Find the IT consulting you need.
Discover leading Managed IT Service Providers across USA, Canada & the United Kingdom.
- 100s of leading MSPs
- Find a MSP near you
- Latest IT news for SMBs
How to Secure Contractor and Vendor Access Without Expanding Your MDM Footprint
For most enterprises today, third-party access is just part of work. Contractors, vendors, consultants, and short-term staff all need quick access to internal apps and files so things don’t slow down. But security teams are already overloaded. More tools, more devices, more rules. It adds up fast. This is where the old MDM-first approach starts to feel heavy and outdated. IAM, IT Ops, and security leaders are asking a fair question now. How do we secure access without forcing MDM on personal devices or creating privacy issues? Managing devices we don’t own never feels clean, and it rarely sca
For most enterprises today, third-party access is just part of work. Contractors, vendors, consultants, and short-term staff all need quick access to internal apps and files so things don’t slow down. But security teams are already overloaded. More tools, more devices, more rules. It adds up fast. This is where the old MDM-first approach starts to feel heavy and outdated. IAM, IT Ops, and security leaders are asking a fair question now. How do we secure access without forcing MDM on personal devices or creating privacy issues? Managing devices we don’t own never feels clean, and it rarely scales well. This article breaks down why MDM often fails with third-party access, how modern access models actually work today, and how AI-driven edge security helps teams move forward, especially in messy BYOD environments. Why MDM Falls Short for Contractors and Vendors Mobile Device Management was built for corporate-owned endpoints. It assumes long-term employees, standardized hardware, and full administrative control. None of that reflects how contractors and vendors actually work today. Common MDM challenges with third parties include: In short, forcing MDM on external users increases friction without meaningfully reducing risk. Worse, it can delay projects and push teams toward insecure workarounds. The Real Risk: Access, Not the Device Security leaders are increasingly shifting focus from device control to access control. The real question isn’t “Is this device managed?” but: Contractors typically need limited, time-bound access to specific applications, not full network visibility. Managing the entire device to solve that problem is excessive. This is why access-first security models are gaining traction. Modern Requirements for Secure Third-Party Access Securing contractors and vendors is tricky, especially if you don’t want to bloat your MDM. But some basics really help. 1. Zero Trust Access Don’t assume anything. Every access request should be checked all the time. It does not matter where the user is or what device they’re using. Trust nothing, verify everything. 2. BYOD-Friendly Controls Most contractors use their own devices. Security needs to work without invading privacy or using heavy tools. Otherwise, people just push back. 3. Context-Aware Risk Decisions Access should change based on behavior, location, device health, and session risk. Static rules aren’t enough. 4. Fast Onboarding and Clean Offboarding Contractors need access quickly. And when they leave, access should disappear automatically. No leftovers, no messy cleanup. AI-Powered Edge Security: A Cleaner, Smarter Way to Protect Access A growing number of organizations are turning to AI-driven edge security to address these challenges. Instead of pushing agents and profiles onto devices, security is enforced at the access layer. Netzilo has introduced an AI-powered edge security approach designed specifically for modern BYOD and third-party scenarios. Rather than expanding MDM, this model evaluates risk in real time and applies granular access controls without managing the entire device. Key advantages of this approach include: This aligns closely with how third-party access actually works in the real world. How AI-Powered Edge Security Reduces MDM Footprint While Keeping Systems Safe By shifting enforcement to the edge, organizations can: This model is particularly effective for vendors who rotate frequently or contractors