Search and you will find.
Discover leading Managed IT Service Providers across USA, Canada & the United Kingdom.
- 100s of leading MSPs
- Find a MSP near you
- Latest IT news for SMBs

Essential IT Security Policies Every Business Needs
A successful business is a secure business. You probably have a good lock on the front door, maybe an alarm system, and secure cabinets for important documents. You do all of this to protect your business' physical assets from threats. So why wouldn't you do the same for your digital assets?Just as you have physical security measures, your business also needs strong cybersecurity policies. They help create clear rules for employees to follow and a plan to fall back on if an incident occurs.Here are five essential security policies every business needs.Acceptable Use PolicyThis policy explains
A successful business is a secure business. You probably have a good lock on the front door, maybe an alarm system, and secure cabinets for important documents. You do all of this to protect your business' physical assets from threats. So why wouldn't you do the same for your digital assets?Just as you have physical security measures, your business also needs strong cybersecurity policies. They help create clear rules for employees to follow and a plan to fall back on if an incident occurs.Here are five essential security policies every business needs.Acceptable Use PolicyThis policy explains how employees can and can't use your company's technology. It should cover everything from hardware and networks to Internet access and software installation. Do you allow employees to use work devices for personal use, like social media? How do they request new software instead of downloading it on their own? This policy outlines all the procedures for these situations and more.Password PolicyEven with all the new security tools available, passwords are still a critical line of defense. A password policy ensures employees use strong, unique passwords. This policy should specify minimum length and complexity requirements and prohibit password reuse. You can also recommend or require the use of a password manager to make it easier for employees to create and store their passwords securely.Data Handling PolicyWhat kind of data does your business handle, and how sensitive is it? This policy classifies your data and establishes clear rules for how each type should be handled, from storage and accessibility to sharing. It helps your team understand what data can be saved and shared, and if so, how.Remote Access PolicyWith many companies embracing remote or hybrid work, a remote access policy is more important than ever. This policy tells your team how they should securely connect to the company network from other locations. It should require the use of a virtual private network (VPN) and prohibit accessing company data over public Wi-Fi.Incident Response PlanNo matter how prepared you are, a security incident can still happen. The worst thing you can do is panic, which is why an incident response plan is so important. This plan defines who to notify, how to contain the threat, and what to communicate to customers and employees. Having this plan in place before you need it can help you minimize the damage and recover quickly.Strengthen Your Business with the Right PoliciesSecurity policies aren't meant to restrict your employees; they're designed to protect your team and your company. By putting these safeguards in place, security becomes a clear, actionable strategy rather than a vague concept.Writing these policies can be a complicated task, but Argentum IT can help. We assist businesses with all kinds of IT needs, including designing effective security policies that protect your business while fitting its unique requirements. Give us a call today at (502) 473-6407.
Read full post on argentumit.comMSPdb™ News

IT Audit Checks: 6 Critical Midyear Reviews That Prevent Costly Business Disruptions
As businesses move through the second half of the year, many technology problems begin to surface. Not because systems suddenly fail, but because small issues were left unchecked for too long. That’s why midyear IT audit checks are one of the smartest preventative measures an organization can take. A midyear IT audit gives businesses the...
As businesses move through the second half of the year, many technology problems begin to surface. Not because systems suddenly fail, but because small issues were left unchecked for too long. That’s why midyear IT audit checks are one of the smartest preventative measures an organization can take. A midyear IT audit gives businesses the...
