmentation. Nothing fancy. Just practical setups that work here. Cost Breakdown for Managed IT Services in Maryland Local providers tend to be clearer about pricing. Competition helps. Still worth asking direct questions. Managed vs Other IT Models: How Managed IT is Different from Other IT Models IT Model Cost Pattern Coverage Compliance Readiness Break/Fix IT Low upfront, spikes later Reactive only Weak or missing. No real structure In-House IT High salary and benefits Limited to one or two people Inconsistent. Burnout creates gaps Managed IT Services in Maryland Predictable monthly cost Broad team and tools Strong. Documented controls and audit support Maryland SMB Case Example A 15-person medical office outside Baltimore with a small team and a busy schedule. Problems showed up slowly. Old backups. No clear breach plan. Slow response from freelance IT. They moved to managed services. Cleaned up systems. Set up encrypted backups. Documented response steps. Six months later: Final Thoughts PIPA in 2026 is not theoretical anymore. Maryland SMBs are being judged on preparation, not intent. Managed IT Services in Maryland give structure to that chaos. Clear response times. Clear controls. Clear costs. IT support in Maryland that understands local rules, buildings, and industries makes compliance less painful. It’s still work, still effort, but with fewer headaches and surprises. FAQs
Read full post on gocorptech.com
The Rise of Business Email Compromise and How to Protect your Organization
A payment request hits an inbox, references a real project, and matches the tone your team expects from a vendor or executive. A controller approves it, funds leave your bank account forever, and no one is the wiser until much later. That pattern describes business email compromise (BEC), a type of fraud that uses impersonation
A payment request hits an inbox, references a real project, and matches the tone your team expects from a vendor or executive. A controller approves it, funds leave your bank account forever, and no one is the wiser until much later. That pattern describes business email compromise (BEC), a type of fraud that uses impersonation
Read full post on axxys.com
Navigating the AI Shift: Q&A with Net Friends CEO
Navigating the AI revolution is about building a foundation that lasts. At Net Friends, we view the AI landscape through three distinct layers: how we use it internally, how we guide our clients, and the bigger picture of where the technology is heading for small businesses.
Navigating the AI revolution is about building a foundation that lasts. At Net Friends, we view the AI landscape through three distinct layers: how we use it internally, how we guide our clients, and the bigger picture of where the technology is heading for small businesses.
Read full post on netfriends.com
The Governance Gap: Why Secure Scaling in Defense Tech Demands More Than Just Good IT
With the November 2026 CMMC 2.0 deadline only months away, many defense contractors are realizing good IT isn't enough to pass a C3PAO audit. If you aren't already remediating your NIST 800-171 gaps, your eligibility for new contract awards is at risk. Techvera breaks down the 4 critical governance hurdles you must clear to stay in the game.
With the November 2026 CMMC 2.0 deadline only months away, many defense contractors are realizing good IT isn't enough to pass a C3PAO audit. If you aren't already remediating your NIST 800-171 gaps, your eligibility for new contract awards is at risk. Techvera breaks down the 4 critical governance hurdles you must clear to stay in the game.
Read full post on techvera.com
7 Things Outsourced IT Support Should Actually Include
Most business leaders who start looking into outsourced IT support are picturing a help desk. Someone to call when a laptop stops working or a password needs resetting. A more affordable option than hiring a full-time technology person in-house. That picture is accurate for some providers. It is nowhere close to what a growing business
Most business leaders who start looking into outsourced IT support are picturing a help desk. Someone to call when a laptop stops working or a password needs resetting. A more affordable option than hiring a full-time technology person in-house. That picture is accurate for some providers. It is nowhere close to what a growing business
Read full post on stringfellow.com
AI Cybersecurity Threats: What You Need to Know (And How We Can Help)
Understanding the landscape of AI cybersecurity threats is the first step toward protecting the business that you've built.
Understanding the landscape of AI cybersecurity threats is the first step toward protecting the business that you've built.
Read full post on gocourant.com
Security Fatigue in 2026: The Workflow Fix That Protects Customers
Article summary: Security fatigue in 2026 turns everyday security prompts into background noise. Employees click through on autopilot, and customers feel the impact through delays, lockouts, and avoidable mistakes. The fix is to redesign the way of working by reducing repeated decisions, tightening sign-in flows, and strengthening baseline controls. Customers don’t see your MFA prompts,... Source
Article summary: Security fatigue in 2026 turns everyday security prompts into background noise. Employees click through on autopilot, and customers feel the impact through delays, lockouts, and avoidable mistakes. The fix is to redesign the way of working by reducing repeated decisions, tightening sign-in flows, and strengthening baseline controls. Customers don’t see your MFA prompts,... Source
Read full post on cloudavize.com
Calgary Business IT Solutions: Cybersecurity & Growth Support
Calgary Business IT Solutions: Cybersecurity & Growth Support | PCe Solutions PCe Solutions partners with Calgary businesses across every sector to deliver the cybersecurity protection and scalable IT infrastructure needed to grow confidently Calgary is a city with ambition. From the towers of the downtown core to the industrial parks of the northeast, from the...
Calgary Business IT Solutions: Cybersecurity & Growth Support | PCe Solutions PCe Solutions partners with Calgary businesses across every sector to deliver the cybersecurity protection and scalable IT infrastructure needed to grow confidently Calgary is a city with ambition. From the towers of the downtown core to the industrial parks of the northeast, from the...
Read full post on pcesolutions.ca
Why Google Drive Is Not a Real Backup for Salinas Businesses in 2026
Discover why Google Drive is not a real backup for your business. Learn the difference between syncing and true backup to protect your critical business data.
Discover why Google Drive is not a real backup for your business. Learn the difference between syncing and true backup to protect your critical business data.
Read full post on adaptiveis.net
Why Reliable IT Support Is Critical for Business Continuity
Technology plays a central role in keeping modern businesses running smoothly every day. From communication systems to data management, organizations depend heavily on stable and responsive IT infrastructure. Even a short disruption can impact productivity, customer service, and overall operations. Reliable technical support helps businesses respond quickly to issues and maintain consistent performance. In this
Technology plays a central role in keeping modern businesses running smoothly every day. From communication systems to data management, organizations depend heavily on stable and responsive IT infrastructure. Even a short disruption can impact productivity, customer service, and overall operations. Reliable technical support helps businesses respond quickly to issues and maintain consistent performance. In this
Read full post on integricom.net