Cybersecurity
Latest cybersecurity news, ransomware alerts, and threat intelligence for growing companies.

Vulnerability Assessment vs Penetration Testing
When it comes to protecting your business from cyber threats, two security testing methods stand out: vulnerability assessments and penetration testing. While both help identify security weaknesses, they serve very different purposes and provide distinct value to your organization.
When it comes to protecting your business from cyber threats, two security testing methods stand out: vulnerability assessments and penetration testing. While both help identify security weaknesses, they serve very different purposes and provide distinct value to your organization.
Read full post on sirkit.ca
Ransomware in 2026: What LA Businesses Need to Know Right Now
Ransomware is still one of the fastest ways for a mid-size business to lose momentum. In Los Angeles, that risk is amplified by hybrid work, multiple offices, vendor-heavy operations, aging infrastructure, and constant pressure around uptime and data protection. When ransomware hits, it is not just a cybersecurity issue. It becomes an operations issue, a
Ransomware is still one of the fastest ways for a mid-size business to lose momentum. In Los Angeles, that risk is amplified by hybrid work, multiple offices, vendor-heavy operations, aging infrastructure, and constant pressure around uptime and data protection. When ransomware hits, it is not just a cybersecurity issue. It becomes an operations issue, a
Read full post on crimsonit.com
The State of Cybersecurity in Canada (2026): Key Takeaways for Small Business
The State of Cybersecurity in Canada (2026): Key Takeaways for Small Business Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping Canadian businesses build and manage secure IT infrastructure since 2012 across Toronto, Hamilton, and Metro Vancouver. The average data breach in Canada now costs CA$6.98 million. That’s up 10.4% from last year,
The State of Cybersecurity in Canada (2026): Key Takeaways for Small Business Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping Canadian businesses build and manage secure IT infrastructure since 2012 across Toronto, Hamilton, and Metro Vancouver. The average data breach in Canada now costs CA$6.98 million. That’s up 10.4% from last year,
Read full post on fusioncomputing.ca
This Week In Cybersecurity | April 10th, 2026
This Week in Cybersecurity Each week at Applied Tech we recap the biggest cybersecurity news headlines from the week to keep you informed and ready to face the latest threats. Here’s your breakdown for the week of April 4th – April 10th. Major FBI Breach A data breach targeting an FBI surveillance system is being
This Week in Cybersecurity Each week at Applied Tech we recap the biggest cybersecurity news headlines from the week to keep you informed and ready to face the latest threats. Here’s your breakdown for the week of April 4th – April 10th. Major FBI Breach A data breach targeting an FBI surveillance system is being
Read full post on appliedtech.us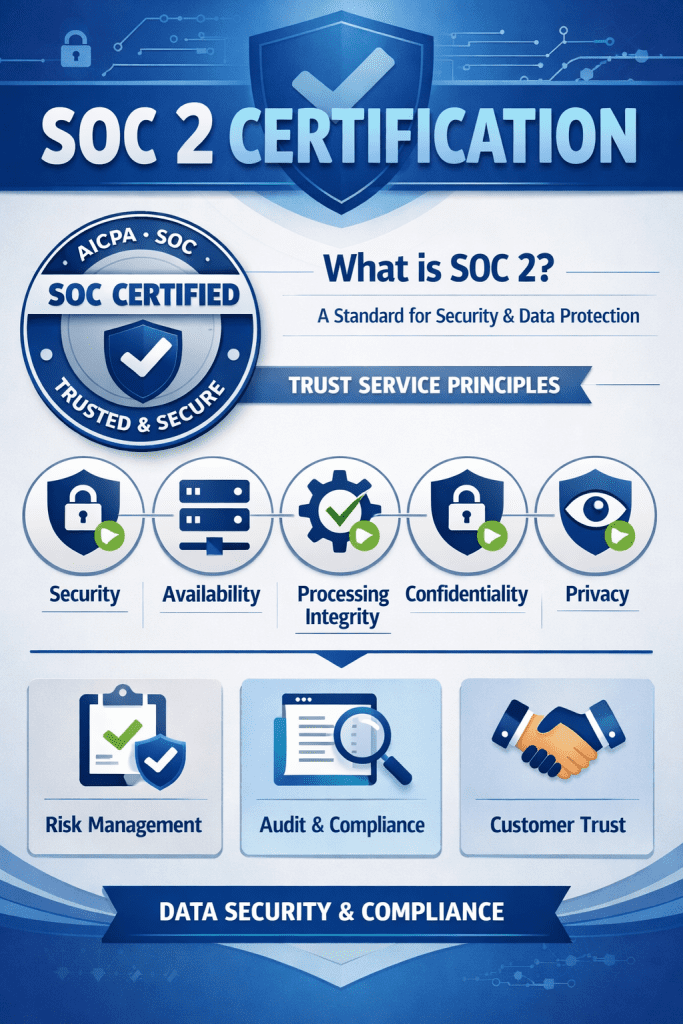
SOC 2 Compliance in Canada
Last Updated on April 10, 2026 by Matthew Goodchild SOC 2 Compliance in Canada: Type 1 vs Type 2, Certification & Checklist | CG Technologies Cybersecurity & Compliance SOC 2 Compliance in Canada: Type 1 vs Type 2, Certification & Checklist What Ontario businesses need to know before starting — and what CG Technologies can
Last Updated on April 10, 2026 by Matthew Goodchild SOC 2 Compliance in Canada: Type 1 vs Type 2, Certification & Checklist | CG Technologies Cybersecurity & Compliance SOC 2 Compliance in Canada: Type 1 vs Type 2, Certification & Checklist What Ontario businesses need to know before starting — and what CG Technologies can
Read full post on cgtechnologies.com
Cybersecurity Services Aren’t a One-Time Fix Anymore