Read full post on fogosolutions.com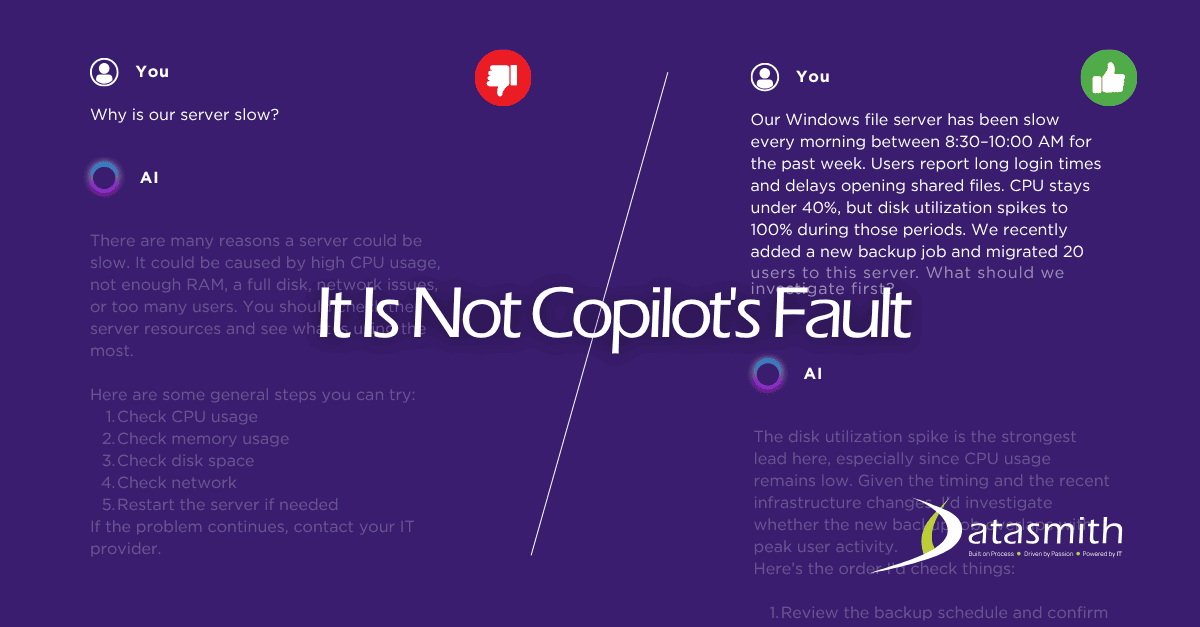
Is Microsoft Copilot a Good AI Tool for Small Businesses? An Honest Answer.
If your business runs on Microsoft 365 and you are wondering whether Copilot is worth your time, the short answer
If your business runs on Microsoft 365 and you are wondering whether Copilot is worth your time, the short answer
Read full post on datasmithnetworks.com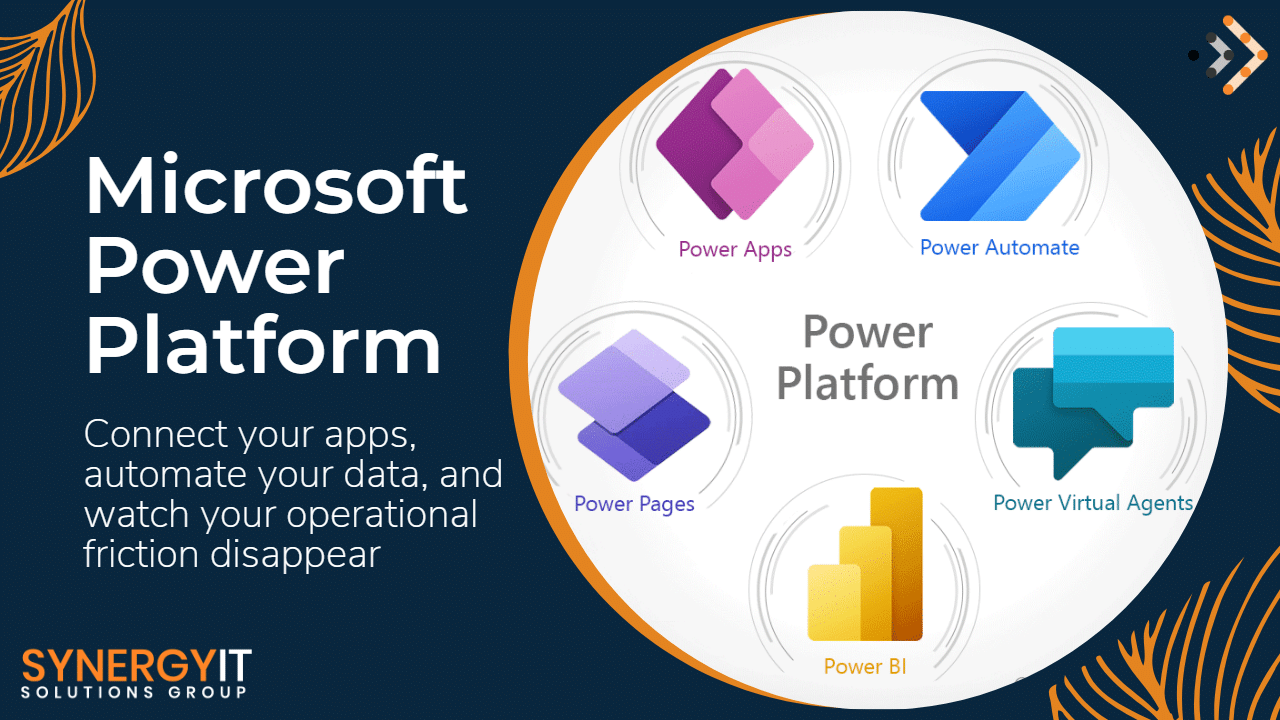
Automate Your Business with Power Automate: Save Time & Costs
Every business leader wants the same thing: more productivity, lower operational costs, and faster growth.…
Every business leader wants the same thing: more productivity, lower operational costs, and faster growth.…
Read full post on blog.synergyit.ca
AI Is Already in Your Business. Who’s Keeping It in Check?
