Search and you will find.
Discover leading Managed IT Service Providers across USA, Canada & the United Kingdom.
- 100s of leading MSPs
- Find a MSP near you
- Latest IT news for SMBs

The Key to Understanding How Bandwidth Works
The Internet is a staple in most offices around the world, and you’d be hard-pressed to find one that doesn’t rely on it in some fashion. A big part of seeing success with the Internet depends on your bandwidth, as well as your network’s capacity to reach the capabilities of your Internet service provider. Today, we want to break down what bandwidth is, as well as how you can make the most of your Internet package.What Is Bandwidth?Bandwidth measures how much volume of information per unit of time that your network can transmit. The more bandwidth you have, the faster your connection, which me
The Internet is a staple in most offices around the world, and you’d be hard-pressed to find one that doesn’t rely on it in some fashion. A big part of seeing success with the Internet depends on your bandwidth, as well as your network’s capacity to reach the capabilities of your Internet service provider. Today, we want to break down what bandwidth is, as well as how you can make the most of your Internet package.What Is Bandwidth?Bandwidth measures how much volume of information per unit of time that your network can transmit. The more bandwidth you have, the faster your connection, which means more data can be transferred. Bandwidth is measured in seconds, so you might see some ISPs use language like megabits per second (Mbps or Mb/s).An important distinction to make, however, is that Megabytes, or MB, does not measure bandwidth. If you see a connection advertised as 15 MB/s, that number is actually much lower (1.875 Mbps), since there are only eight bits in a byte. If all that sounds confusing, that’s because it is, and suffice to say that you should always look for the Mbps of an advertised connection rather than MB if you can find it.The good news: most ISPs will advertise their Internet packages at a megabit value. Even still, this isn’t a reliable way to know how much bandwidth you can expect from your connection, as there are several factors that can contribute to how much actual bandwidth you have—variables like your physical location, the location of your ISP’s data centers, your networking hardware and whether you’re on a wired or wireless connection, etc. To see how fast your connection is, you’ll need to use a speed tester; there are plenty on the Internet, including one built right into Google, but we like to recommend the one at speedtest.net.A Practical Explanation of BandwidthBandwidth can be compared to plumbing in a lot of ways. Think of your data as water flowing through a pipe. It can only send so much at a time. If you want to send more water through, you’ll need a bigger pipe so more water can pass through at once.Most users who only take advantage of simple applications and a web browser probably don’t need too much bandwidth, but bandwidth can get dicey when you add in streaming media or accessing resource-intensive cloud-based resources. Especially for SMBs, you might find that a lower bandwidth is just not cutting it, and that’s to be expected. We always recommend that you look into enterprise-grade bandwidth options whenever possible so your options aren’t so limited.If your bandwidth is already high enough as is, and you want to upgrade the speed of your network, you have a couple of options available. You might look into purchasing a new router, changing the location of that router, switching from a wireless connection to a wired connection, and so on. Keep in mind there is only so much blood you can squeeze from this stone, and in many cases, you’ll have to upgrade with your ISP (or find a different provider) to increase your network speeds.If your business needs to make adjustments to its network, bandwidth, or networking hardware, you can count on Argentum IT to provide the necessary expertise and support. Learn more by calling us today at (502) 473-6407.
Read full post on argentumit.comMSPdb™ News

IT Audit Checks: 6 Critical Midyear Reviews That Prevent Costly Business Disruptions
As businesses move through the second half of the year, many technology problems begin to surface. Not because systems suddenly fail, but because small issues were left unchecked for too long. That’s why midyear IT audit checks are one of the smartest preventative measures an organization can take. A midyear IT audit gives businesses the...
As businesses move through the second half of the year, many technology problems begin to surface. Not because systems suddenly fail, but because small issues were left unchecked for too long. That’s why midyear IT audit checks are one of the smartest preventative measures an organization can take. A midyear IT audit gives businesses the...
