How can we help you?
Discover leading Managed IT Service Providers across USA, Canada & the United Kingdom.
- 100s of leading MSPs
- Find a MSP near you
- Latest IT news for SMBs

Cybersecurity Threats in 2025: How to Protect Your Business
Cybersecurity Awareness Month is here, and 2025 is shaping up to be a pivotal year. Businesses are facing smarter, faster, and more persistent threats than ever before. Leaders who rely on capable IT support, Omaha firms especially, know how disruptive downtime or a breach can be with substandard IT support. Lincoln based firms have reported that even small lapses can create costly consequences.As the threat landscape shifts, businesses can no longer rely on yesterday's defenses to protect this year's assets. Modern attacks adapt quickly, exploiting both technical gaps and human error, making
Cybersecurity Awareness Month is here, and 2025 is shaping up to be a pivotal year. Businesses are facing smarter, faster, and more persistent threats than ever before. Leaders who rely on capable IT support, Omaha firms especially, know how disruptive downtime or a breach can be with substandard IT support. Lincoln based firms have reported that even small lapses can create costly consequences.As the threat landscape shifts, businesses can no longer rely on yesterday's defenses to protect this year's assets. Modern attacks adapt quickly, exploiting both technical gaps and human error, making cybersecurity a strategic priority at the leadership level. By layering defenses so that if one safeguard fails, others remain in place to block the attack, company leadership gains the confidence that investments in IT support directly translate into risk reduction.This year's risks demand vigilance. They require action-driven approaches to educating employees and stopping threats before they cause downtime and financial losses. From AI-assisted phishing to cloud vulnerabilities, here are the key threats shaping 2025, along with strategies to defend against them.
Read full post on coretech.usMSPdb™ News

How to Spot a Phishing Email
Cybercriminals have become more sophisticated than ever, and thanks to AI, phishing emails are now harder to detect than many people realize. A phishing email is a fraudulent message designed to trick you into clicking a malicious link, opening an infected attachment, or providing sensitive information such as passwords, financial details, or login credentials. These
Cybercriminals have become more sophisticated than ever, and thanks to AI, phishing emails are now harder to detect than many people realize. A phishing email is a fraudulent message designed to trick you into clicking a malicious link, opening an infected attachment, or providing sensitive information such as passwords, financial details, or login credentials. These
Read full post on litechadvisors.com
AI Readiness Assessment: 10 Questions to Ask Before You Start
You Shouldn’t Have To Tolerate Your IT Provider
There’s a question we ask almost every business leader we meet for the first time: “How do you feel when you have to call your IT provider?” The answers are telling. Some people sigh. Some laugh. A few say something polite like “they’re fine” in a tone that means they are not fine. Nobody should
There’s a question we ask almost every business leader we meet for the first time: “How do you feel when you have to call your IT provider?” The answers are telling. Some people sigh. Some laugh. A few say something polite like “they’re fine” in a tone that means they are not fine. Nobody should
Read full post on stringfellow.com
Microsoft 365 Price Increase: What It Means for You
Microsoft has announced global price changes taking effect on July 1, 2026. Discover how these updates impact your M365 licensing, what new features are being bundled in, and how simpleroute can help you audit and optimize your IT spend to protect your bottom line.
Microsoft has announced global price changes taking effect on July 1, 2026. Discover how these updates impact your M365 licensing, what new features are being bundled in, and how simpleroute can help you audit and optimize your IT spend to protect your bottom line.