AI probably did not enter your business through a formal rollout. It probably showed up in the tools your team already uses every day, like an AI button in email or another one in a Read More...
AI probably did not enter your business through a formal rollout. It probably showed up in the tools your team already uses every day, like an AI button in email or another one in a Read More...
Read full post on taznetworks.com
Smart Businesses: Top 5 Traits of Ideal IT Partners
In today’s fast-paced digital world, technology is the engine that drives your business forward. For many business owners, managing IT can be a major headache, pulling focus away from core operations. That’s why finding the right IT partner is more important than ever. The ideal partner does more than just fix problems; they provide strategic
In today’s fast-paced digital world, technology is the engine that drives your business forward. For many business owners, managing IT can be a major headache, pulling focus away from core operations. That’s why finding the right IT partner is more important than ever. The ideal partner does more than just fix problems; they provide strategic
Read full post on vcsolutions.com
Zero Trust in Action: Leveraging Microsoft Security Stack to Safeguard the Hybrid Enterprise
Discover how Zero Trust and Microsoft Security Stack safeguard hybrid enterprises from advanced cyber threats. Learn key strategies for 2026.
Discover how Zero Trust and Microsoft Security Stack safeguard hybrid enterprises from advanced cyber threats. Learn key strategies for 2026.
Read full post on trndigital.com
New SharePoint Sharing Rule: What Your Business Needs to Know Before July 2026
All those SharePoint files you’ve shared with clients, vendors or other partners outside your organization could be inaccessible in July 2026. Why? New SharePoint sharing rules start that month. The core change is occurring because Microsoft is moving away from link-based access to a more secure identity-based access model. Every external person you share files…
All those SharePoint files you’ve shared with clients, vendors or other partners outside your organization could be inaccessible in July 2026. Why? New SharePoint sharing rules start that month. The core change is occurring because Microsoft is moving away from link-based access to a more secure identity-based access model. Every external person you share files…
Read full post on skyterratech.com
Solving the “Slow Computer” Complaint: When to Upgrade vs. When to Replace
We’ve all been there. You are trying to meet a deadline, but you find yourself staring at a spinning wheel while a webpage takes forever to load. You close a few tabs and restart the machine, yet everything still crawls at a snail’s pace. A sluggish device quickly drains your productivity and your patience. When
We’ve all been there. You are trying to meet a deadline, but you find yourself staring at a spinning wheel while a webpage takes forever to load. You close a few tabs and restart the machine, yet everything still crawls at a snail’s pace. A sluggish device quickly drains your productivity and your patience. When
Read full post on totalit.com
Streamlining Your Vendors Helps Streamline Your Business
How many vendors and subscriptions does your business rely on to function day to day?Now, to ask a question that hopefully has (but very easily doesn’t have) the same answer: How many vendors and subscriptions does your business currently pay for?Unfortunately, for most small and medium-sized businesses, these answers can vary widely, which often creates confusion and leads to wasted capital. Let’s talk about a simple and reliable way to help align the answers to these two key questions: vendor management.
How many vendors and subscriptions does your business rely on to function day to day?Now, to ask a question that hopefully has (but very easily doesn’t have) the same answer: How many vendors and subscriptions does your business currently pay for?Unfortunately, for most small and medium-sized businesses, these answers can vary widely, which often creates confusion and leads to wasted capital. Let’s talk about a simple and reliable way to help align the answers to these two key questions: vendor management.
Read full post on coretechllc.com
MSSP for Healthcare: What HIPAA Requires from Your Security Partner
A managed security service provider for healthcare is a third-party organization that takes operational responsibility for the security controls a covered entity must maintain under the HIPAA Security Rule, including continuous monitoring, incident response, risk analysis support, and the documentation that OCR expects to see in an investigation. What separates a qualified healthcare MSSP from ... Read more
A managed security service provider for healthcare is a third-party organization that takes operational responsibility for the security controls a covered entity must maintain under the HIPAA Security Rule, including continuous monitoring, incident response, risk analysis support, and the documentation that OCR expects to see in an investigation. What separates a qualified healthcare MSSP from ... Read more
Read full post on meriplex.com