who work across multiple clients. IT teams stay in control of access, not hardware. Aligning With Industry Security Guidance This access-first way of thinking isn’t random. It lines up with guidance from trusted US institutions like the National Institute of Standards and Technology. NIST keeps pushing zero-trust ideas for a reason. Don’t assume trust. Keep checking it all the time. Their frameworks focus more on who the user is, what they’re doing, and how risky it looks right now. Not who owns the laptop. This matters even more in hybrid and remote setups, where devices, locations, and users are all over the place. Operational Benefits for IAM and IT Ops Teams Beyond security, reducing MDM expansion delivers tangible operational gains: Security teams gain better visibility into access patterns, while IT Ops avoids becoming the support desk for non-employees. Supporting Vendor Risk Management Programs Vendor risk management is no longer just a procurement concern; it’s a security priority. An access-centric approach allows organizations to: Agencies such as the Cybersecurity and Infrastructure Security Agency (CISA) also advocate for zero trust maturity models that reduce reliance on network location and device ownership, key principles when working with external users. When MDM Still Makes Sense (And When It Doesn’t) MDM is not useless. It just gets used in the wrong places sometimes. For company-owned laptops and phones, it works fine. IT owns the device, sets the rules, and controls updates. The same goes for highly regulated roles where full device visibility is required by policy. Long-term internal employees also fit this model better. Problems start when the same approach is pushed onto contractors and short-term vendors. These people come and go. They use personal devices. Forcing MDM slows access, creates pushback, and often leads to shortcuts. That’s when risk actually grows. In these cases, access-layer security feels cleaner, lighter, and easier to manage. Final Thoughts Securing contractor and vendor access doesn’t have to mean more MDM or a worse user experience. Chasing device ownership only adds noise. What really matters is identity, context, and what’s happening in real time. When access is checked properly, critical systems stay protected without slowing people down. For teams handling nonstop third-party access and BYOD headaches, AI-driven edge security offers a cleaner way forward. It balances security, privacy, and daily operations without piling on extra tools. FAQs
Read full post on gocorptech.comMSPdb™ News

How to Spot a Phishing Email
Cybercriminals have become more sophisticated than ever, and thanks to AI, phishing emails are now harder to detect than many people realize. A phishing email is a fraudulent message designed to trick you into clicking a malicious link, opening an infected attachment, or providing sensitive information such as passwords, financial details, or login credentials. These
Cybercriminals have become more sophisticated than ever, and thanks to AI, phishing emails are now harder to detect than many people realize. A phishing email is a fraudulent message designed to trick you into clicking a malicious link, opening an infected attachment, or providing sensitive information such as passwords, financial details, or login credentials. These
Read full post on litechadvisors.com
AI Readiness Assessment: 10 Questions to Ask Before You Start
You Shouldn’t Have To Tolerate Your IT Provider
There’s a question we ask almost every business leader we meet for the first time: “How do you feel when you have to call your IT provider?” The answers are telling. Some people sigh. Some laugh. A few say something polite like “they’re fine” in a tone that means they are not fine. Nobody should
There’s a question we ask almost every business leader we meet for the first time: “How do you feel when you have to call your IT provider?” The answers are telling. Some people sigh. Some laugh. A few say something polite like “they’re fine” in a tone that means they are not fine. Nobody should
Read full post on stringfellow.com
Microsoft 365 Price Increase: What It Means for You
Microsoft has announced global price changes taking effect on July 1, 2026. Discover how these updates impact your M365 licensing, what new features are being bundled in, and how simpleroute can help you audit and optimize your IT spend to protect your bottom line.
