Compliance updates for CMMC, HIPAA, PCI DSS, SOC 2, and NIST-driven security programs.

The Role of Vision in Your Compliance-as-a-Service Strategy
Navigating the world of regulatory compliance can feel overwhelming. The rules are constantly changing, and keeping up requires significant time and resources. This is where a solid compliance management strategy becomes essential. By proactively handling tasks like risk assessment and ensuring you meet all requirements, you can protect your business from hefty fines and reputational
Navigating the world of regulatory compliance can feel overwhelming. The rules are constantly changing, and keeping up requires significant time and resources. This is where a solid compliance management strategy becomes essential. By proactively handling tasks like risk assessment and ensuring you meet all requirements, you can protect your business from hefty fines and reputational
Read full post on vcsolutions.com
What CMMC 2.0 Changes for Your Cybersecurity Compliance
The Cybersecurity Maturity Model Certification (CMMC) program began a new program in November 2025 that will shift the burden of attestation and place stricter requirements on government contractors and subcontractors. The existing framework establishes a uniform cybersecurity standard for businesses that handle Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) under contracts with the …
The Cybersecurity Maturity Model Certification (CMMC) program began a new program in November 2025 that will shift the burden of attestation and place stricter requirements on government contractors and subcontractors. The existing framework establishes a uniform cybersecurity standard for businesses that handle Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) under contracts with the …
Read full post on swktech.com
BLACK BOTTLE IT ACHIEVES SOC 2 CERTIFICATION

2026 AI Governance: A Leadership Guide to Creating an Acceptable Use Policy
2026 AI Governance: A Leadership Guide to Creating an Acceptable Use Policy The era of unchecked artificial intelligence experimentation is coming to a close. As we move into 2026, organizations are shifting from casual AI use to formal enterprise standardization. To remain competitive and secure, leadership must establish a clear framework for how these tools
2026 AI Governance: A Leadership Guide to Creating an Acceptable Use Policy The era of unchecked artificial intelligence experimentation is coming to a close. As we move into 2026, organizations are shifting from casual AI use to formal enterprise standardization. To remain competitive and secure, leadership must establish a clear framework for how these tools
Read full post on appliedtech.us
Vendor Risk Management in Financial Services: Why CFOs Must Rethink Third-Party Exposure
Most financial services firms understand their internal controls well. However, fewer have the same visibility into their vendors. Today, that gap is widening fast. Vendor risk management has become a core financial discipline. CFOs can no longer treat third-party exposure as a back-office concern. Every vendor relationship now carries operational, regulatory, and financial weight. The
Most financial services firms understand their internal controls well. However, fewer have the same visibility into their vendors. Today, that gap is widening fast. Vendor risk management has become a core financial discipline. CFOs can no longer treat third-party exposure as a back-office concern. Every vendor relationship now carries operational, regulatory, and financial weight. The
Read full post on coretelligent.com
How to Prepare for Evolving Data Privacy Regulations in the U.S.
Companies can face serious financial, legal, and reputational penalties for failing to comply with data privacy regulations. Data breaches involving private personal information may result in large fines imposed by regulatory entities such as the Office for Civil Rights (OCR), which enforces HIPAA. Businesses may also be forced to address lawsuits initiated by individuals whose
Companies can face serious financial, legal, and reputational penalties for failing to comply with data privacy regulations. Data breaches involving private personal information may result in large fines imposed by regulatory entities such as the Office for Civil Rights (OCR), which enforces HIPAA. Businesses may also be forced to address lawsuits initiated by individuals whose
Read full post on vastitservices.com
Cybersecurity Compliance in Financial Services: Where Priorities Are Shifting
Cyber risk, vendor dependencies, AI use, and evolving supervisory expectations are changing how financial services firms approach compliance. Here’s how you should prioritize them. Why Priorities Are Shifting Financial services firms are operating in a more connected environment than they were just a few years ago. Core systems rely on vendors, employees use cloud-based platforms
Cyber risk, vendor dependencies, AI use, and evolving supervisory expectations are changing how financial services firms approach compliance. Here’s how you should prioritize them. Why Priorities Are Shifting Financial services firms are operating in a more connected environment than they were just a few years ago. Core systems rely on vendors, employees use cloud-based platforms
Read full post on coretelligent.com
Why HIPAA compliance costs rise and how to control them.
