MSPs are real, and their spectacular.
Discover leading Managed IT Service Providers across USA, Canada & the United Kingdom.
- 100s of leading MSPs
- Find a MSP near you
- Latest IT news for SMBs
7 Critical Microsoft 365 Security Strategies for IT Leaders
Microsoft 365 has become the backbone of productivity for organizations worldwide – and a prime target for cyberattacks. In fact, according to the Microsoft Digital Defense Report Microsoft’s cloud services are now the top phishing target, with attackers making 4,000 password compromise attempts per second against Microsoft cloud accounts. “The biggest piece I think Read More
Microsoft 365 has become the backbone of productivity for organizations worldwide – and a prime target for cyberattacks. In fact, according to the Microsoft Digital Defense Report Microsoft’s cloud services are now the top phishing target, with attackers making 4,000 password compromise attempts per second against Microsoft cloud accounts. “The biggest piece I think Read More
Read full post on wolfconsulting.comMSPdb™ News

Modern Microsoft 365 Governance for the AI Era: A Thrive Perspective
Strong governance has always served as the cornerstone of a secure, efficient, and well-managed digital workplace. Microsoft 365 has become the primary productivity platform for most organizations; however, without deliberate and effective governance, even robust…
Strong governance has always served as the cornerstone of a secure, efficient, and well-managed digital workplace. Microsoft 365 has become the primary productivity platform for most organizations; however, without deliberate and effective governance, even robust…
Read full post on thrivenextgen.com
9 Tips to Work Faster in Outlook and Teams
Boost workplace efficiency with practical tips for Outlook and Teams. Learn how to streamline communication, reduce distractions, and help your team stay organized and productive using tools you already rely on every day... continue reading
Boost workplace efficiency with practical tips for Outlook and Teams. Learn how to streamline communication, reduce distractions, and help your team stay organized and productive using tools you already rely on every day... continue reading
Read full post on dynedge.com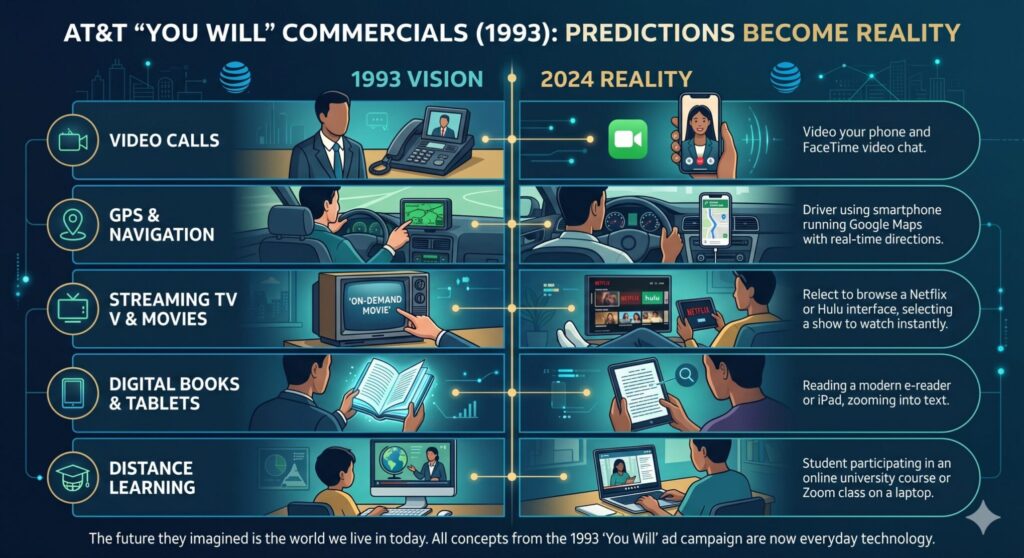
How AT&T’s 1993 Ads Saw the Future
The “You Will” Prophecies: How AT&T’s 1993 Ads Saw the Future In 1993, the internet was a novelty mostly relegated to academic and military institutions. Dial-up connections hummed with erratic screeches, and cell phones, if you had one, resembled actual bricks. Yet, in the midst of this early technological landscape, AT&T launched an advertising campaign
The “You Will” Prophecies: How AT&T’s 1993 Ads Saw the Future In 1993, the internet was a novelty mostly relegated to academic and military institutions. Dial-up connections hummed with erratic screeches, and cell phones, if you had one, resembled actual bricks. Yet, in the midst of this early technological landscape, AT&T launched an advertising campaign
Read full post on fuellednetworks.com
Instantly Speed Up Your Slow PC in 4 Easy Steps
When you think about it, the difference in speed between a new computer and one that’s just a few months old is staggering… and in the worst way. This slowdown happens simply because your computer collects information that it doesn’t need to retain. All this extra data metaphorically weighs your workstation down.Fortunately, there are a few different ways to get rid of this digital detritus and put the pep back in your productivity.