Read full post on fogosolutions.com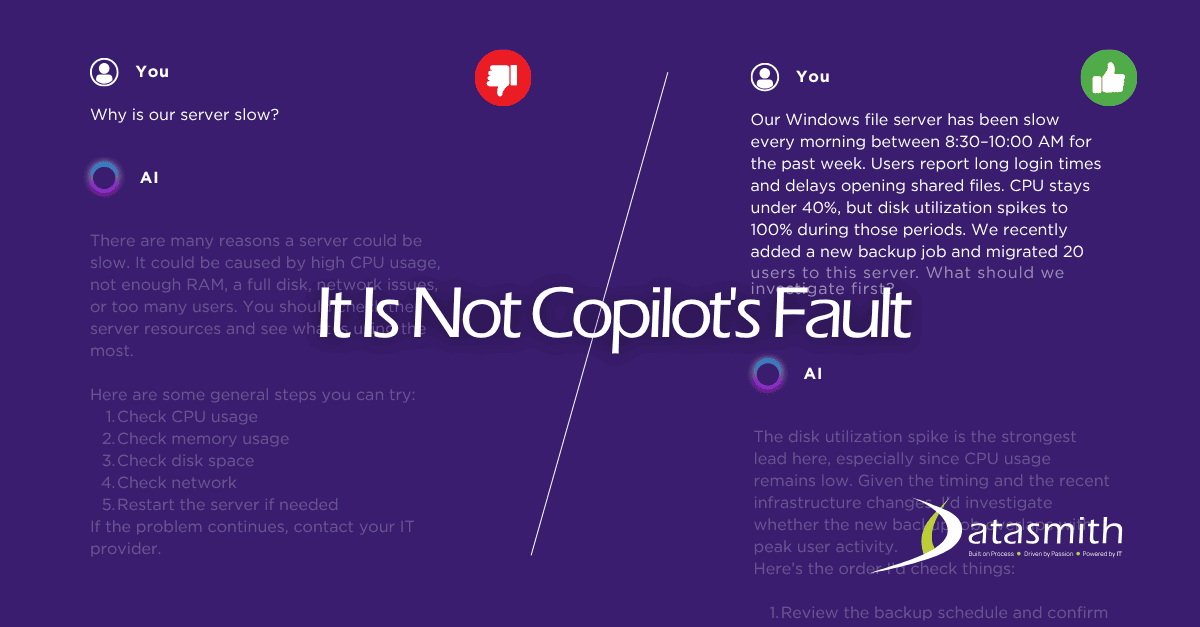
Is Microsoft Copilot a Good AI Tool for Small Businesses? An Honest Answer.
If your business runs on Microsoft 365 and you are wondering whether Copilot is worth your time, the short answer
If your business runs on Microsoft 365 and you are wondering whether Copilot is worth your time, the short answer
Read full post on datasmithnetworks.com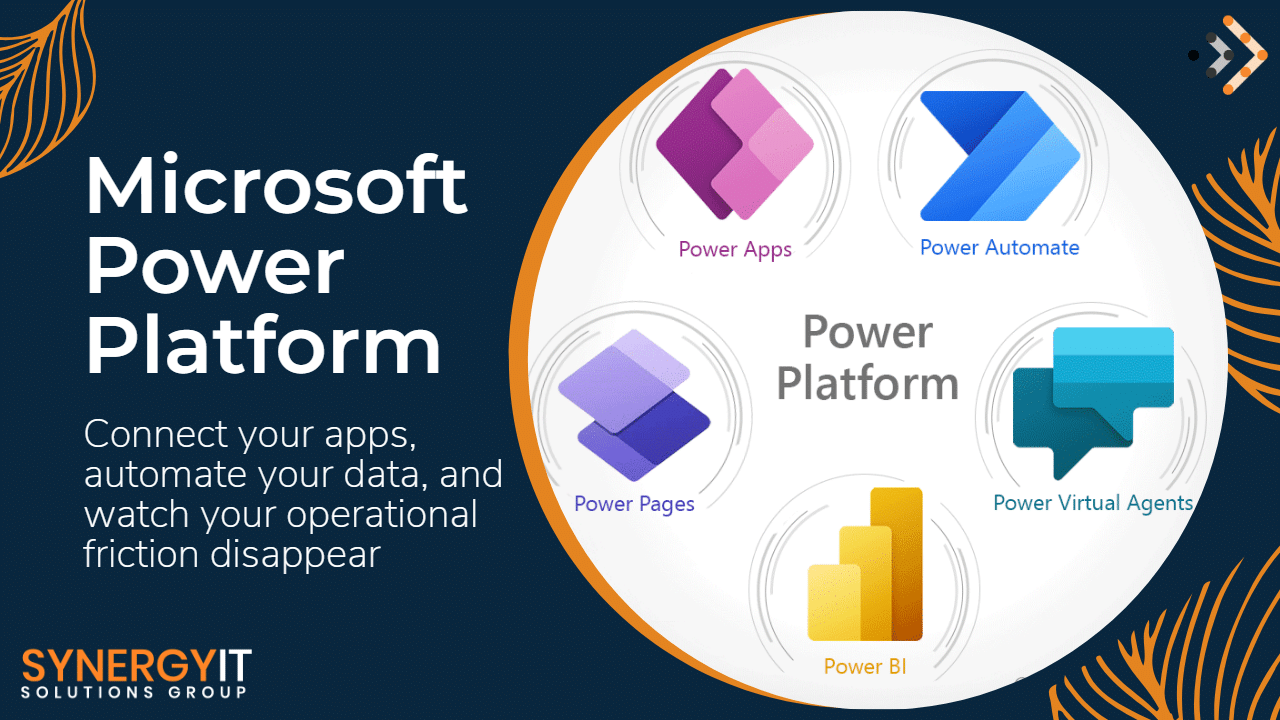
Automate Your Business with Power Automate: Save Time & Costs
Every business leader wants the same thing: more productivity, lower operational costs, and faster growth.…
Every business leader wants the same thing: more productivity, lower operational costs, and faster growth.…
Read full post on blog.synergyit.ca
AI Is Already in Your Business. Who’s Keeping It in Check?