As healthcare technology expands and data privacy expectations evolve, the cost of supporting and maintaining HIPAA compliance has risen across the industry. From upgraded systems to labor-intensive audits, organizations are investing more to keep pace with enforcement activity, digital transformation, and vendor oversight. Understanding why HIPAA support costs increase, and how to control them strategically,
As healthcare technology expands and data privacy expectations evolve, the cost of supporting and maintaining HIPAA compliance has risen across the industry. From upgraded systems to labor-intensive audits, organizations are investing more to keep pace with enforcement activity, digital transformation, and vendor oversight. Understanding why HIPAA support costs increase, and how to control them strategically,
Read full post on magna5.com
Managed IT Services in New Mexico for Law Firms in Albuquerque: Secure eDiscovery, Data Retention, and Compliance
Law firms in Albuquerque deal with the pressure of deadlines, clients, courts, and files that cannot be lost. One small IT issue can turn into a real legal problem of emails stopping, case files not opening, or a system update breaking something important. That’s why more firms are moving toward Managed IT Services in New Mexico that are built for legal work. Not generic office setups. Real support for eDiscovery, data retention, and security. The kind that understands how law firms actually work. Quick Summary Local Context: Why Albuquerque Law Firms Have Unique IT Risks Law firms in New Mexi
Law firms in Albuquerque deal with the pressure of deadlines, clients, courts, and files that cannot be lost. One small IT issue can turn into a real legal problem of emails stopping, case files not opening, or a system update breaking something important. That’s why more firms are moving toward Managed IT Services in New Mexico that are built for legal work. Not generic office setups. Real support for eDiscovery, data retention, and security. The kind that understands how law firms actually work. Quick Summary Local Context: Why Albuquerque Law Firms Have Unique IT Risks Law firms in New Mexico don’t work in a perfect setup. Even in Albuquerque, things can be uneven. Older buildings. Mixed internet quality. Power issues once in a while. Outside the city, it gets worse. Many firms serve clients across the state. That means remote access matters. Court filings from home. Secure file sharing. Video calls that don’t drop. Common local issues include: This is where Managed IT Services in New Mexico have to be realistic. Systems must keep working even when the environment is not ideal. Data and Benchmarks for Law Firm IT Measured benchmarks help law firms understand what “good IT” actually means. Here’s what shows up often in Albuquerque law firms: Firms using proactive IT services in Albuquerque usually see fewer system failures. Less panic. Less late-night fixes. How Managed IT Services Work for Law Firms Good Managed IT Services in New Mexico follow a clear, step-by-step process. No confusion. No tech talk overload. Just solving problems in the right order so law firms can work without constant interruptions. 1. Assessment (Week 1) This phase is about understanding the current setup and risks. They review: Nothing fancy here. Just identifying what’s broken, outdated, or risky. 2. Stabilization (Weeks 2–3) Next comes cleanup and fixing the obvious issues: This step alone reduces stress for staff and cuts down daily tech issues. 3. Security Baseline (Weeks 3–4) Core protections are put in place: For law firms, this step is critical, not optional. 4. Ongoing Monitoring After setup, systems are continuously supported: This is where consistent IT support in New Mexico delivers long-term stability. Compliance and Legal Risk in New Mexico Law firms don’t just worry about clients. They worry about rules. In New Mexico, that includes: Most compliance problems come from small gaps. Old email systems. No clear data retention policy. Staff using personal devices. Reliable IT support in Albuquerque helps close those gaps before they turn into bigger issues. Infrastructure Challenges Law Firms Face in Albuquerque Offices Not every law office is modern. Some are in buildings that were never designed for today’s tech. That creates problems. Practical setups often include: Providers offering Managed IT Services in New Mexico usually design systems with failure in mind. Cost Breakdown: What Law Firms Actually Pay Costs are one of the first questions firms ask. Monthly Managed IT Pricing Pricing depends on risk, not just size. One-Time Costs Hidden Cost Drivers Honest IT services in Albuquerque will talk about these early. Comparison: Choosing the Right IT Model Break/Fix In-House