When you think about it, the difference in speed between a new computer and one that’s just a few months old is staggering… and in the worst way. This slowdown happens simply because your computer collects information that it doesn’t need to retain. All this extra data metaphorically weighs your workstation down.Fortunately, there are a few different ways to get rid of this digital detritus and put the pep back in your productivity.
Read full post on coretechllc.com
Find the Best IT Consulting Firms for Small Businesses
It consulting firms for small businesses - Discover the best it consulting firms for small businesses. Our guide helps Monterey Bay companies find, vet, & hire
It consulting firms for small businesses - Discover the best it consulting firms for small businesses. Our guide helps Monterey Bay companies find, vet, & hire
Read full post on adaptiveis.net
The Bigger Risk? Doing Nothing: Why Waiting on AI Could Cost You Clients
Think about a competitor in your space. Same size, same client base, similar service mix. They spent the last six months building an AI workflow their team actually uses every day. Not experimenting. Using. Meeting prep that takes ten minutes instead of an hour. Client briefings finished before lunch instead of the following morning. Senior
Think about a competitor in your space. Same size, same client base, similar service mix. They spent the last six months building an AI workflow their team actually uses every day. Not experimenting. Using. Meeting prep that takes ten minutes instead of an hour. Client briefings finished before lunch instead of the following morning. Senior
Read full post on midnightbluetech.com
What is Cloud Disaster Recovery? Unpack the Myths, Realities & Resilience
Stop Gambling on Backups—Why a Tested Cloud Disaster Recovery Plan Saves Your Business from the Unexpected You’ve probably heard, “We’ll just restore...
Stop Gambling on Backups—Why a Tested Cloud Disaster Recovery Plan Saves Your Business from the Unexpected You’ve probably heard, “We’ll just restore...
Read full post on turnkeysol.com
The “Cookie” Hijack: Why MFA Can’t Always Save You
MFA is a strong front-door lock. But it’s not the only thing that decides whether someone can get in. After you sign in, your browser keeps you logged in using a session token (often stored as a cookie). It’s the digital version of a wristband at an event: once you’ve been checked, the wristband proves
MFA is a strong front-door lock. But it’s not the only thing that decides whether someone can get in. After you sign in, your browser keeps you logged in using a session token (often stored as a cookie). It’s the digital version of a wristband at an event: once you’ve been checked, the wristband proves
Read full post on avenirit.com
Ransomware in 2026: What Portland Trades Need to Know | AlwaysOnIT
88% of ransomware attacks now hit small businesses. Learn why Portland trades and contractors are top targets — and the three controls that stop attacks.
88% of ransomware attacks now hit small businesses. Learn why Portland trades and contractors are top targets — and the three controls that stop attacks.
Read full post on alwaysonit.com
What’s New with Microsoft Copilot: 10 Key Features Your Team Should Know
Microsoft Copilot is becoming more useful inside the tools your team already uses every day. This blog breaks down 10 key features including Excel cleanup, agent-based analysis, Word drafting, PowerPoint creation, calendar scheduling, and inbox follow-up.
Microsoft Copilot is becoming more useful inside the tools your team already uses every day. This blog breaks down 10 key features including Excel cleanup, agent-based analysis, Word drafting, PowerPoint creation, calendar scheduling, and inbox follow-up.
Read full post on snaptechit.com