Cybersecurity Services Introduction: What This Page Covers This page explains what cybersecurity services are, why they matter for modern organizations, and how to choose the right solutions for your business. Designed for business owners, IT leaders, and decision-makers, this guide will help you understand the critical role cybersecurity services play in protecting your organization from
Cybersecurity Services Introduction: What This Page Covers This page explains what cybersecurity services are, why they matter for modern organizations, and how to choose the right solutions for your business. Designed for business owners, IT leaders, and decision-makers, this guide will help you understand the critical role cybersecurity services play in protecting your organization from
Read full post on enitechsolutions.com
How to Survive a Total Ransomware Lockout
Imagine the terror of arriving at the office only to find every screen glowing with the same cryptic message: "Your files are encrypted." If you’re like most business owners, this kind of situation could set you back weeks, and that’s not to mention the financial setback and permanent data loss that could occur as a result of such a ransomware attack. What your business needs is resilience, the kind that only immutable backups can offer.
Imagine the terror of arriving at the office only to find every screen glowing with the same cryptic message: "Your files are encrypted." If you’re like most business owners, this kind of situation could set you back weeks, and that’s not to mention the financial setback and permanent data loss that could occur as a result of such a ransomware attack. What your business needs is resilience, the kind that only immutable backups can offer.
Read full post on coretechllc.com
You Can’t Secure What You Can’t See: Why Asset Visibility Is a Cybersecurity Requirement
Asset visibility is one of the most overlooked parts of cybersecurity. In this blog, we explain why businesses need clear visibility into hardware, software, users, and cloud assets to reduce risk, strengthen operations, and support compliance.
Asset visibility is one of the most overlooked parts of cybersecurity. In this blog, we explain why businesses need clear visibility into hardware, software, users, and cloud assets to reduce risk, strengthen operations, and support compliance.
Read full post on v2systems.com
CIS Controls v8.1 for Small Business: How Canadian SMBs Can Build a Real Cybersecurity Program (2026)
CIS Controls v8.1 for Small Business: How Canadian SMBs Can Build a Real Cybersecurity Program (2026) Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping Canadian businesses build and manage secure IT infrastructure since 2012 across Toronto, Hamilton, and Metro Vancouver. Forty-three percent of Canadian organizations were hit by a cyberattack in the
CIS Controls v8.1 for Small Business: How Canadian SMBs Can Build a Real Cybersecurity Program (2026) Written by Mike Pearlstein, CISSP, CEO of Fusion Computing Limited. Helping Canadian businesses build and manage secure IT infrastructure since 2012 across Toronto, Hamilton, and Metro Vancouver. Forty-three percent of Canadian organizations were hit by a cyberattack in the
Read full post on fusioncomputing.ca
Financial Services Cybersecurity Compliance Guide | All Covered
Financial services cybersecurity is essential for protecting sensitive financial data, maintaining regulatory compliance, and preserving client trust. As financial firms expand digital banking platforms, trading systems, payment networks, and cloud environments, cyber risk increases across every layer of infrastructure.Financial institutions operate in one of the most heavily regulated and targeted industries. Improving cybersecurity compliance requires a structured, proactive approach that aligns security controls with evolving regulatory requirements.