IT Managed IT Services For most firms, Managed IT Services in New Mexico sits in the middle. Not cheap, but stable. Case Example: Albuquerque Litigation Firm A mid-size litigation firm in Albuquerque, with 12 attorneys, was dealing with repeated email outages and backup systems that looked fine but weren’t actually working. The real problem showed up during an active case, when key files couldn’t be found. At that point, the risk was already high, and the pressure was on. The firm moved to managed services with secure backups, continuous monitoring, and proper eDiscovery support. Within 90 days, downtime stopped catching them off guard. Document searches became faster and more reliable. A full security review was completed with no findings. Results like this are common with dependable IT support in Albuquerque. Conversion Block: Is Your Firm at Risk? A simple local IT check can show issues fast. Typical review includes: Many firms start their move to Managed IT Services in New Mexico with a small audit like this. Final Thought Law firms don’t need flashy tech. They need systems that work every day quietly and securely. With the right Managed IT Services in New Mexico, Albuquerque firms reduce risk and focus on cases instead of crashes. FAQs 1. How much do managed IT services cost for law firms? Most Albuquerque firms pay between $125 and $185 per user each month. 2. What response time should law firms expect? Remote response in under 30 minutes is standard. On-site within 2–4 hours locally. 3. Do law firms still need on-site IT visits? Yes. Hardware failures, network issues, and audits still require physical support. 4. Can managed IT help with compliance? Yes. Providers help align systems with New Mexico breach laws and HIPAA, where applicable. 5. What services are typically included in Managed IT for law firms? Services like monitoring, backups, security, eDiscovery support, user helpdesk, and reporting are included.
Read full post on gocorptech.com
Security Compliance is Mandatory for Cyber Insurance
The digital makeup of almost every business has shifted significantly over the past couple of years. Cyber insurance was once an optional add-on; in 2026, it is a requirement for corporate governance. It is no longer a simple transaction where you pay a premium and transfer your risk.
The digital makeup of almost every business has shifted significantly over the past couple of years. Cyber insurance was once an optional add-on; in 2026, it is a requirement for corporate governance. It is no longer a simple transaction where you pay a premium and transfer your risk.
Read full post on coretechllc.com
Shadow AI: Adoption Outpaces Policy and Governance
More than half of small businesses in the United States are now actively using generative AI tools, according to the U.S. Chamber of Commerce’s 2025 data. That number is accelerating. What is not accelerating at the same rate is policy. CybSafe and the National Cybersecurity Alliance found in late 2025 that 58 percent of employees…
More than half of small businesses in the United States are now actively using generative AI tools, according to the U.S. Chamber of Commerce’s 2025 data. That number is accelerating. What is not accelerating at the same rate is policy. CybSafe and the National Cybersecurity Alliance found in late 2025 that 58 percent of employees…
Read full post on intrust-it.com
McGraw Hill Data Breach: What This Cyberattack Teaches Businesses About Third-Party Risk
When a big education company like McGraw Hill gets hit with a data breach tied to an extortion attempt, it’s more than just another headline. It’s a wake up call on how cyber threats are evolving. According to Bleeping Computer, attackers got into sensitive data through a third-party vendor and then tried to extort the
When a big education company like McGraw Hill gets hit with a data breach tied to an extortion attempt, it’s more than just another headline. It’s a wake up call on how cyber threats are evolving. According to Bleeping Computer, attackers got into sensitive data through a third-party vendor and then tried to extort the
Read full post on enitechsolutions.com
The Audit Readiness Problem Government Contractors Can’t Afford to Ignore
Many government contractors are not failing audits because they lack tools. They are failing because documentation is incomplete, evidence is disorganized, and readiness starts too late. This blog explains the most common gaps and how to fix them before an audit begins.
Many government contractors are not failing audits because they lack tools. They are failing because documentation is incomplete, evidence is disorganized, and readiness starts too late. This blog explains the most common gaps and how to fix them before an audit begins.