AI probably did not enter your business through a formal rollout. It probably showed up in the tools your team already uses every day, like an AI button in email or another one in a Read More...
AI probably did not enter your business through a formal rollout. It probably showed up in the tools your team already uses every day, like an AI button in email or another one in a Read More...
Read full post on taznetworks.com
Smart Businesses: Top 5 Traits of Ideal IT Partners
In today’s fast-paced digital world, technology is the engine that drives your business forward. For many business owners, managing IT can be a major headache, pulling focus away from core operations. That’s why finding the right IT partner is more important than ever. The ideal partner does more than just fix problems; they provide strategic
In today’s fast-paced digital world, technology is the engine that drives your business forward. For many business owners, managing IT can be a major headache, pulling focus away from core operations. That’s why finding the right IT partner is more important than ever. The ideal partner does more than just fix problems; they provide strategic
Read full post on vcsolutions.com
Zero Trust in Action: Leveraging Microsoft Security Stack to Safeguard the Hybrid Enterprise
Discover how Zero Trust and Microsoft Security Stack safeguard hybrid enterprises from advanced cyber threats. Learn key strategies for 2026.
Discover how Zero Trust and Microsoft Security Stack safeguard hybrid enterprises from advanced cyber threats. Learn key strategies for 2026.
Read full post on trndigital.com
New SharePoint Sharing Rule: What Your Business Needs to Know Before July 2026
All those SharePoint files you’ve shared with clients, vendors or other partners outside your organization could be inaccessible in July 2026. Why? New SharePoint sharing rules start that month. The core change is occurring because Microsoft is moving away from link-based access to a more secure identity-based access model. Every external person you share files…
All those SharePoint files you’ve shared with clients, vendors or other partners outside your organization could be inaccessible in July 2026. Why? New SharePoint sharing rules start that month. The core change is occurring because Microsoft is moving away from link-based access to a more secure identity-based access model. Every external person you share files…
Read full post on skyterratech.com
Solving the “Slow Computer” Complaint: When to Upgrade vs. When to Replace
We’ve all been there. You are trying to meet a deadline, but you find yourself staring at a spinning wheel while a webpage takes forever to load. You close a few tabs and restart the machine, yet everything still crawls at a snail’s pace. A sluggish device quickly drains your productivity and your patience. When
We’ve all been there. You are trying to meet a deadline, but you find yourself staring at a spinning wheel while a webpage takes forever to load. You close a few tabs and restart the machine, yet everything still crawls at a snail’s pace. A sluggish device quickly drains your productivity and your patience. When
Read full post on totalit.com
Streamlining Your Vendors Helps Streamline Your Business
How many vendors and subscriptions does your business rely on to function day to day?Now, to ask a question that hopefully has (but very easily doesn’t have) the same answer: How many vendors and subscriptions does your business currently pay for?Unfortunately, for most small and medium-sized businesses, these answers can vary widely, which often creates confusion and leads to wasted capital. Let’s talk about a simple and reliable way to help align the answers to these two key questions: vendor management.
How many vendors and subscriptions does your business rely on to function day to day?Now, to ask a question that hopefully has (but very easily doesn’t have) the same answer: How many vendors and subscriptions does your business currently pay for?Unfortunately, for most small and medium-sized businesses, these answers can vary widely, which often creates confusion and leads to wasted capital. Let’s talk about a simple and reliable way to help align the answers to these two key questions: vendor management.
Read full post on coretechllc.com
MSSP for Healthcare: What HIPAA Requires from Your Security Partner
A managed security service provider for healthcare is a third-party organization that takes operational responsibility for the security controls a covered entity must maintain under the HIPAA Security Rule, including continuous monitoring, incident response, risk analysis support, and the documentation that OCR expects to see in an investigation. What separates a qualified healthcare MSSP from ... Read more
A managed security service provider for healthcare is a third-party organization that takes operational responsibility for the security controls a covered entity must maintain under the HIPAA Security Rule, including continuous monitoring, incident response, risk analysis support, and the documentation that OCR expects to see in an investigation. What separates a qualified healthcare MSSP from ... Read more
Read full post on meriplex.com