MSPs are real, and their spectacular.
Discover leading Managed IT Service Providers across USA, Canada & the United Kingdom.
- 100s of leading MSPs
- Find a MSP near you
- Latest IT news for SMBs

Maintaining Data Security In Cloud Computing
With more and more businesses and companies moving to cloud computing solutions it’s important to understand the basics of maintaining data security in cloud computing. Hackers aren’t looking for financial and credit card information as much as they used to—they are looking to obtain sensitive data that they can hold for ransom. Much of the
With more and more businesses and companies moving to cloud computing solutions it’s important to understand the basics of maintaining data security in cloud computing. Hackers aren’t looking for financial and credit card information as much as they used to—they are looking to obtain sensitive data that they can hold for ransom. Much of the
Read full post on amanetworks.comMSPdb™ News

Stop Wasting Your Software Budget: The Employee Training Gap
Most businesses spend heavily on software and almost nothing training their teams to actually use it. Employees use an average of just 40% of available features in the tools they are given, [1] while companies waste an average of $18 million annually on SaaS licenses that deliver little to no return. [2] The fix is not more software. It is better training on what you already own.
Most businesses spend heavily on software and almost nothing training their teams to actually use it. Employees use an average of just 40% of available features in the tools they are given, [1] while companies waste an average of $18 million annually on SaaS licenses that deliver little to no return. [2] The fix is not more software. It is better training on what you already own.
Read full post on sentrytechsolutions.com
Top Golf, Top Partners: Bringing Kansas City’s Leaders Together
The best partnerships are built face-to-face. That’s why MDL recently hosted a Top Golf event for leaders, business decision-makers, and trusted vendor partners from across Kansas City. It was an afternoon of swinging clubs, swapping stories, and building the kind of relationships that don’t happen over a calendar invite. A Word From Our Partners at
The best partnerships are built face-to-face. That’s why MDL recently hosted a Top Golf event for leaders, business decision-makers, and trusted vendor partners from across Kansas City. It was an afternoon of swinging clubs, swapping stories, and building the kind of relationships that don’t happen over a calendar invite. A Word From Our Partners at