Read full post on v2systems.com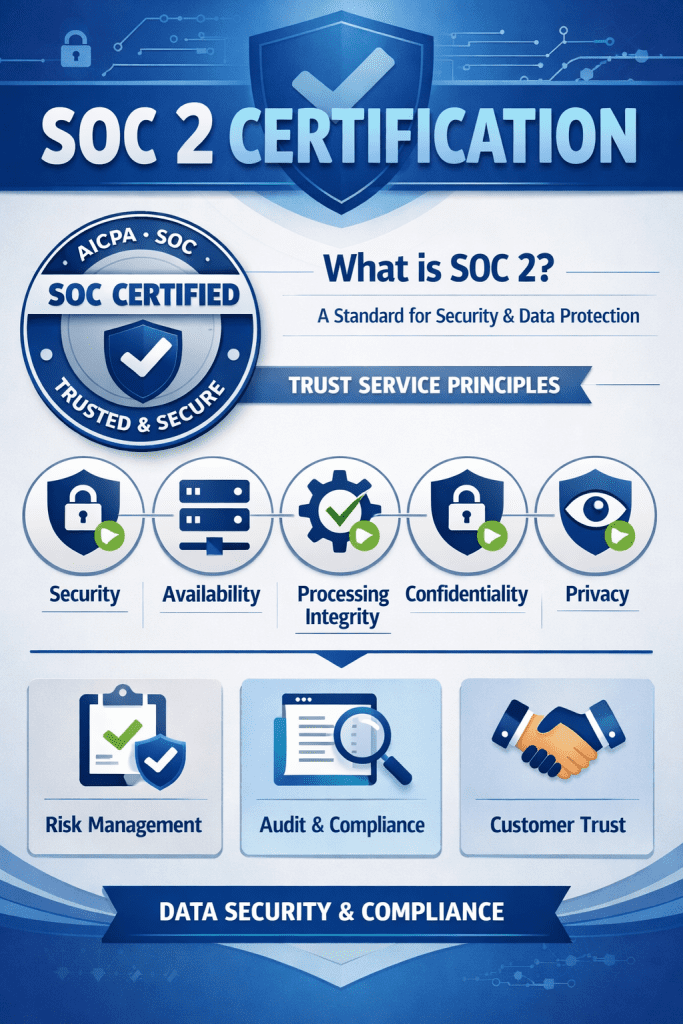
SOC 2 Compliance in Canada
Last Updated on April 10, 2026 by Matthew Goodchild SOC 2 Compliance in Canada: Type 1 vs Type 2, Certification & Checklist | CG Technologies Cybersecurity & Compliance SOC 2 Compliance in Canada: Type 1 vs Type 2, Certification & Checklist What Ontario businesses need to know before starting — and what CG Technologies can
Last Updated on April 10, 2026 by Matthew Goodchild SOC 2 Compliance in Canada: Type 1 vs Type 2, Certification & Checklist | CG Technologies Cybersecurity & Compliance SOC 2 Compliance in Canada: Type 1 vs Type 2, Certification & Checklist What Ontario businesses need to know before starting — and what CG Technologies can
Read full post on cgtechnologies.com
Compliance Checklist: PCI, HIPAA, and ISO
Navigate PCI, HIPAA, and ISO compliance requirements efficiently. See how Northeast Ohio businesses maintain multiple compliance frameworks, without chaos. In This Article: Your compliance requirements keep you awake at night. There’s PCI if you process payments, HIPAA if you handle health data, and ISO if you serve certain industries or clients. Each framework has different
Navigate PCI, HIPAA, and ISO compliance requirements efficiently. See how Northeast Ohio businesses maintain multiple compliance frameworks, without chaos. In This Article: Your compliance requirements keep you awake at night. There’s PCI if you process payments, HIPAA if you handle health data, and ISO if you serve certain industries or clients. Each framework has different
Read full post on infinit.us
CIS Controls v8.1 for Small Business: How Canadian SMBs Can Build a Real Cybersecurity Program (2026)
CIS Controls v8.1 for Small Business: How Canadian SMBs Can Build a Real Cybersecurity Program (2026) Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping Canadian businesses build and manage secure IT infrastructure since 2012 across Toronto, Hamilton, and Metro Vancouver. Forty-three percent of Canadian organizations were hit by a cyberattack in the
CIS Controls v8.1 for Small Business: How Canadian SMBs Can Build a Real Cybersecurity Program (2026) Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping Canadian businesses build and manage secure IT infrastructure since 2012 across Toronto, Hamilton, and Metro Vancouver. Forty-three percent of Canadian organizations were hit by a cyberattack in the
Read full post on fusioncomputing.ca
Financial Services Cybersecurity Compliance Guide | All Covered
Financial services cybersecurity is essential for protecting sensitive financial data, maintaining regulatory compliance, and preserving client trust. As financial firms expand digital banking platforms, trading systems, payment networks, and cloud environments, cyber risk increases across every layer of infrastructure.Financial institutions operate in one of the most heavily regulated and targeted industries. Improving cybersecurity compliance requires a structured, proactive approach that aligns security controls with evolving regulatory requirements.