Financial services cybersecurity is essential for protecting sensitive financial data, maintaining regulatory compliance, and preserving client trust. As financial firms expand digital banking platforms, trading systems, payment networks, and cloud environments, cyber risk increases across every layer of infrastructure.Financial institutions operate in one of the most heavily regulated and targeted industries. Improving cybersecurity compliance requires a structured, proactive approach that aligns security controls with evolving regulatory requirements.
Read full post on allcovered.com
How to Take a Proactive Approach to Cybersecurity Risk Management
Cybersecurity threats are not a matter of “if,” but “when.” Mid-sized organizations face an increasingly complex threat landscape, with cybercriminals targeting everything from endpoints and cloud environments to email systems and supply chains. While many…
Cybersecurity threats are not a matter of “if,” but “when.” Mid-sized organizations face an increasingly complex threat landscape, with cybercriminals targeting everything from endpoints and cloud environments to email systems and supply chains. While many…
Read full post on thrivenextgen.com
Cybersecurity for the Real World: Advice From an IT Consultant Greenville Businesses Trust
In the bustling business landscape of Upstate South Carolina, security… Read more
In the bustling business landscape of Upstate South Carolina, security… Read more
Read full post on brightflow.net
How SMBs Can Use AI to Prevent Cyber Attacks
Cybersecurity is no longer just a concern for big companies. In fact, cyberattacks have already impacted nearly half of U.S. small businesses. Hackers know that smaller firms lack the deep resources and complex defenses of large enterprises, so they prey on small targets. In this environment, using artificial intelligence in cybersecurity is a force-multiplier. AI-powered
Cybersecurity is no longer just a concern for big companies. In fact, cyberattacks have already impacted nearly half of U.S. small businesses. Hackers know that smaller firms lack the deep resources and complex defenses of large enterprises, so they prey on small targets. In this environment, using artificial intelligence in cybersecurity is a force-multiplier. AI-powered
Read full post on panatexperts.com
Ransomware Recovery Readiness: Backups Alone Aren’t Enough
Ransomware Recovery Readiness: Backups Alone Aren’t Enough People assume that if backups are in place, recovery is handled. Files are copied somewhere safe, retention is configured, and that box gets checked during audits. Then ransomware hits, and teams discover how many decisions sit between having backups and actually restoring the business. Ransomware Recovery Doesn’t Fail
Ransomware Recovery Readiness: Backups Alone Aren’t Enough People assume that if backups are in place, recovery is handled. Files are copied somewhere safe, retention is configured, and that box gets checked during audits. Then ransomware hits, and teams discover how many decisions sit between having backups and actually restoring the business. Ransomware Recovery Doesn’t Fail
Read full post on appliedtech.us
Sagiss Achieves MSP Cyber Verify Certification and SOC 2 Type II Report, Continuing a Commitment to Security Since 2017
Security, compliance, and trust are foundational to every technology partnership. Sagiss is proud to announce the successful completion of its latest MSP Cyber Verify and SOC 2 Type II audits and certifications. This milestone reflects an ongoing commitment to protecting client operations through proven processes and independent validation.
Security, compliance, and trust are foundational to every technology partnership. Sagiss is proud to announce the successful completion of its latest MSP Cyber Verify and SOC 2 Type II audits and certifications. This milestone reflects an ongoing commitment to protecting client operations through proven processes and independent validation.
Read full post on sagiss.com
MDR vs XDR vs SIEM: What’s the Difference?
💡 EXCLUSIVE Resource: MSSP Pricing Calculator Calculate Your Pricing SIEM is a technology for collecting and analyzing cybersecurity data, while MDR and XDR offer overlapping but differing approaches to threat detection and response. So which solution—or solutions—does your organization need? Here’s how these solutions compare and how to choose the right mix for your business.