Read full post on mdltechnology.com
Uncovering the Hidden Security Risks of Your BYOD Policy
Once upon a time, Bring Your Own Device (BYOD) was seen as mutually beneficial. An employer could save substantial costs by eliminating the need for new hardware investment, while the employee didn’t have to juggle devices and could stick with what was familiar and comfortable.However, there is a pretty significant drawback that could upend the undeniable usefulness of BYOD if it isn’t addressed: the inherent insecurity that the business needs to contend with.
Once upon a time, Bring Your Own Device (BYOD) was seen as mutually beneficial. An employer could save substantial costs by eliminating the need for new hardware investment, while the employee didn’t have to juggle devices and could stick with what was familiar and comfortable.However, there is a pretty significant drawback that could upend the undeniable usefulness of BYOD if it isn’t addressed: the inherent insecurity that the business needs to contend with.
Read full post on coretechllc.com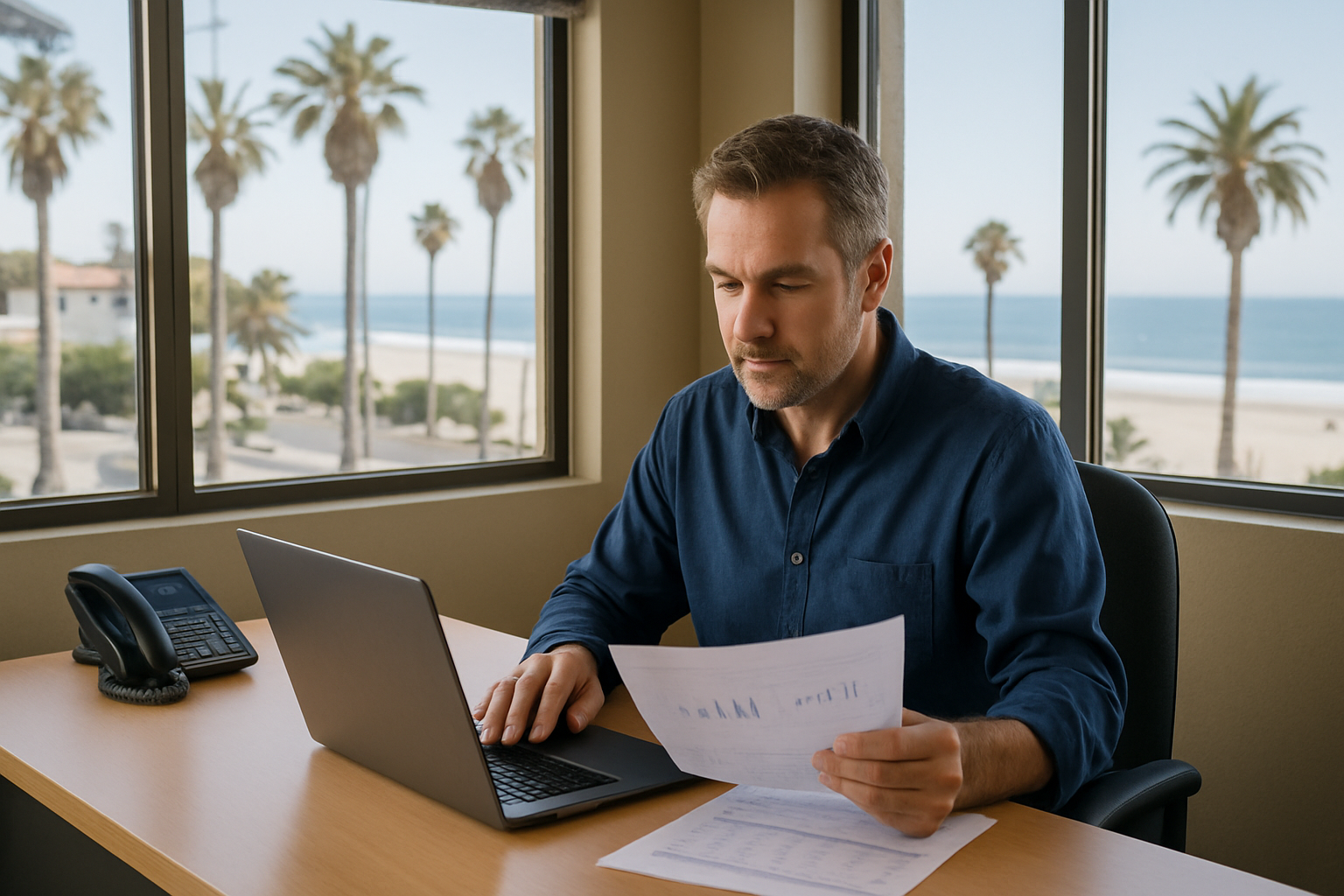
How Small Businesses in Monterey Are Handling IT Without an In-House Team
Direct Answer: Most small businesses in Monterey handle IT by outsourcing to a managed services provider — getting full IT support at a predictable monthly cost, without hiring a full-time employee. Most small businesses in Monterey County don’t have an IT department. No dedicated technician, no helpdesk ticket system, no one watching the network overnight.
Direct Answer: Most small businesses in Monterey handle IT by outsourcing to a managed services provider — getting full IT support at a predictable monthly cost, without hiring a full-time employee. Most small businesses in Monterey County don’t have an IT department. No dedicated technician, no helpdesk ticket system, no one watching the network overnight.
Read full post on adaptiveis.net
Questions Hospitals Should Ask HIPAA Managed IT Providers
Managed IT services for hospitals means outsourcing IT infrastructure, cybersecurity, and HIPAA compliance operations to a third-party provider under a formal service-level agreement. When evaluating providers, hospitals should ask specific questions across four risk categories: HIPAA documentation and audit readiness, managed detection and response for clinical networks, ransomware resilience and backup recovery, and subcontractor HIPAA ... Read more