Read full post on simpleroute.com
Why AI-Generated Passwords Are a Security Risk
Are the passwords protecting your business as strong as you think they are? There’s a growing shortcut that looks clever on the surface, and feels efficient, but could weaken your security without you realizing. If you’re using AI in your business, this is something you need to understand…
Are the passwords protecting your business as strong as you think they are? There’s a growing shortcut that looks clever on the surface, and feels efficient, but could weaken your security without you realizing. If you’re using AI in your business, this is something you need to understand…
Read full post on skysailtechnologies.com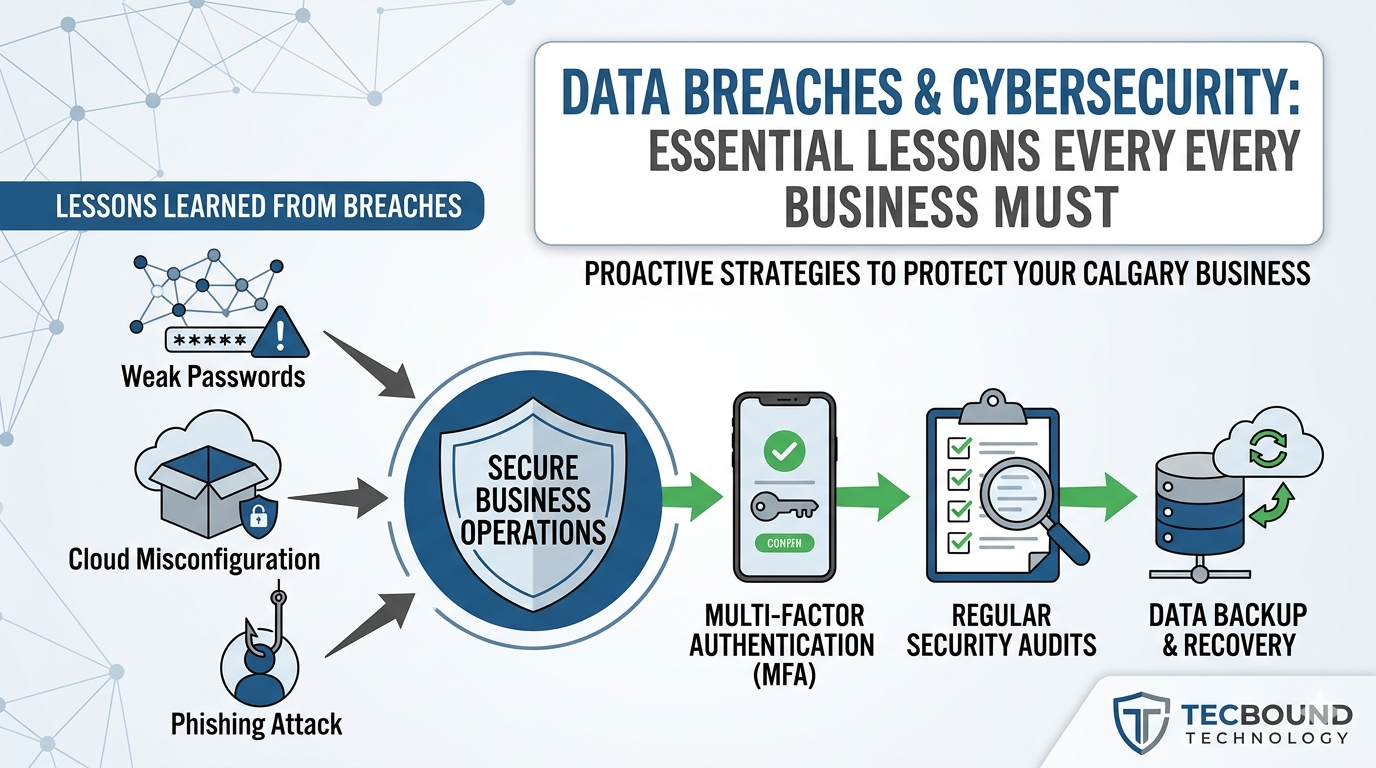
Data Breach Cybersecurity Lessons for Businesses | Tecbound
Business cybersecurity team reviewing data breach risks and prevention strategies
Business cybersecurity team reviewing data breach risks and prevention strategies
Read full post on tecbound.com
EDI Software: How to Choose the Right Solution
Originally published June 25, 2024. Completely refreshed June 1, 2026. EDI (electronic data interchange) offers powerful benefits, but you need to pick the right software solution to make EDI work for your organization. How do you choose between on-premises and cloud-based EDI software? Do you need EDI direct connect, or should you choose an EDI
Originally published June 25, 2024. Completely refreshed June 1, 2026. EDI (electronic data interchange) offers powerful benefits, but you need to pick the right software solution to make EDI work for your organization. How do you choose between on-premises and cloud-based EDI software? Do you need EDI direct connect, or should you choose an EDI
Read full post on corsicatech.com
Business Process Automation Doesn’t Manage Itself
Most businesses treat automation as a project. You identify a process, build the automation, and move on to the next thing. The work is done. But automation needs ongoing management, and that part rarely makes it into the plan. Sometimes the gap shows up immediately. IT rolls out a security update and an automation that...
Most businesses treat automation as a project. You identify a process, build the automation, and move on to the next thing. The work is done. But automation needs ongoing management, and that part rarely makes it into the plan. Sometimes the gap shows up immediately. IT rolls out a security update and an automation that...
Read full post on xpertechs.com
Cybersecurity for Venture Capital Firms: Protecting Deal Flow, Capital Movement, and Portfolio Communications
Venture capital firms rarely start the cybersecurity conversation with compliance. They start it when a partner cannot get support on the road, a capital call depends on a clean wire process, a provider misses a project deadline, or sensitive information is being passed to portfolio companies through ad hoc channels. For GPs, Managing Directors, CFOs,
Venture capital firms rarely start the cybersecurity conversation with compliance. They start it when a partner cannot get support on the road, a capital call depends on a clean wire process, a provider misses a project deadline, or sensitive information is being passed to portfolio companies through ad hoc channels. For GPs, Managing Directors, CFOs,
Read full post on coretelligent.com
The Measurably Better IT™ Management Framework: A Smarter Approach to Business Technology in Tennessee
Most businesses today depend heavily on technology, but very few have a clear framework for measuring whether their IT environment is actually helping the organization grow, stay secure, and operate efficiently.
Most businesses today depend heavily on technology, but very few have a clear framework for measuring whether their IT environment is actually helping the organization grow, stay secure, and operate efficiently.
Read full post on epion.com