💡 EXCLUSIVE Resource: MSSP Pricing Calculator Calculate Your Pricing SIEM is a technology for collecting and analyzing cybersecurity data, while MDR and XDR offer overlapping but differing approaches to threat detection and response. So which solution—or solutions—does your organization need? Here’s how these solutions compare and how to choose the right mix for your business.
Read full post on corsicatech.com
The Stryker Cyberattack
SECURITY BRIEFING The Stryker Cyberattack: What It Was, Why It Happened, and Why Your Organization Is Protected Executive Summary On March 11, 2026, Stryker Corporation — a Fortune 500 medical device manufacturer with $25 billion in annual revenue and 56,000 employees — experienced one of the most disruptive cyberattacks in
SECURITY BRIEFING The Stryker Cyberattack: What It Was, Why It Happened, and Why Your Organization Is Protected Executive Summary On March 11, 2026, Stryker Corporation — a Fortune 500 medical device manufacturer with $25 billion in annual revenue and 56,000 employees — experienced one of the most disruptive cyberattacks in
Read full post on techriver.com
How to Prepare for a Cyber Attack: Tips for Small Businesses
To prepare for a cyber attack, a small business needs more than basic security tools. Too many companies wait until something goes wrong, and by then the response is slower, more expensive, and harder to manage. At MDL Technology, we help businesses prepare with stronger security basics, better visibility, employee training, and a clear response
To prepare for a cyber attack, a small business needs more than basic security tools. Too many companies wait until something goes wrong, and by then the response is slower, more expensive, and harder to manage. At MDL Technology, we help businesses prepare with stronger security basics, better visibility, employee training, and a clear response
Read full post on mdltechnology.com
Phishing & Social Engineering: How to Train & Protect Your Team
If you run a small or midsize business, you already know cybersecurity is no longer just a technical issue sitting quietly in the background. It is a business issue. It affects your operations, your reputation, your client trust, and your team’s ability to work without disruption. And while firewalls, endpoint protection, and monitoring tools all
If you run a small or midsize business, you already know cybersecurity is no longer just a technical issue sitting quietly in the background. It is a business issue. It affects your operations, your reputation, your client trust, and your team’s ability to work without disruption. And while firewalls, endpoint protection, and monitoring tools all
Read full post on leaftechit.com
Endpoint Security in a Remote Work World
Remote work is no longer a temporary shift. It is how many businesses now operate every day. Your team works from home offices, shared spaces, airports, client sites, and everywhere in between. That flexibility creates opportunity, but it also creates risk. If you want to protect your business in a distributed environment, endpoint security has
Remote work is no longer a temporary shift. It is how many businesses now operate every day. Your team works from home offices, shared spaces, airports, client sites, and everywhere in between. That flexibility creates opportunity, but it also creates risk. If you want to protect your business in a distributed environment, endpoint security has
Read full post on leaftechit.comFailed to load more articles
You're all caught up!
Check back later for more cybersecurity news.
MSPdb™ News

SOC Goals, SIEM-ply Smarter, and Let Your Defenses SOAR: Your Upgrade to Modern, Unified Defense.

Is That Email Legit? How to Check for These 3 Phishing Red Flags
Most contemporary cyberthreats originate from social engineering. Typically, this involves deceptive phishing messages designed to lure users into compromising their own safety. While these attacks can occur across various platforms, email remains the primary weapon of choice for attackers.To stay protected, let’s examine the key red flags that suggest an email is actually a phishing attempt.
Most contemporary cyberthreats originate from social engineering. Typically, this involves deceptive phishing messages designed to lure users into compromising their own safety. While these attacks can occur across various platforms, email remains the primary weapon of choice for attackers.To stay protected, let’s examine the key red flags that suggest an email is actually a phishing attempt.
Read full post on phantomts.com
What an Endpoint Protection Platform Does for Small Business Security
Learn what an endpoint protection platform does, how endpoint protection helps small businesses stop cyber threats, and why modern endpoint security solutions matter.
Learn what an endpoint protection platform does, how endpoint protection helps small businesses stop cyber threats, and why modern endpoint security solutions matter.
Read full post on bastionpoint.com
The Cyber Attack Hiding in Your Inbox and it came from Microsoft?