Financial services cybersecurity is essential for protecting sensitive financial data, maintaining regulatory compliance, and preserving client trust. As financial firms expand digital banking platforms, trading systems, payment networks, and cloud environments, cyber risk increases across every layer of infrastructure.Financial institutions operate in one of the most heavily regulated and targeted industries. Improving cybersecurity compliance requires a structured, proactive approach that aligns security controls with evolving regulatory requirements.
Read full post on allcovered.com
Sagiss Achieves MSP Cyber Verify Certification and SOC 2 Type II Report, Continuing a Commitment to Security Since 2017
Security, compliance, and trust are foundational to every technology partnership. Sagiss is proud to announce the successful completion of its latest MSP Cyber Verify and SOC 2 Type II audits and certifications. This milestone reflects an ongoing commitment to protecting client operations through proven processes and independent validation.
Security, compliance, and trust are foundational to every technology partnership. Sagiss is proud to announce the successful completion of its latest MSP Cyber Verify and SOC 2 Type II audits and certifications. This milestone reflects an ongoing commitment to protecting client operations through proven processes and independent validation.
Read full post on sagiss.com
ITAR + NIST 800-171 for Maryland Manufacturers and Government Contractors
Running a regulated business in Maryland adds pressure you don’t always notice right away. It builds slowly. More rules. More systems. More expectations around how data is handled. Most companies don’t ignore compliance. They grow. They add tools. They move files to the cloud. Over time, the setup drifts. Then an audit request shows up, and gaps become obvious. That’s usually when Managed IT Services in Maryland stop feeling optional and start feeling necessary. This is the baseline most Managed IT Services in Maryland providers work from. Why compliance feels heavier in Maryland Maryland isn’
Running a regulated business in Maryland adds pressure you don’t always notice right away. It builds slowly. More rules. More systems. More expectations around how data is handled. Most companies don’t ignore compliance. They grow. They add tools. They move files to the cloud. Over time, the setup drifts. Then an audit request shows up, and gaps become obvious. That’s usually when Managed IT Services in Maryland stop feeling optional and start feeling necessary. This is the baseline most Managed IT Services in Maryland providers work from. Why compliance feels heavier in Maryland Maryland isn’t forgiving when it comes to regulated work. Too many federal agencies. Too many prime contractors. Too many eyes watching. If your business touches defense drawings, technical data, or controlled files, ITAR is already in your world. If you handle CUI for a federal contract, NIST 800-171 is not a suggestion. It’s expected. A lot of businesses still rely on basic IT support in Maryland. Someone to reset passwords. Someone to fix the email. That approach doesn’t survive audits. This is why many teams quietly move toward Top Managed IT Services in Maryland after their first close call. Why ITAR and NIST 800-171 Matter in Maryland Maryland is not an easy state for compliance. With places like Aberdeen Proving Ground, Fort Meade, and heavy federal supply chains tied to the National Security Agency, a lot of local companies handle sensitive data without even realizing how exposed they are. ITAR controls where data lives, who can access it, and even who can see it. One wrong cloud tool. One overseas backup. One shared login. That’s enough to cause serious trouble. NIST 800-171 is more detailed. Around 110 controls. Access rules, logging, encryption, incident response, and documentation. The stuff nobody enjoys maintaining. This is where Managed IT Services in Maryland stop being about convenience. They become about staying in business. One missed control. One badly set cloud tool. That