Managed IT services for hospitals means outsourcing IT infrastructure, cybersecurity, and HIPAA compliance operations to a third-party provider under a formal service-level agreement. When evaluating providers, hospitals should ask specific questions across four risk categories: HIPAA documentation and audit readiness, managed detection and response for clinical networks, ransomware resilience and backup recovery, and subcontractor HIPAA ... Read more
Read full post on meriplex.com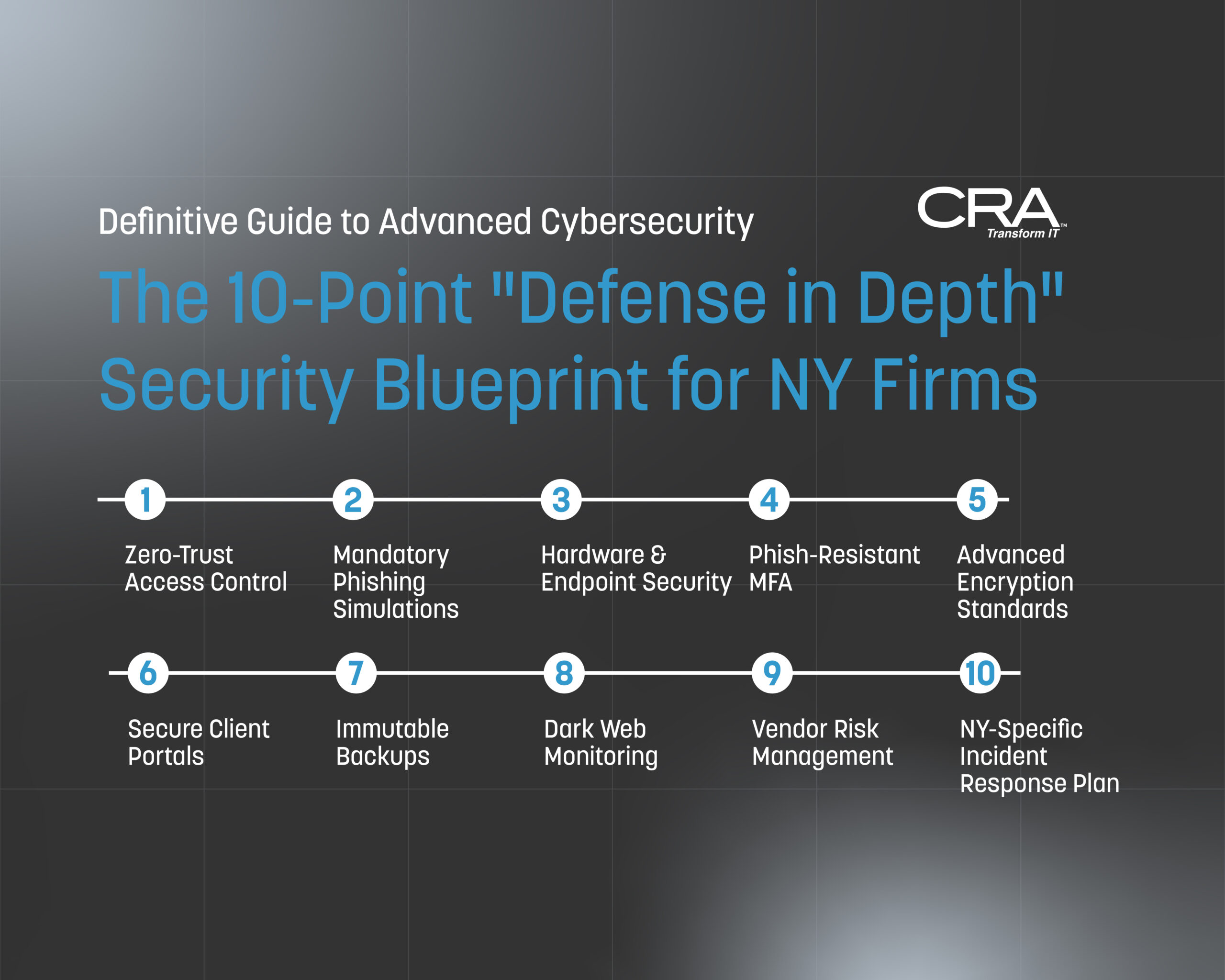
Advanced Cybersecurity for New York Law Firms: The Definitive Guide for Compliance & Protection in 2026
Introduction: The Cost of Complacency in the New York Legal Landscape New York law firms occupy a unique and paradoxical position in the cybersecurity landscape. On one hand, your firm handles some of the most sensitive, high-value information in the world — privileged communications, M&A deal structures, real estate escrow instructions, litigation strategies, and the…
Introduction: The Cost of Complacency in the New York Legal Landscape New York law firms occupy a unique and paradoxical position in the cybersecurity landscape. On one hand, your firm handles some of the most sensitive, high-value information in the world — privileged communications, M&A deal structures, real estate escrow instructions, litigation strategies, and the…
Read full post on consultcra.com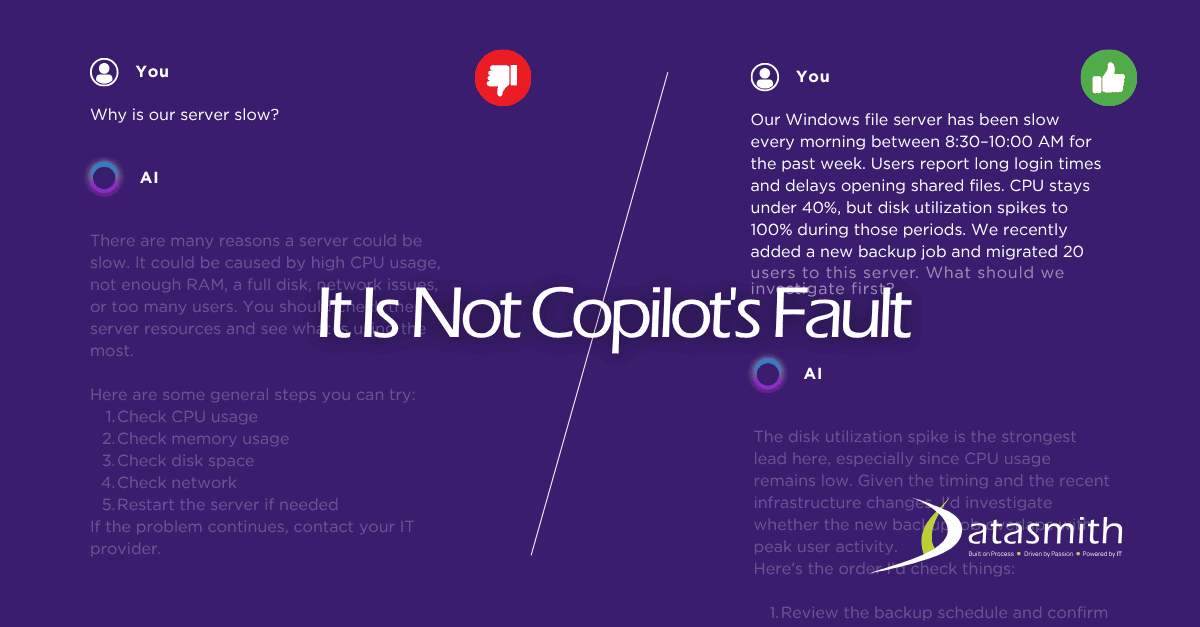
Getting Bad Results from Microsoft Copilot? The Problem Is Almost Never the Tool.
The Short Answer Bad results from Microsoft Copilot almost always trace back to one of two problems, and neither of them
The Short Answer Bad results from Microsoft Copilot almost always trace back to one of two problems, and neither of them
Read full post on datasmithnetworks.com
How Hackers Actually Get Into Small Business Networks
Many organizations still picture cyberattacks as highly sophisticated, targeted operations. In reality, understanding how hackers get into small business networks reveals a much more practical and often simpler truth. Most breaches do not start with complex exploits. They begin with overlooked gaps, everyday tools, and predictable human behavior. For small businesses, this creates a dangerous