Microsoft has announced global price changes taking effect on July 1, 2026. Discover how these updates impact your M365 licensing, what new features are being bundled in, and how simpleroute can help you audit and optimize your IT spend to protect your bottom line.
Read full post on simpleroute.com
Why AI-Generated Passwords Are a Security Risk
Are the passwords protecting your business as strong as you think they are? There’s a growing shortcut that looks clever on the surface, and feels efficient, but could weaken your security without you realizing. If you’re using AI in your business, this is something you need to understand…
Are the passwords protecting your business as strong as you think they are? There’s a growing shortcut that looks clever on the surface, and feels efficient, but could weaken your security without you realizing. If you’re using AI in your business, this is something you need to understand…
Read full post on skysailtechnologies.com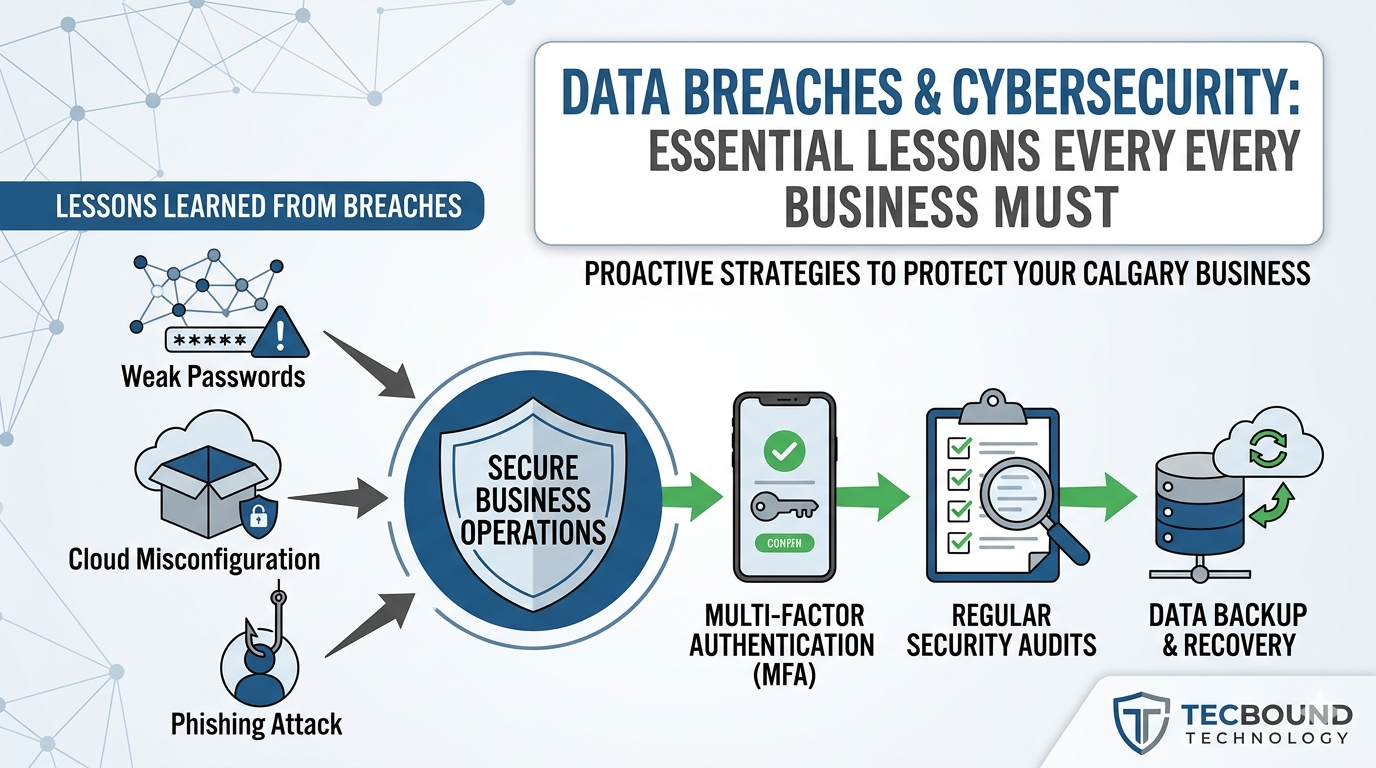
Data Breach Cybersecurity Lessons for Businesses | Tecbound
Business cybersecurity team reviewing data breach risks and prevention strategies
Business cybersecurity team reviewing data breach risks and prevention strategies
Read full post on tecbound.com
EDI Software: How to Choose the Right Solution
Originally published June 25, 2024. Completely refreshed June 1, 2026. EDI (electronic data interchange) offers powerful benefits, but you need to pick the right software solution to make EDI work for your organization. How do you choose between on-premises and cloud-based EDI software? Do you need EDI direct connect, or should you choose an EDI
Originally published June 25, 2024. Completely refreshed June 1, 2026. EDI (electronic data interchange) offers powerful benefits, but you need to pick the right software solution to make EDI work for your organization. How do you choose between on-premises and cloud-based EDI software? Do you need EDI direct connect, or should you choose an EDI
Read full post on corsicatech.com
Business Process Automation Doesn’t Manage Itself
Most businesses treat automation as a project. You identify a process, build the automation, and move on to the next thing. The work is done. But automation needs ongoing management, and that part rarely makes it into the plan. Sometimes the gap shows up immediately. IT rolls out a security update and an automation that...
Most businesses treat automation as a project. You identify a process, build the automation, and move on to the next thing. The work is done. But automation needs ongoing management, and that part rarely makes it into the plan. Sometimes the gap shows up immediately. IT rolls out a security update and an automation that...
Read full post on xpertechs.com
Cybersecurity for Venture Capital Firms: Protecting Deal Flow, Capital Movement, and Portfolio Communications
Venture capital firms rarely start the cybersecurity conversation with compliance. They start it when a partner cannot get support on the road, a capital call depends on a clean wire process, a provider misses a project deadline, or sensitive information is being passed to portfolio companies through ad hoc channels. For GPs, Managing Directors, CFOs,
Venture capital firms rarely start the cybersecurity conversation with compliance. They start it when a partner cannot get support on the road, a capital call depends on a clean wire process, a provider misses a project deadline, or sensitive information is being passed to portfolio companies through ad hoc channels. For GPs, Managing Directors, CFOs,
Read full post on coretelligent.com
The Measurably Better IT™ Management Framework: A Smarter Approach to Business Technology in Tennessee
Most businesses today depend heavily on technology, but very few have a clear framework for measuring whether their IT environment is actually helping the organization grow, stay secure, and operate efficiently.
Most businesses today depend heavily on technology, but very few have a clear framework for measuring whether their IT environment is actually helping the organization grow, stay secure, and operate efficiently.
Read full post on epion.com