can lead to audits, lost contracts, or worse. Maryland-Specific Compliance Realities Maryland companies deal with a tight mix of pressure points: Businesses relying on casual IT support in Maryland often miss how closely these rules overlap. ITAR violations are federal problems. NIST failures shut doors quietly. Both hit harder here than most states. Data, Costs, and Benchmarks (Local Ranges) No ranges pulled out of thin air. These show up often. Monthly managed IT costs Downtime reality Response benchmarks These numbers explain why businesses commit to Managed IT Services in Maryland even when budgets feel tight. How managed IT for compliance usually works The process is more direct than most expect. 1. Assessment 2. Stabilization 3. Security Baseline 4. Continuous Monitoring This structure separates real Managed IT Services in Maryland from basic IT support in Maryland. Common compliance gaps seen in Maryland audits These come up again and again. Maryland also has strict breach notification laws. Add HIPAA for mixed environments. Add CMMC pressure from primes. It piles up fast. Most IT support in Baltimore doesn’t track all of this unless asked. By then, it’s late. Infrastructure Realities in Maryland Facilities Not every risk is digital. Older industrial buildings struggle with power stability. Shared offices complicate physical access rules. Some industrial zones don’t have strong ISP redundancy. Local Managed IT Services in Maryland plan for this. Battery backups. Failover internet. Physical access controls. Small things that matter during audits. Cost Breakdown: What You Actually Pay Monthly pricing One-time costs Costs worth asking about Clear providers explain this early. Unclear ones don’t. Managed IT vs other choices IT Model What It Looks Like Real Impact Break/Fix IT Cheap at the start. You pay only when something breaks. Costs spike later. High risk. No audit readiness. Problems show up at the worst time. In-House IT One or two internal staff members handling everything. Security skills are hard to hire. Burnout is common. Coverage gaps happen fast. Managed IT Ongoing support, security, and monitoring under one plan. Predictable costs. Documentation ready. Someone answers during audits. Baltimore Defense Manufacturer: A Compliance Success Story A small defense manufacturer near Baltimore failed a security review. File access was loose. Logging incomplete. Backups weren’t encrypted. They moved to Managed IT Services in Maryland. Gaps were mapped. Controls fixed. A secure ITAR setup was built. Six weeks later, they passed the follow-up review. A key contract stayed active. Stress dropped. Final Thoughts ITAR and NIST 800-171 are not trends. They are already part of doing business in Maryland. Ignoring them doesn’t make them easier. It only delays the hit. For regulated teams, Managed IT Services in Maryland are about control. Control over audits. Over risk. Over long-term work. If your current IT support in Maryland can’t explain your compliance position clearly, that silence is already a problem. FAQs
Read full post on gocorptech.com
HIPAA Compliance for Northeast Ohio Healthcare Providers: An IT Checklist
HIPAA compliance checklist for Cleveland healthcare providers. See what IT safeguards Ohio medical practices need to protect their patient data and avoid fines. In This Article: Your medical practice handles sensitive patient data every single day. Electronic health records, billing information, treatment notes, and personal medical histories flow through your systems constantly. One HIPAA violation
HIPAA compliance checklist for Cleveland healthcare providers. See what IT safeguards Ohio medical practices need to protect their patient data and avoid fines. In This Article: Your medical practice handles sensitive patient data every single day. Electronic health records, billing information, treatment notes, and personal medical histories flow through your systems constantly. One HIPAA violation
Read full post on infinit.usFailed to load more articles
You're all caught up!
Check back later for more compliance news.