Many organizations still picture cyberattacks as highly sophisticated, targeted operations. In reality, understanding how hackers get into small business networks reveals a much more practical and often simpler truth. Most breaches do not start with complex exploits. They begin with overlooked gaps, everyday tools, and predictable human behavior. For small businesses, this creates a dangerous
Read full post on superion.ca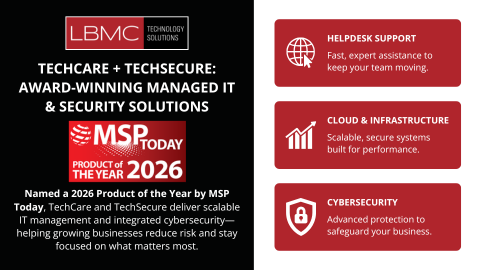
LBMC Technology Solutions Wins 2026 MSP Today Product of the Year Award
Nashville, TN — May 2026 — LBMC Technology Solutions today announced that its managed IT and security solutions, TechCare and TechSecure, have been named winners of the 2026 MSP Today Product of the Year Award, presented by TMC, a global, integrated media company. The MSP Today Product of the Year Award honors the most innovative and impactful products and services shaping the managed services landscape. TechCare and TechSecure were recognized for their ability to deliver a unified approach to IT operations and cybersecurity—driving measurable outcomes for both customers and channel partners.
Nashville, TN — May 2026 — LBMC Technology Solutions today announced that its managed IT and security solutions, TechCare and TechSecure, have been named winners of the 2026 MSP Today Product of the Year Award, presented by TMC, a global, integrated media company. The MSP Today Product of the Year Award honors the most innovative and impactful products and services shaping the managed services landscape. TechCare and TechSecure were recognized for their ability to deliver a unified approach to IT operations and cybersecurity—driving measurable outcomes for both customers and channel partners.
Read full post on lbmctech.com
What Is an MSP Provider?
What Is an MSP Provider? Managed IT Services Explained Businesses rely heavily on technology to manage operations, communicate with customers, store sensitive information, and maintain productivity. From cloud-based software and cybersecurity protection to network infrastructure and remote work capabilities, modern organizations depend on stable, secure IT environments more than ever. However, managing technology internally can
What Is an MSP Provider? Managed IT Services Explained Businesses rely heavily on technology to manage operations, communicate with customers, store sensitive information, and maintain productivity. From cloud-based software and cybersecurity protection to network infrastructure and remote work capabilities, modern organizations depend on stable, secure IT environments more than ever. However, managing technology internally can
Read full post on bemaservices.com