A financial services firm in western Pittsburgh area reached out to Midnight Blue Technology Services in crisis mode. Cybercriminals had spent nearly two weeks inside their Microsoft 365 environment before anyone noticed. By the time the ransomware deployed, the attackers had read confidential client communications, mapped the entire organization, and positioned themselves for maximum damage. The door they walked
A financial services firm in western Pittsburgh area reached out to Midnight Blue Technology Services in crisis mode. Cybercriminals had spent nearly two weeks inside their Microsoft 365 environment before anyone noticed. By the time the ransomware deployed, the attackers had read confidential client communications, mapped the entire organization, and positioned themselves for maximum damage. The door they walked
Read full post on midnightbluetech.com
The Good and the Evil of AI in Cybersecurity: How Ransomware Is Evolving at Machine Speed
How AI Is Changing Ransomware Threats It doesn’t start with a bang anymore. There’s no dramatic breach alert or obvious system failure, at least not at first. Instead, it begins quietly. An employee receives a phishing email that looks legitimate. It might reference a real vendor, a recent invoice, or even an internal conversation from a known
How AI Is Changing Ransomware Threats It doesn’t start with a bang anymore. There’s no dramatic breach alert or obvious system failure, at least not at first. Instead, it begins quietly. An employee receives a phishing email that looks legitimate. It might reference a real vendor, a recent invoice, or even an internal conversation from a known
Read full post on alvaka.net
Ways to Protect Your Small Business with Ransomware Protection
Strong ransomware protection matters because one bad click, weak password, or missed update can disrupt your business. For small businesses, the damage often goes beyond the attack itself and leads to downtime, lost access, and a harder recovery. At MDL Technology, we help businesses reduce that risk with stronger security, better monitoring, and a clear
Strong ransomware protection matters because one bad click, weak password, or missed update can disrupt your business. For small businesses, the damage often goes beyond the attack itself and leads to downtime, lost access, and a harder recovery. At MDL Technology, we help businesses reduce that risk with stronger security, better monitoring, and a clear
Read full post on mdltechnology.com
Cybersecurity for Small Businesses: PCe Solutions’ Calgary Defense Strategy
Cybersecurity for Small Businesses: PCe Solutions’ Calgary Defense Strategy PCe Solutions protects Calgary small businesses with a proven, layered cybersecurity defense strategy built specifically for Alberta’s threat landscape and regulatory environment There is a dangerous myth circulating in Calgary’s small business community — and it’s costing local organizations dearly. The myth goes like this: cybercriminals...
Cybersecurity for Small Businesses: PCe Solutions’ Calgary Defense Strategy PCe Solutions protects Calgary small businesses with a proven, layered cybersecurity defense strategy built specifically for Alberta’s threat landscape and regulatory environment There is a dangerous myth circulating in Calgary’s small business community — and it’s costing local organizations dearly. The myth goes like this: cybercriminals...
Read full post on pcesolutions.ca
Ransomware Fears: How to Prepare Before an Attack Hits
Learn how to prepare your organization for ransomware threats. Expert strategies to safeguard data and ensure business continuity in 2026.
Learn how to prepare your organization for ransomware threats. Expert strategies to safeguard data and ensure business continuity in 2026.
Read full post on trndigital.com
The Ransomware Wake-Up Call: 75% of SMBs Risk Shutting Down
Explore the ransomware wake-up call: 75% of SMBs risk shutting down after an attack. Learn how to protect your business with a practical resilience roadmap.
Explore the ransomware wake-up call: 75% of SMBs risk shutting down after an attack. Learn how to protect your business with a practical resilience roadmap.
Read full post on adaptiveis.net
Why Detection Speed in Cybersecurity Is Now a Business Issue
Most organizations still think business cybersecurity is about stopping attacks. The reality is most incidents aren’t prevented. They’re detected. And how fast detection speed happens is what determines impact. That’s why CISA emphasizes Threat Detection as a core pillar of Zero Trust. Not just keeping threats out, but identifying and responding to them quickly once
Most organizations still think business cybersecurity is about stopping attacks. The reality is most incidents aren’t prevented. They’re detected. And how fast detection speed happens is what determines impact. That’s why CISA emphasizes Threat Detection as a core pillar of Zero Trust. Not just keeping threats out, but identifying and responding to them quickly once
Read full post on msgrouponline.comPopular MSPs
View AllStay Updated
Get the latest cybersecurity advice for growing companies delivered to your inbox.