MSPdb™ News

Questions Hospitals Should Ask HIPAA Managed IT Providers
Managed IT services for hospitals means outsourcing IT infrastructure, cybersecurity, and HIPAA compliance operations to a third-party provider under a formal service-level agreement. When evaluating providers, hospitals should ask specific questions across four risk categories: HIPAA documentation and audit readiness, managed detection and response for clinical networks, ransomware resilience and backup recovery, and subcontractor HIPAA ... Read more
Managed IT services for hospitals means outsourcing IT infrastructure, cybersecurity, and HIPAA compliance operations to a third-party provider under a formal service-level agreement. When evaluating providers, hospitals should ask specific questions across four risk categories: HIPAA documentation and audit readiness, managed detection and response for clinical networks, ransomware resilience and backup recovery, and subcontractor HIPAA ... Read more
Read full post on meriplex.com
The IT Compliance Problem Cannabis Businesses Don’t Talk About
Direct Answer: Cannabis businesses face unique IT compliance requirements around data security, access controls, and state reporting systems — and most have no formal plan to meet them. Monterey County now has dozens of licensed cannabis operators — cultivators in the Salinas Valley, dispensaries near Marina and Seaside, distributors moving product through the region —
Direct Answer: Cannabis businesses face unique IT compliance requirements around data security, access controls, and state reporting systems — and most have no formal plan to meet them. Monterey County now has dozens of licensed cannabis operators — cultivators in the Salinas Valley, dispensaries near Marina and Seaside, distributors moving product through the region —
Read full post on adaptiveis.net
What Is CMMC Compliance & Why It Matters
Every year there are growing cybersecurity risks, especially across the Defense Industrial Base (DIB). To strengthen national security and ensure consistent cyber hygiene across contractors, the U.S. Department of War (DoW) created the Cybersecurity Maturity Model Certification (CMMC). The latest version, CMMC 2.0, streamlines the framework by reducing the levels from five to three and aligning the requirements with NIST standards. This guide covers: what CMMC is, why this compliance matters, the three certification levels, and the path to compliance.
Every year there are growing cybersecurity risks, especially across the Defense Industrial Base (DIB). To strengthen national security and ensure consistent cyber hygiene across contractors, the U.S. Department of War (DoW) created the Cybersecurity Maturity Model Certification (CMMC). The latest version, CMMC 2.0, streamlines the framework by reducing the levels from five to three and aligning the requirements with NIST standards. This guide covers: what CMMC is, why this compliance matters, the three certification levels, and the path to compliance.
Read full post on dpsolutions.com
Why SMBs Should Partner with SOC 2 Certified MSPs
In today’s rapidly evolving digital landscape, small and medium-sized businesses (SMBs) face unprecedented challenges when it comes to data security, compliance, and operational resilience. Cyber threats are becoming more sophisticated, while customers and business partners increasingly expect organizations to maintain strong security and privacy standards. For SMBs, partnering with a SOC 2 certified Managed Service
In today’s rapidly evolving digital landscape, small and medium-sized businesses (SMBs) face unprecedented challenges when it comes to data security, compliance, and operational resilience. Cyber threats are becoming more sophisticated, while customers and business partners increasingly expect organizations to maintain strong security and privacy standards. For SMBs, partnering with a SOC 2 certified Managed Service
Read full post on trndigital.com
What Is Third-Party Vendor Risk Management?
Third-party vendor risk management is the process of identifying, assessing, and reducing risks caused by external service providers that your business depends on.
Third-party vendor risk management is the process of identifying, assessing, and reducing risks caused by external service providers that your business depends on.
Read full post on coretechllc.com
Achieving CMMC Compliance with Vision Computer Solutions
If your business is a contractor for the Department of Defense (DoD) in the United States, navigating the world of Cybersecurity Maturity Model Certification (CMMC) is not just an option—it’s a necessity. Achieving CMMC compliance demonstrates that your organization meets crucial cybersecurity standards designed to protect sensitive government information. This certification validates your security posture
If your business is a contractor for the Department of Defense (DoD) in the United States, navigating the world of Cybersecurity Maturity Model Certification (CMMC) is not just an option—it’s a necessity. Achieving CMMC compliance demonstrates that your organization meets crucial cybersecurity standards designed to protect sensitive government information. This certification validates your security posture
Read full post on vcsolutions.com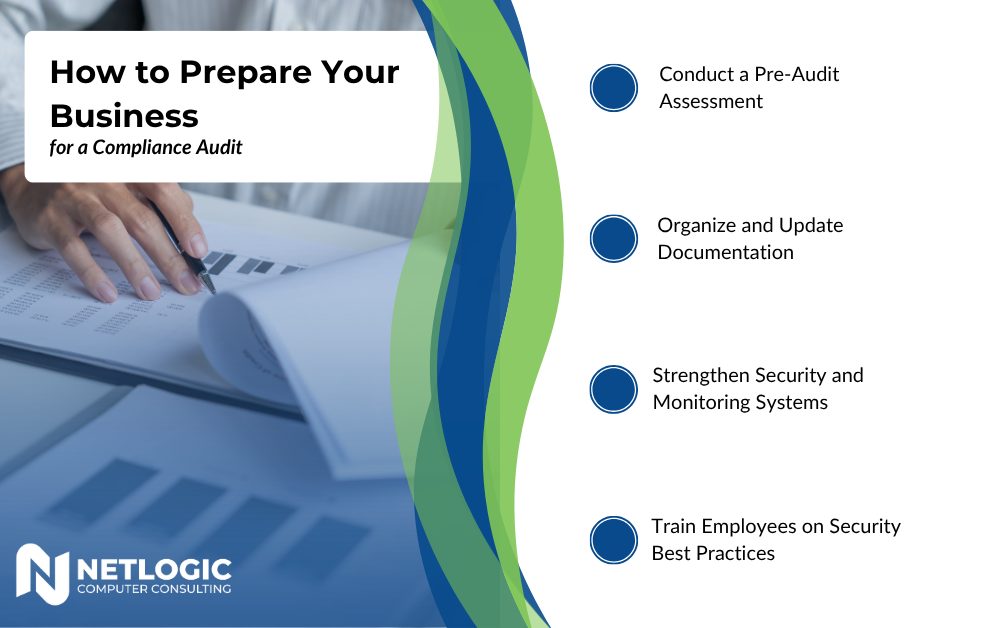
How to Prepare Your Business for a Compliance Audit
Compliance audits are becoming more common across industries, especially as cybersecurity threats and data regulations continue to evolve. For many business owners, the idea of an audit brings uncertainty. What are auditors actually looking for? And more importantly, how can you be confident your business is prepared? The reality is that compliance is not just
Compliance audits are becoming more common across industries, especially as cybersecurity threats and data regulations continue to evolve. For many business owners, the idea of an audit brings uncertainty. What are auditors actually looking for? And more importantly, how can you be confident your business is prepared? The reality is that compliance is not just
Read full post on netlogiccomputer.com
How SOC Monitoring Helps You Meet Security Compliance Requirements
If a compliance requirement just landed on your desk with SOC monitoring attached to it, it might imply hours of research and months of work. While the terminology sounds like a fancy tech solution, the core idea behind SOC monitoring is actually very straightforward. It’s simply a team of professionals that monitors your systems. The
If a compliance requirement just landed on your desk with SOC monitoring attached to it, it might imply hours of research and months of work. While the terminology sounds like a fancy tech solution, the core idea behind SOC monitoring is actually very straightforward. It’s simply a team of professionals that monitors your systems. The
Read full post on reliabletechnology.co
AI Governance for Private Equity: The Missing Piece of Your Firm’s Data Policy
By Kirk Samuels, Executive Director Cybersecurity PE firms handle some of the most sensitive data in business. This blog explores
By Kirk Samuels, Executive Director Cybersecurity PE firms handle some of the most sensitive data in business. This blog explores
Read full post on netrio.com
How Fidelity State Bank Achieved IT Compliance Success
“That was an eye-opening … learning experience, knowing that [RESULTS Technology] was working behind the scenes to make sure that we were kept up to date, compliant, and secure.” —Noel Gaucin, VP Loan Officer for Fidelity State Bank & Trust Company Running a community bank is all about striking the right balance: delivering great service
“That was an eye-opening … learning experience, knowing that [RESULTS Technology] was working behind the scenes to make sure that we were kept up to date, compliant, and secure.” —Noel Gaucin, VP Loan Officer for Fidelity State Bank & Trust Company Running a community bank is all about striking the right balance: delivering great service
Read full post on resultstechnology.comPopular MSPs
View AllStay Updated
Get the latest it compliance advice for growing companies delivered to your inbox.